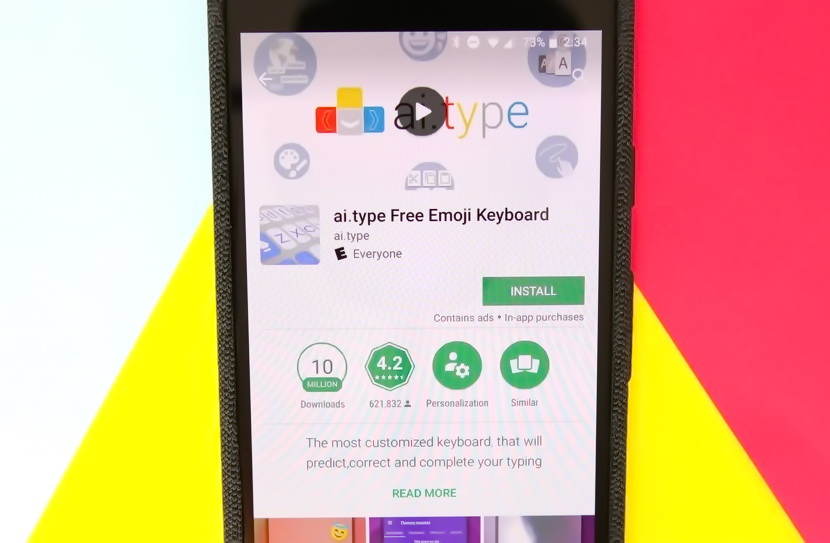
Secure-D and Upstream Systems experts found that ai.type, a popular Android keyboard, was infected with malicious code, and users could lose about $18 million because of this.
Recalling, discovery of malware as part of the application was first reprorted last summer.Then, experts revealed on Google Play many applications infected with a clicker trojan, among which was ai.type installed more than 40 million times.
“The app has been delivering millions of invisible ads and fake clicks, while delivering genuine user data about real views, clicks and purchases to ad networks. Ai.type carries out some of its activity hiding under other identities[1], including disguising itself to spoof popular apps such as Soundcloud”, — write Upstream Systems experts.
Now, Secure-D and Upstream Systems experts are warning that even after uninstalling from Google Play, the application has remained active on millions of devices and is still available in other, unofficial application stores. Although the activity of the malware decreased, unfortunately, it did not stop completely.
The problem is that the trojan can not only engage in advertising and promoting other applications on Google Play, but can also quietly load any sites, including those with advertising (including video) or other dubious content.
Read also: xHelper “undeletable” Trojan infected 45,000 Android devices
It is reported that to date, Upstream Systems analysts have detected and blocked more than 14,000,000 suspicious requests for transactions originating from 110,000 unique devices onto which the ai.type keyboard was loaded.
If these requests were not blocked, purchase of premium digital services happened without victim’s notification, which in total would cost users about $18,000,000.
“Ai.type contains software development kits (SDKs) with hardcoded links to ads and subscribes users to premium services without their consent. These SDKs navigate to the ads via a series of redirections and automatically perform clicks to trigger the subscriptions. This is committed in the background so that normal users will not realize it is taking place”, — explains Head of Secure-D at Upstream, Dimitris Maniatis.
Suspicious activity of this kind was recorded in 13 countries, but was especially high in Egypt and Brazil.
Recommendations:
Upstream is advising all consumers who have downloaded ai.type to check their phones for unusual behavior. Users should regularly check their phones and remove any reported malware. They should also check their bills for unwanted or unexpected charges for accessing premium data services and to look out for signs of increased data usage which could indicate a malicious app is consuming data in the background.
