
In its press release Volvo Cars, a Swedish multinational manufacturer of luxury vehicles headquartered in Torslanda, Gothenburg reported about the illegal access of its file repositories by a third party. After the discovery of the breach, the company notified relevant authorities and undertook measures to prevent further access to its property. Immediately with the news of the data breach, shares in Volvo Cars fell down to 3.2% at 1555 GMT. In fact the company’s IPO on Oct. 29 made up the biggest in Europe this year.
Volvo Cars plan to fully rebrand itself by 2030
According to Wikipedia in March this year, the company made an announcement of rebranding to a fully electric cars` manufacturer by 2030. In June 2021, Swedish battery developer and manufacturer Northvolt and Volvo Cars made public their intention to start a 50/50 joint venture that would be made up of development and research (R&D) center and battery gigafactory. In December 2021, a statement revealed that the battery R&D center would be located in Gothenburg, Sweden.
“Volvo Cars is conducting its own investigation and working with third-party specialists to investigate the property theft. The company does not see, with currently available information, that this has an impact on the safety or security of its customers’ cars or their personal data,” goes in a press release issued by a company.
The investigation showed that only a limited amount of the company’s R&D property has been accessed in the course of the intrusion. The information discovered under investigation indicates that there may be some impact on the company’s operation. Although there is no indication that security and safety of its customers’ personal data or cars have been endangered.
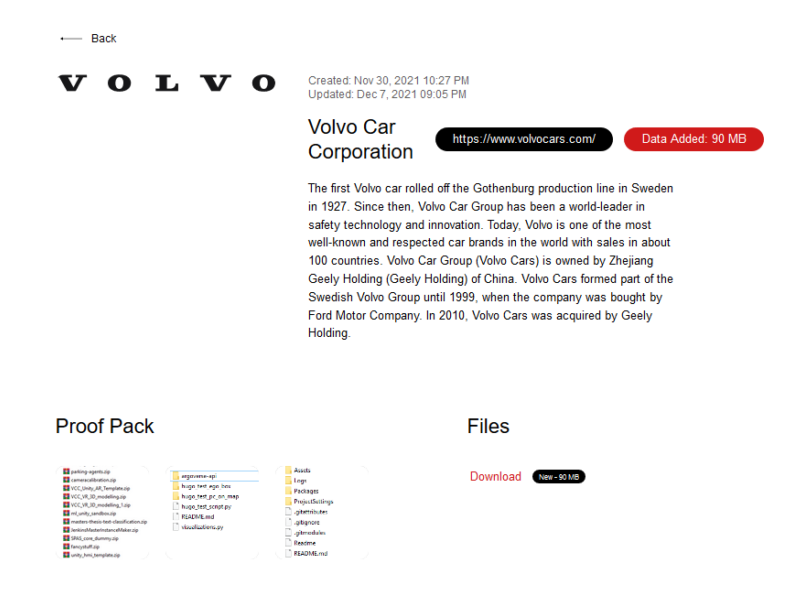
Snatch ransomware seems to show responsibility for the attack. In the proof of the attack the threat actors leaked 35.9 MB of documents that they claim to have been stolen. Samples that Snatch gang published on their site contained among others firmware components. And in addition it also contained the source code of various Volvo internal apps. Besides all were mostly written in Python. Though the company in media communication did not confirm the gang`s involvement.
Threat actors involved denied their connections to Snatch ransomware
Snatch ransomware targets its victims by booting Windows PCs in Safe Mode. Subsequently it allows for the malware to avoid detection by security protections that do not work in such a mode. However, threat actors involved denied any connections to the Snatch ransomware. Threat actors added they do not demand a ransom to decrypt data. In addition they shared that the work will be exclusively with acquired data.
Specialists point out that threat actors used RDP tools for lateral movement across the network. In such a case they recommend for organizations to use strong passwords which were not reused elsewhere. And they should more often monitor RDP connections for brute force attacks.
