
If you ever wondered how much those hackers guys earn you might take a glimpse now. On February 27, 2022 a Twitter account named @ContiLeaks and many others similar accounts started to post quite juicy details about the underworld money and employees.
“I know you, you know me, we know us”
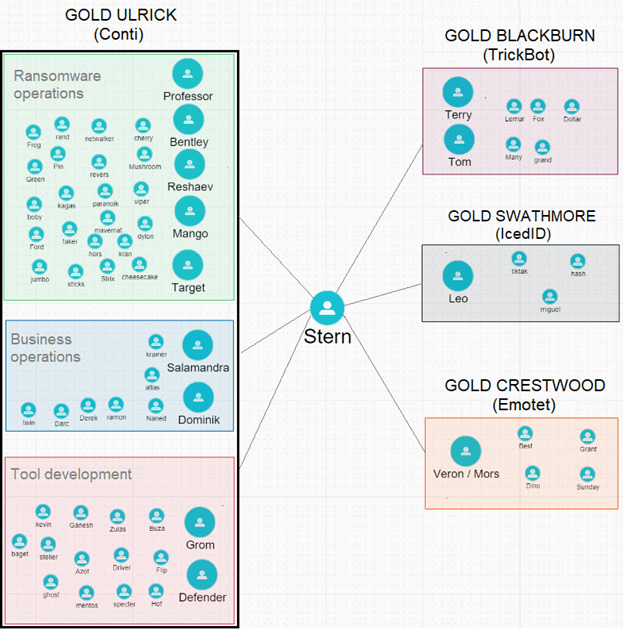
The leaks mainly concern Gold Blackburn and Gold Ulrick and in more than 160,000 messages reveal communications exchanged among nearly 500 threat actors in the period between January 2020 and March 2022. In addition there were leaked source code and tool repositories; quite a fact to open the lid over previously unknown threat actors.
for now stern/deamon – try to hide himeself, changing nicknames, wants to make some voice calls 🙂 reshaev/cyberganster – in total panic. tramp – doing somethings unknown! We know everything about you Conti, go to panic, you can even trust your gf , we against you!
— conti leaks (@ContiLeaks) March 19, 2022
Among the other leaked data were also dozens of dossiers on many threat actors with citizenship information, passport, bank account numbers, phone numbers, addresses, names, photos. Cybersecurity specialists can’t determine the motives of the doers so far but they assume it could possibly be that some threat actors do not agree with pro Russian statements Gold Ulrick posted on its leak site. Their identity is not known as well.
What are Gold Ulrick and Gold Blackburn?
Most of the leaked data concerns two different but highly collaborative threat groups. They got their identification names from Secureworks® Counter Threat Unit™ (CTU) researchers who observed the activity referenced in the leaked data to be linked to Gold Blackburn and Gold Ulrick threat groups.
Gold Ulrick, a financially motivated cybercrime group, has been active since mid-2018. The group operated Ryuk ransomware from August 2018 until early 2021 and Conti ransomware from early 2020. They only target organizations with their ransomware.
Gold Blackburn, also a financially motivated cybercrime group, that has been active since June 2014. Trickbot malware, Buer Loader, Zloader, Anchor, BazarLoader all belong to the authorship of this group.
As being mentioned these are highly different threat groups but they show no less level of collaboration. CTU researchers observed operators of Conti and Ryuk ransomware to use BazarLoader, TrickBot or another malware payload issued by the Gold Blackburn threat group. Cobalt Strike Beacon and PowerShell Empire command and control (C2) servers used in the attacks conducted by the threat groups shared TrickBot and that could possibly be a sign of a single entity maintaining infrastructure for both. Which shows clearly one of the numerous close friendship signs among them.
But other threat groups have also used the malware like LockBit, Maze and RansomExx (also known as 777).
What has been revealed in Conti ransomware leak?
The leaked messaged as we said shone a light onto the underworld economy also revealing some previously unknown resources.
Having observed the leaked material, cyber security specialists made several assumptions about what has been leaked and what the specialists in their field could take from the information.
“Stern” persona has been mentioned the most in the revealed messages. This account seems to be interacting with a wide circle of underworld employees making them the presupposed leader. According to messages this account makes key organizational decisions, manages crises, communicates with other threat groups and gives out payroll.
“Stern” persona also oversees ransomware distribution and BazarLoader, TrickBot operations. With such a wide list of responsibilities this reveals this account as the possible leader of both Gold Ulrick and Gold Blackburn.
In the messages were also mentioned the representatives of other threat groups and they were actively communicating with the “Stern” persona and other presupposed members of Gold Ulrick and Gold Blackburn as well. Among them: Gold Swarthmore (IcedID),Gold Mystic (LockBit), Gold Crestwood (Emotet). But researchers warn that despite its connection to many groups mentioned, they can’t make suggestions that this person leads all the groups.
One of the conclusions researchers could make out of the leaks was that it certainly showed the mature well organized criminal ecosystem involving many threat groups. Simply, they don’t work alone but help each other; you can even say it’s some kind of Evil Corporation that grew out in the underworld.
My comments are coming from the bottom of my heart which is breaking over my dear Ukraine and my people. Looking of what is happening to it breaks my heart and sometimes my heart wants to scream.
— conti leaks (@ContiLeaks) March 1, 2022
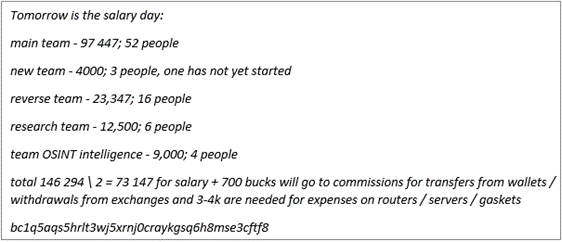
One of the messages that picked exceptionally the researchers interest, thoroughly a practical one, is the salary of cybercriminals. Yes, of course, Evil Corporation offers you paid leave, sick leave and many bonuses. From one leaked message we learn that on average individuals earn approximately $1,800 USD per month.
The salary exceeds the average Russian salaries of approximately $540 USD per month. As of July 1, 2021 the mentioned Bitcoin address at the bottom of the messages has received 2.31 bitcoins ( which amounts to approximately $80,000 USD at that time).
Statistics on ransomware
If you surprised by the fact that there’s actually a whole Evil Corporation exist then read the following stat on ransomware prepared by researchers from Purplesec to understand the actual scope this particular kind of cyber crime has taken:
- Cybersecurity specialists estimated that every 14 seconds a business falls victim to a ransomware;
- In 2019 with ransomware attacks increase of 41% 205,000 businesses lost access to their files;
- Cybersecurity specialists detected 68,000 new ransomware Trojans for mobiles in 2019;
- As of 2019, the number of new ransomware variants grew in 46%;
- Social actions, such as phishing made up 21% of ransomware infection cases;
- The volume of phishing emails that contain ransomware payload increased by 109% over 2017;
- In 2021 ransomware operators made the biggest known ransom demand of $100 million;
- As of Q2 2021 (up 64% year-over-year) 121 ransomware incidents have been reported;
- In 2021 ( increased by 82% year over year) the average ransomware payment made up nearly $570,000.
Reading all this stat you can imagine there’s more than one Evil Corporation and the sums climbing up the sky.
