
With the IoT world growing rapidly the cybersecurity experts take more time to investigate this particular field of technology. Recently researchers from Sentinel Lab published a report of their findings on discovered vulnerabilities in Microsoft Azure for IoT devices that allow for remote code execution.
Which vulnerabilities have been found?
Last year researchers from Sentinel Lab discovered a few vulnerabilities in Microsoft Azure’s Defender for IoT devices. And some of them were rated as critical, scoring CVSS score of 10.0.
First time the security specialist from Sentinel Lab reported the vulnerabilities to Microsoft was in June 2021. The company immediately issued the patches to all discovered vulnerabilities. There’s currently no evidence that these vulnerabilities have been exploited in the wild.
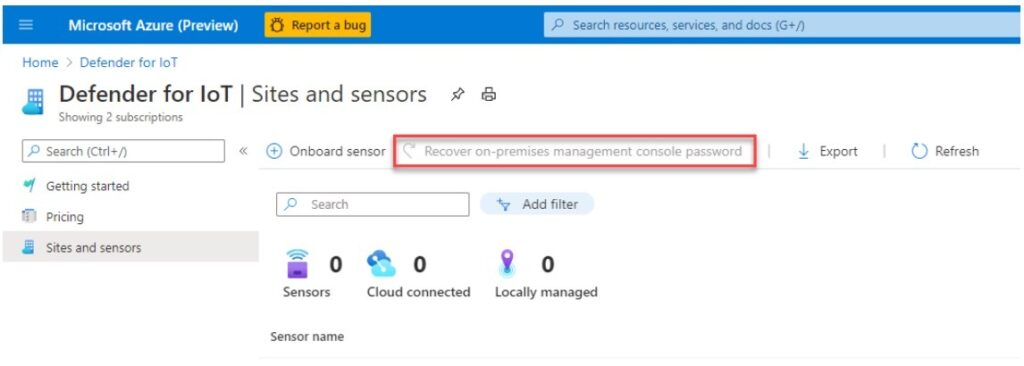
According to the published report an unauthorized attacker can remotely exploit the device protected by Microsoft Azure Defender for IoT by taking advantage of the vulnerabilities found in Azure’s Password Recovery mechanism. The vulnerabilities affect both on cloud and on premises customers.
The discovered vulnerabilities received the following identifications : CVE-2021-42311, CVE-2021-42313, CVE-2021-37222, CVE-2021-42312 and CVE-2021-42310. Cybersecurity specialists urge users to take immediate actions.
In the case of a successful attack the exploitation may lead to full network compromise.
In addition to mitigating the potential threat, cybersecurity specialists also advise users of the products affected to revoke any privileged credentials deployed to the platform and check access logs for any irregularities.
What is Microsoft Azure Defender For IoT?
Microsoft Defender for IoT is a security solution to use both on premise and in the cloud. It does continuous IoT/OT asset discovery, manages vulnerabilities and threat detection while not requiring changes to existing environments.
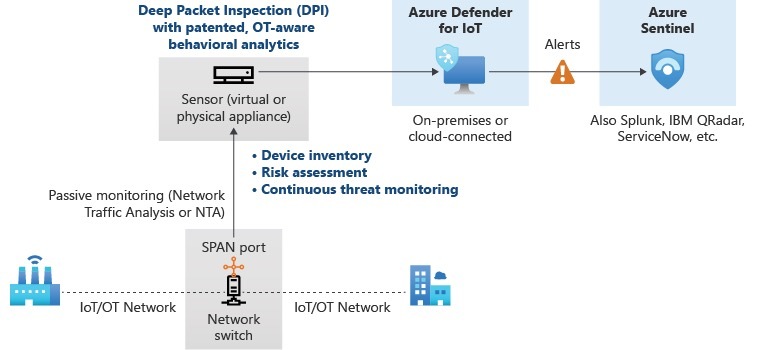
This passive network layer security consists of two main components:
- Microsoft Azure Defender For IoT Sensor – continuously discovers and monitors the devices on the network;
- Microsoft Azure Defender For IoT Management – helps SOC teams to analyze and manage data collected from multiple IoT devices. In a single dashboard SOC specialists can also oversee if the networks are safety-secured.
Users can install both components either on an appliance or VM.
The attack surface of the Microsoft Azure vulnerabilities
Cybersecurity specialists say that the reason that both components share nearly the same codebase makes them prone to the same vulnerabilities.
For the exploitation of these vulnerabilities potential threat actors will use a web interface that will allow them to control the targeted environment in an easy way. Additionally the sensors provide the attack surface with its DPI service (horizon) that parses the network traffic.
Defender for IoT is a product (known formerly as CyberX) was acquired by Microsoft in 2020.
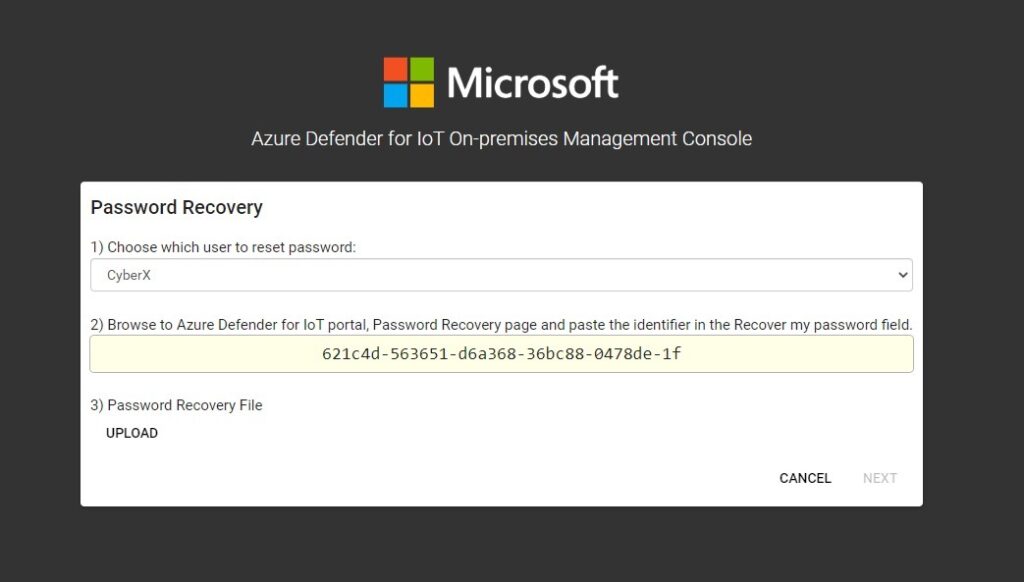
For the exploitation of both components, the threat actor will use Azure’s Password Recovery Mechanism for the first step of an attack.
The password recovery mechanism works the same for sensor and management. Here, manipulating it, the threat actor will get a new password and thus obtain the internal access into an account.
To understand how exactly the exploitation of this mechanism will work the cybersecurity specialists explain that the password recovery mechanism consists of two main components:
- The Java web API (tomcat, internal);
- The Python web API (external).
And that’s where they say it introduces a time-of-check-time-of-use (TOCTOU) vulnerability because no synchronization mechanism is applied.
Saying shortly, the exploit script will perform the TOCTOU attack to reset and receive the password of the account detouring authentication.
After obtaining internal access to the account the threat actor gets a more vast attack surface. For the next vulnerability the cybersecurity researchers found is a simple command injection vulnerability inside the change password mechanism.
The remaining vulnerabilities are basic SQL Injections and the other is the vulnerability in the traffic processing framework.
If you are interested in a more detailed description of the vulnerabilities you can also read an original report prepared by Sentinel Lab.
How to secure your IoT devices?
If you use any IoT device you definitely need to know the basic IoT device cybersecurity hygiene. It’s easy to imagine that with all kinds of IoT devices nowadays this part of our homes can pose no less threat than the compromise of a computer or phone.
The most obvious device in your home that should be protected the most is the wifi router. Saying metaphorically it’s the doorway of your smart home. So to have it secure comes to be one of the first priorities.
To talk about the ways to enable the safeness of IOT devices they will be the next:
Employing a Next-Generation Firewall (NGFW)
Generally your router will have a built in firewall but often it is not enough. Traditional firewalls don’t have more needed security features like virtual private network (VPN), QoS management, SSL/SSH interception, content filtering, malware protection, an intrusion prevention system (IPS).
Of course, a next-generation firewall (NGFW) is quite expensive thing but if you can afford to buy an IoT device what are those extra money to spend on their safety? NGFW will combine traditional firewall with more robust security functionalities to help you secure your privacy.
Enabling Multi-Factor Authentication
Probably you know what multifactor authentication is? It’s the way to additionally secure your device by enabling to have the second proof of identify such as like a one-time pin (OTP) or a code/ email sent to confirm that the person trying to log into is really you.
Some IoT devices have the multifactor authentication by default but others don’t. The case might be that your IoT device has multifactor authentication with its associated mobile app but you can also use third-party service like Google Authenticator to help with additional security of IoT devices.
Keeping Your Devices Up-To-Date
Some wifi routers don’t update automatically so check often if there’s any pending updates for your device. In some cases these updates can have significant security patches so make a habit to regularly check the thing. The same rule applies to IoT devices and their apps. Don’t procrastinate with this, do straightaway.
Disabling Features You Don’t Use
The rule is simple if you don’t use, for example, the voice control on your smart tv, it’s better to disable it. Or you only use your wifi home’s connection, disable the remote access. When you block those unused features you block the many entry points that potentially could get hacked.
Creating a Separate Wi-Fi Network for IoT Devices
In many modern wifi routers a user can set up a guest (or secondary) network. So basically creating it you protect your main network from any threats arisen from the compromised IoT device.
The last pieces of advise will be some basic cybersecurity hygiene tips like use strong and unique password, change default name of your wifi router. Look for what encryption you have. It should be WPA2. Because if it’s WPA or WEP protocols it’s time for a change.
