
Check Point Research (CPR) reports over a new kind of malware distributed via Microsoft’s official store. The new threat is capable of taking control over social media accounts on SoundCloud, Google and Facebook.
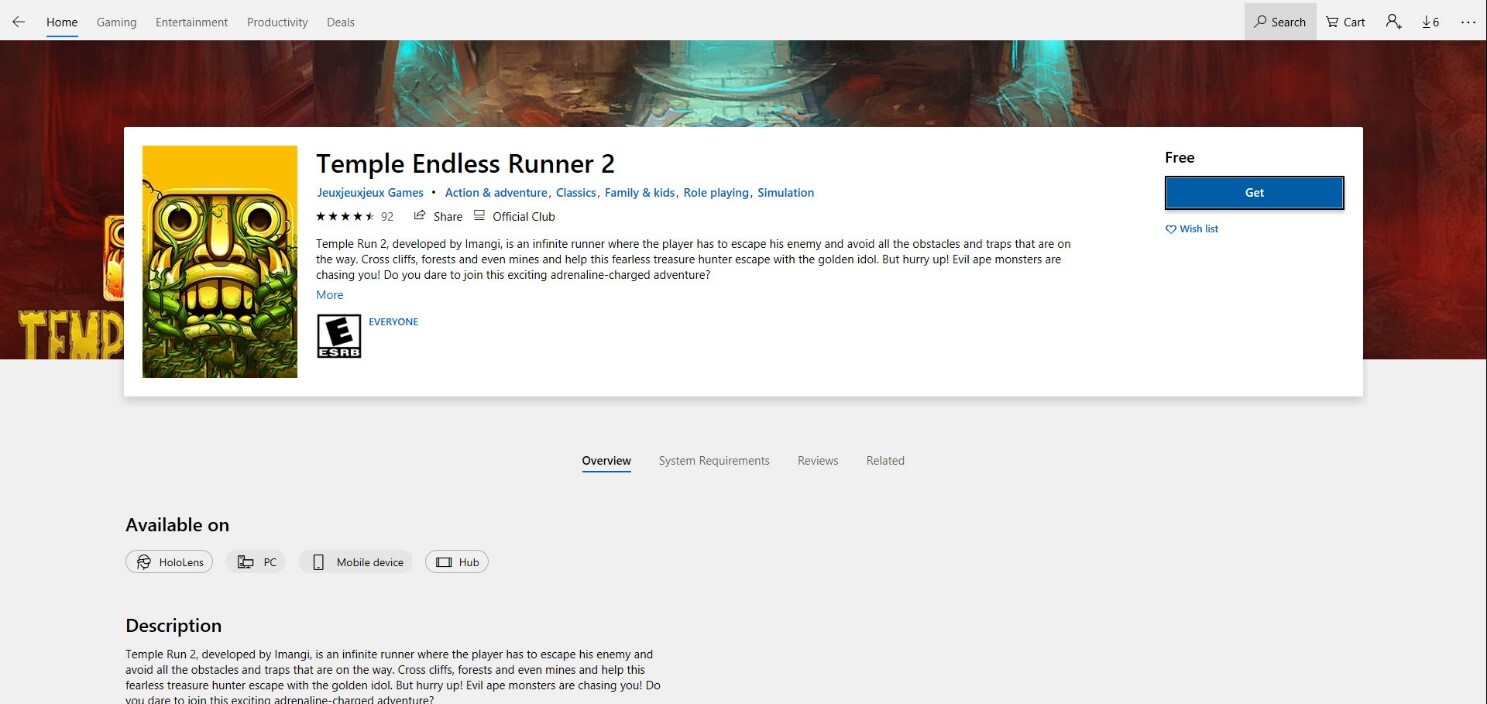
The researchers report that malware has already infected over 5000 active devices worldwide. It shows the ability to register new accounts, log in, make comments and even “like” other posts. Threat actors used such popular games as “Subway Surfer” and “Temple Run” to disperse the malware.
Subsequently they can use it as a backdoor gaining full control on the victim’s machine. Most victims targeted by the Electron Bot were from Sweden, Bermuda, Spain, Bulgaria and Russia.
What is Electron Bot malware?
CPR has already reported to Microsoft the found malware and all detected game publishers who are behind the campaign. The name of the malware researchers from CPR based on the last campaign’s C&CdomainElectron-Bot[.]s3[.]eu-central-1[.]amazonaws.com. The malware which is a modular SEO was used for click fraud and social media promotion.
The attackers began their malicious activity as an ad click campaign at the end of 2018. Back at that time the malware was hiding behind an app called “Album by Google Photos” in the Microsoft Store pretending to be the legitimate product of Google LLC. Over the years the malware received significant updates like new features and techniques. These days threat actors mainly distribute it via the Microsoft store platform, dropping from dozens of infected applications ( which in most cases are games). They also don’t forget to regularly upload it.
The malware uses the Electron framework that imitates human browsing behavior and evades website protections. Electron is a framework designed for building cross-platform desktop applications that use Web scripts. It combines Node.js runtime and Chromium rendering engine allowing for itself to have the capabilities of a browser which is controlled by scripts, for example JavaScript.
Electron Bot capabilities
To avoid detection threat actors load the malware dynamically at run time from their servers. Such actions allow them to change the bots’ behavior and modify the malware’s payload at any time. Researchers described the next main capabilities of the Electron Bot:
- It promotes online products generating profits with ad clicking or with the increase of store rating for higher sales;
- It promotes social media accounts, for example SoundCloud and YouTube, directing traffic to specific content and increasing views and ad clicks for profits generation;
- It is also an ad clicker, a computer virus that will run in the background constantly connecting to remote websites and thus generating clicks for ads. Threat actors will receive their profit based on how many times the ad was clicked;
- SEO poisoning, malicious method where threat actors using search engine optimization tactics create malicious websites that will show up specifically first in search results. Threat actors also use this method in terms of service to promote other websites ranking.
How does Electron Bot infect its victims?
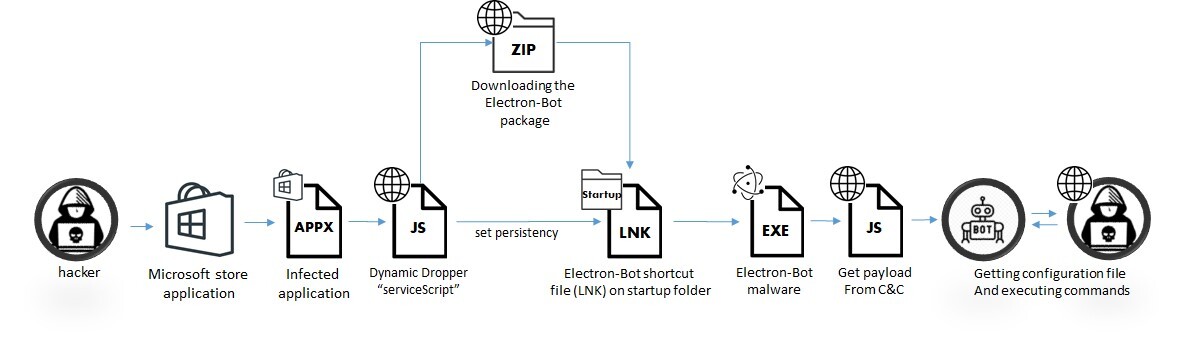
Researchers describe the infection chain for the malware as usual for such a kind. It starts with the installation of an infected application that the user downloads from the Microsoft Store.
When the user launches the game, a JavaScript dropper loads dynamically in the background from the attackers’ server. After that several actions are being executed and among them downloading and installing the malware and gaining persistence on the startup folder.
When it comes to malware at the next system startup it launches. The malware also establishes connection with the C&C and subsequently receives a dynamic JavaScript payload with a set of capability functions. At the very end of the malicious process setup the C&C sends the configuration file containing commands to execute.
How to avoid malware infection?
The researchers note that for now the malware doesn’t engage in any high risk activities on infected machines but it would be wise to know how to avoid the infection at all. Electron Bot can also serve for threat actors as a dropper for RAT or even ransomware. In addition it uses all of the computer resources, including GPU computing.
It is a usual thing for users to believe in the safety of the apps with at least some number of reviews. But one looking for an app might actually oversee the importance. We will repeat this once more: it is not enough for an app to be regarded legit and trusted solely because it has some number of reviews.
You need to look for differences in those reviews. Basically they should be read like the ones written by real people. It might not be a difficult task to do to see if a user puts themselves in the shoes of a real user.
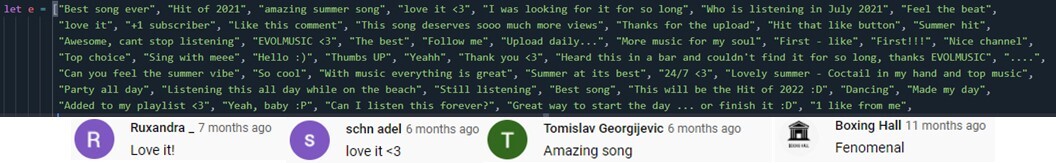
Just think of your hypothetical review of the app you have been working with for extensive time. Whatever comes into your mind might be the example of a normal review by a real person.
In the end of their new threat review article researchers from CPR added a few safety tips on how to avoid getting infected with such and similar kinds of malware. And they will be the following:
- Before deciding on downloading a desired app look carefully for the namings of it. Does it read the same as you know the original naming of this app is?
- It’s better not to download an app with a relatively small number of reviews. A something 100 reviews or less for an app like some messenger somehow should alert you;
- The general rule is that the reviews should be consistent, good and reliable.
In addition to these tips you can also check the publisher of the app and look for some info on it on the internet. If it’s something shady you will most likely get the expected result.
