
Cybersecurity specialists warn users over a new threat emerging — Borat RAT. The new malware shows multifunctional capabilities of incredible specter.
During their regular OSINT research specialists from Cyble Research Labs came across a very unusual Remote Access Trojan (RAT) named Borat.
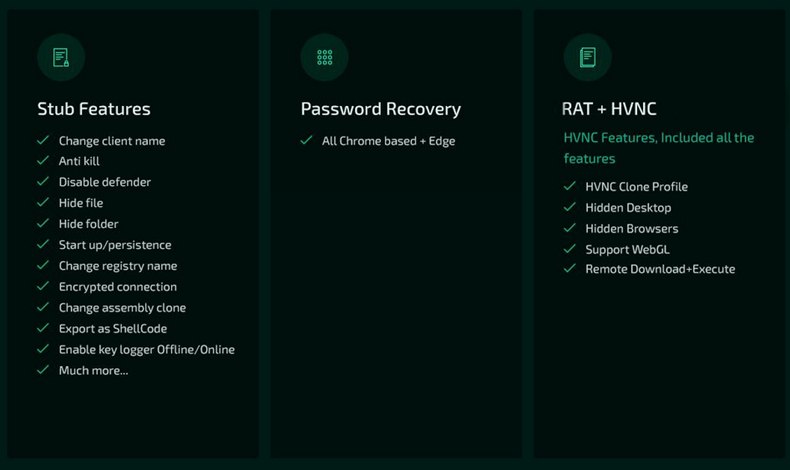
The interesting thing about this malware is that it provides not only the traditional RAT features but also further expanding the malware capabilities by including DDOS services, Ransomware.
It’s name the malware got after a black comedy mockumentary film “Borat”. Threat actors also put the photo of Sacha Baron Cohen as a “cover page” who played the role of Borat in the same named film.
Technical details of Borat RAT
Threat actors use RAT or Remote Access Trojan to obtain remote control and full access on a user’s system among other things mouse and keyboard control,network resources access and files access.
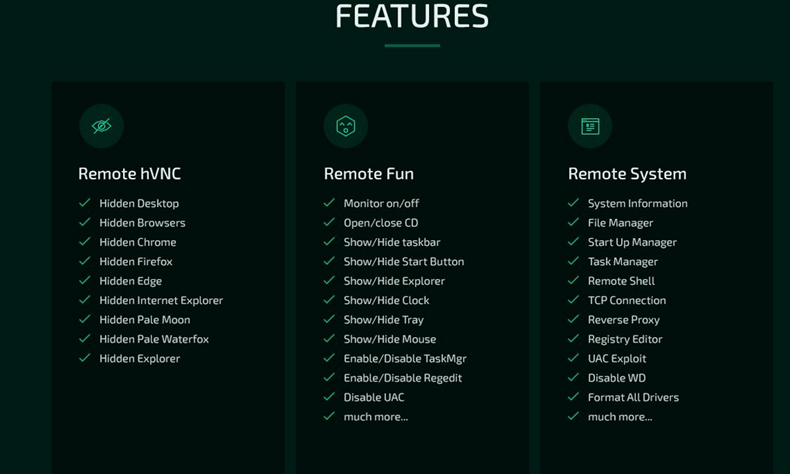
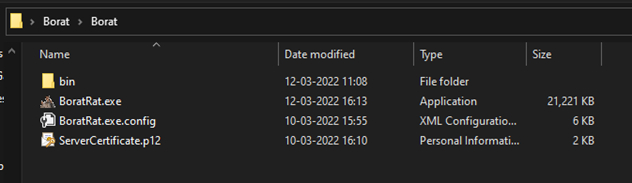
The Borat Rat is a package of server certificate, supporting modules and builder binary, etc. The malware has a dashboard to help to perform RAT activities and also provides an option for compiling the malware binary to perform DDoS and ransomware attacks on the victim’s machine.
So what can the thing do?
Remote Activities with Borat RAT
To scare and distract the victim the RAT will perform: Blank screen, Monitor Off, Hang System, Enable/Disable webcam light, Hold Mouse, Show/hide the taskbar, Show/hide the Desktop, Swap Mouse Buttons, Play Audio.
Discord Token Stealing
The RAT steals Discord tokens and sends the stolen token information back to the threat actors.
Browser Credential Stealing
Borat steals saved login credentials, bookmarks,history and cookies from Chromium based browsers such as Edge, Google Chrome, etc.
Hollowing Process
With the help of this RAT threat actors can use a hollowing process which means injection of malicious code into legitimate processes.
[caption id="attachment_56424" align="aligncenter" width="790"] Borat RAT Dashboard
Borat RAT DashboardDevice Information Collection
The Borat RAT also collects various information on the victim’s machine including System Model, OS Version, OS Name, etc.
Reverse Proxy
Borat RAT also allows attackers to hide their identity in communication with the compromised servers. This malware has code that enables the reverse of the proxy to perform RAT activities anonymously.
Remote Desktop
The malware performs the remote desktop of the victim’s machine. It gives the threat actors the necessary rights to control the victim’s keyboard, mouse, machine and capture the screen. With the control of the victim’s machine, threat actors can perform execution of a ransomware in the compromised machine, deletion of the files.
Webcam and Audio Recording
Borat RAT can also try to find a webcam or microphone and if any of these are present it will start the secret recording saving everything in the designated fold.
DDOS
The malware has the capabilities to disrupt the normal traffic of a targeted server as well.
Ransomware
The interesting fact for the cybersecurity specialist is that this malware has an option to encrypt the victim’s files and subsequently demand a ransom. Typically for the ransomware it also has the capability to create a ransom note on the victim’s machine.
Keylogger
The Borat’s module “keylogger.exe” monitors and stores the keystrokes on the victim’s machine. They are then saved in a file called “Sa8XOfH1BudXLog.txt” for subsequent exfiltration.
Specialists’ Recommendations
To help users avoid the threat of a newly appeared trojan they prepared several tips to follow:
- Make regularly backups of your files and keep them offline better on a separate network;
- Don’t open untrusted email attachments or links without first checking their authenticity;
- Use antivirus software on any connected device including mobile, laptop and PC;
- Enable the automatic updates on your devices whenever it is possible and practical;
- Use strong passwords and enable multi-factor authentication wherever it is possible and practical;
- It’s better not to keep the important files in common locations like My Documents, Desktop.
What is so special about Borat RAT?
The fresh malware strain apart from typical advanced trojan functionality has a series of modules which are capable of launching various types of malicious activities. In comparison to its namesake character from a movie this malware is not “verrry nice” — one of the most popular catchphrases of fictional Borat.
“Malware authors are increasingly developing feature sets and capabilities that allow flexibility on the part of the attacker,” John Bambenek, principal threat hunter at Netenrich, a digital IT and security operations company, writes in an email to Threatpost.
In the same email the researcher adds that he doesn’t see that much of a threat coming from this “Pandora Box” of malware. He explains that usually such types of tools are used by less sophisticated cybercriminals or those pretending to be one. In any way they may find it difficult to succeed at ransomware at scale. As one security professional noted, this malware might have been created just to monetize on the newcomers in the cybercriminal world who just don’t know their ways yet.
Analysts will keep an eye on Borat RAT
The Cyble Research Team will continue to observe the RAT’s actions and will update the community on the situation evolving. The Borat RAT presents itself to be a unique and potent combination of Remote Access Trojan, Spyware and Ransomware making it triple the threat to the compromised machine. Its capabilities of recording audio and controlling the webcam while conducting traditional info stealing behavior asks to keep a close eye on it. To add here the DDOS and ransomware capabilities asks even more attention.
As Jack Mannino, CEO at nVisium noted, ransomware and DDoS attacks are a constant threat to the organizations. The severity of such attacks can be amplified by security bugs and flaws within the software itself.
These attacks are exceptionally effective can be launched at a relatively low cost. Therefore, DDoS and ransomware threats will remain to be a persistent risk for organizations around the world. And this new malware strain Just adding to the ever growing and evolving cybercriminal ecosystem.
