
On November 24, 2021 SafeBreach Labs published research on a new Iranian threat actor using a Microsoft MSHTML Remote Code Execution (RCE) exploit for targeting victims with a new PowerShell stealer or PowerShortShell. ShadowChasing first reported the case on their Twitter page. However specialists could not get the PowerShell Stealer hash/code as it was not available on public malware repositories or elsewhere.
hi threat
why did you use it 😀
ITW:858404225565c80972ba66d2c612e49f
filename:جنایات خامنه ای.docx
URL:
hxxp://hr.dedyn.io/word.html
hxxp://hr.dedyn.io/word.cab
hxxp://hr.dedyn.io/1.ps1
hxxp://hr.dedyn.io/upload.aspx?fn=
hxxp://hr.dedyn.io/upload2.aspx pic.twitter.com/fHsgAshCNc— Shadow Chaser Group (@ShadowChasing1) September 15, 2021
In their research SafeBreach Labs described the analysis of the PowerShortShell full attack chain, and gave details of phishing attacks which started in July this year. Most importantly they managed to acquire the PowerShell Stealer code which researchers named PowerShortShell. In their own words the reason for such name lies in the structure of the script, it contained little more than 150 lines. But nevertheless researchers say the PowerShell script allowed an attacker to gain access to a wide range of information: telegram files, screen captures and the victim’s environment.
“Almost half of the victims are located in the United States. Based on the Microsoft Word document content – which blames Iran’s leader for the “Corona massacre” and the nature of the collected data, we assume that the victims might be Iranians who live abroad and might be seen as a threat to Iran’s Islamic regime,” SafeBreach Labs wrote in their research.
In their attacks, the threat actor exploited CVE-2021-40444 vulnerability. It is a Microsoft Office MSHTML Remote Code Execution Vulnerability that allows no macros and requires only a single approval to “display content”. Researchers think that the campaign might be linked with Iran’s Islamic regime because of the Telegram surveillance usage. Rampant Kitten, Infy and Ferocious Kitten, Iran’s threat actors, also used it. Interestingly, here threat actors applied quite exclusive usage of exploits because most of the Iranian threat actors generally do social engineering tricks.
The attack itself consisted of two steps
The attack itself consisted of two steps: first phishing and the subsequent spamming with malicious attachments. The two phishing attacks started in July 2021 when threat actors collected credentials for Instagram and Gmail. For this matter they used the same C2 server Deltaban[.]dedyn[.]io. Attackers masqueraded this phishing HTML page as the legit deltaban.com travel agency. A click on which would transfer the victim to an Iranian short URL:https://yun[.]ir/jcccj. This URL would then direct you to signin[.]dedyn[.]io/Social/Google_Finish. One registered the domain in July 2021.
The threat actors dumped phished credentials to file out.txt which anyone could just browse. The second phishing campaign involved Instagram. Here the credentials also went to the same out.txt file. All the phishing and C2 and infection server originated from 95.217.50.126.

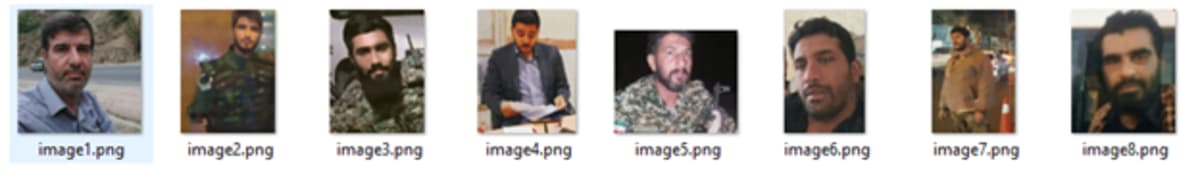
The exploit attack in its turn started on September 15, 2021. A victim received an email with a Winword document in Farsi. The first document titled Mozdor.docx. included images of Iranian soldiers. The second one with a title جنایات خامنه ای.docx (Khamenei Crimes.docx) said: “One week with Khamenei; Complain against the perpetrators of the Corona massacre, including the leader”. It also had attached links to the Iranian news site and Twitter account of an IranWire journalist.
The Word files would connect to the malicious server, execute the malicious html, and then drop a dll to the %temp% directory. The mozdor.docx file included an exploit in the file document.xml.rels. It executed mshtml:http://hr[.]dedyn[.]io/image.html, while the second docx executed mshtml:http://hr.dedyn.io/word.html. The exfiltration of the Telegram files was done to “https://hr.dedyn.io/upload2.aspx”. Researchers could not find the victims of the attacks but they constructed the victims heat map based on the available data. Most cases specialists registered in the United States, Russian Federation and Netherlands.
