
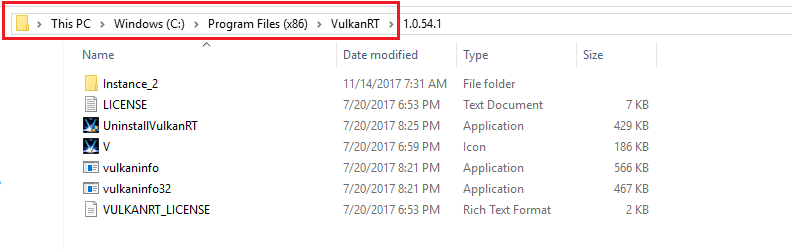
VulkanRT is a strange folder you can spectate in the system partition of your PC, as well as in the list of installed apps. Some people think that it is malicious, but, in fact, you have nothing to worry about.
VulkanRT, or Vulkan Runtime Libraries, is a legitimate graphics API that is at the beginning of its popularity. Being designed as a substitution for “old” DirectX and OpenGL standards, Vulkan is declared a more efficient and more flexible solution for 3D graphics. It was first introduced in 2016, and nowadays, in 6 years, a lot of game developers have released alternative versions of their games for Vulkan. Cross-platform allows that API to be used on Windows, macOS and Linux.
Is VulkanRT safe?
Sure, it is 100% normal to see one on your disk. Spectating this means that you have one of the games or programs installed on your PC using Vulkan as a graphical interface API. For the correct functioning of these applications, it is recommended to keep that thing on your disk. The negative impact of its removal can start from a long process of downloading and installing this API back, and up to fatal error at the program start.
Red Dead Redemption, Rainbow Six Siege, Fortnite, War Thunder, Half-Life: Alyx – these and a lot of other names use this API to render the 3D graphics to you. Some of them can be doubled on different APIs (for example, War Thunder is present for OpenGL, DX, and Vulkan). However, having the article subject means that you use exactly the Vulkan variant. In normal situations, you must not see any unpleasant effects from its presence. Its processes, just like with any of the APIs, are not displayed in the Task Manager.
Do I need to choose Vulkan apps?
Vulkan is considered to be a successor of OpenGL, however, it does not squeeze it out of the market. This API is generally faster, consumes less CPU/GPU resources, and offers a wider range of different functions. Exactly, a lot of modern games, including the aforementioned, were released exclusively on Vulkan. Nonetheless, as it always happens with new things, there are several concerning elements.
This API is an open-source project that is developed voluntarily. The official number of programmers who work on Vulkan is 170 people, but there are also a lot of community activists who offer their own fixes for that library. And all these people work for donations – without any real salary or other monetary motivation. That leads to the fact that Vulkan is not so ideal in various apps – and especially in the programs which require the shells like Wine or Proton.

Vulkan is probably the future of 3D modeling APIs, but it is still under development and is not so great these days. Only high-budget projects can boast of a great implementation – generally, because of the ability to pay their programmers regularly.
I am not certain about the VulkanRT instance on my computer. What should I do?
There were almost no cases when the name of any other element of the identity of VulkanRT was counterfeited for malicious purposes. But nothing stops cybercriminals from doing so. Possibly, your uncertainty is justified, and you have got a very rare malware sample that has Vulkan’s name. Thus, I’d advise you to scan your computer with anti-malware software.
To keep your computer clean, it is recommended to have your antivirus updated as often as possible. GridinSoft Anti-Malware can offer you database updates every hour. Together with the Proactive protection feature, this will let you forget about any malicious activity on your PC.

Follow the steps in the slider explaining how to use GridinSoft Anti-Malware.
- Step 1. Download GridinSoft Anti-Malware. Click on its installer in the left-bottom section of your browser.
- Step 2. Allow changes to be made via User Account Control.
- Step 3. Click on “Install” to install the program.
- Step 4. Wait until the program is fully installed into your PC.
- Step 5. Click on “Finish“.
- Step 6. Run the program. Wait until scanning is completed and all malware is detected.
- Step 7. Click on “Clean Now“
- Step 9. Click on “Protect“. Make sure that Internet Security mode is enabled.
