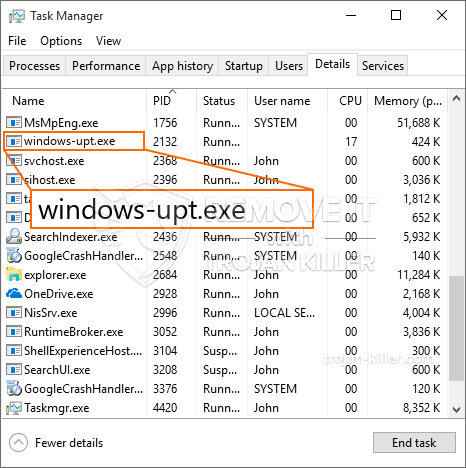
A brand-new, extremely dangerous cryptocurrency miner virus has been spotted by safety scientists. The malware, called Windows-upt.exe can contaminate target victims using a variety of ways. The main point behind the Windows-upt.exe miner is to employ cryptocurrency miner activities on the computer systems of victims in order to acquire Monero symbols at targets cost. The result of this miner is the elevated electricity bills and if you leave it for longer amount of times Windows-upt.exe may also harm your computer systems elements.
Windows-upt.exe: Distribution Methods
The Windows-upt.exe malware utilizes 2 preferred methods which are utilized to infect computer targets:
- Payload Delivery through Prior Infections. If an older Windows-upt.exe malware is released on the victim systems it can instantly upgrade itself or download and install a newer version. This is possible by means of the built-in upgrade command which gets the release. This is done by linking to a specific predefined hacker-controlled server which provides the malware code. The downloaded and install infection will acquire the name of a Windows service and be put in the “%system% temp” area. Vital residential properties and operating system configuration documents are changed in order to allow a relentless and also quiet infection.
- Software Vulnerability Exploits. The latest variation of the Windows-upt.exe malware have actually been found to be brought on by the some ventures, widely understood for being used in the ransomware attacks. The infections are done by targeting open services using the TCP port. The strikes are automated by a hacker-controlled structure which looks up if the port is open. If this condition is met it will certainly scan the solution as well as retrieve information regarding it, including any variation and arrangement information. Exploits and also prominent username and password combinations may be done. When the manipulate is activated versus the vulnerable code the miner will certainly be deployed along with the backdoor. This will certainly present the a double infection.
In addition to these methods various other strategies can be used as well. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like way and depend upon social engineering methods in order to puzzle the victims into thinking that they have gotten a message from a legit service or company. The infection documents can be either directly affixed or placed in the body components in multimedia content or text web links.
The wrongdoers can likewise develop malicious touchdown pages that can pose vendor download and install pages, software application download sites and also other frequently accessed places. When they make use of comparable appearing domain to legit addresses and also safety and security certifications the users may be coerced right into interacting with them. Sometimes merely opening them can cause the miner infection.
Another strategy would certainly be to make use of haul service providers that can be spread utilizing those approaches or through documents sharing networks, BitTorrent is just one of the most preferred ones. It is regularly used to disperse both genuine software program as well as documents and pirate material. 2 of the most popular haul service providers are the following:
Various other methods that can be taken into consideration by the bad guys consist of the use of web browser hijackers -unsafe plugins which are made compatible with the most prominent web browsers. They are uploaded to the pertinent repositories with fake customer testimonials and developer credentials. In a lot of cases the summaries may include screenshots, video clips as well as sophisticated descriptions promising terrific function improvements as well as performance optimizations. However upon installation the behavior of the affected web browsers will certainly alter- individuals will certainly discover that they will certainly be redirected to a hacker-controlled landing web page and their settings could be altered – the default home page, internet search engine as well as brand-new tabs page.
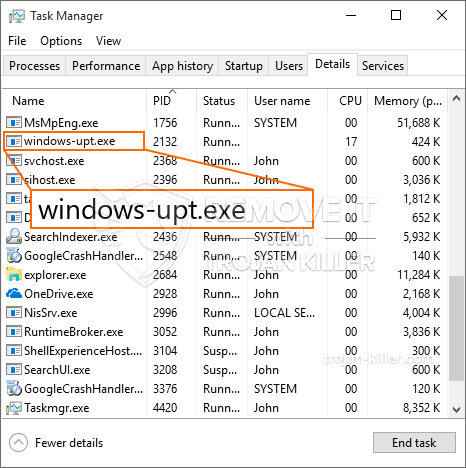
Windows-upt.exe: Analysis
The Windows-upt.exe malware is a traditional case of a cryptocurrency miner which relying on its arrangement can trigger a wide range of harmful activities. Its main goal is to do intricate mathematical tasks that will certainly make use of the readily available system resources: CPU, GPU, memory and hard disk space. The means they work is by attaching to an unique server called mining pool from where the called for code is downloaded. As soon as one of the jobs is downloaded it will be begun simultaneously, numerous instances can be gone for as soon as. When a given task is completed another one will be downloaded in its area and the loophole will certainly proceed until the computer system is powered off, the infection is removed or an additional similar occasion happens. Cryptocurrency will be awarded to the criminal controllers (hacking group or a solitary cyberpunk) directly to their wallets.
A hazardous feature of this group of malware is that examples similar to this one can take all system sources and almost make the victim computer unusable up until the threat has actually been completely removed. Most of them feature a relentless setup which makes them really difficult to remove. These commands will certainly make modifications to boot choices, setup documents as well as Windows Registry values that will certainly make the Windows-upt.exe malware begin immediately when the computer system is powered on. Access to recuperation food selections as well as options might be blocked which renders numerous manual removal overviews virtually useless.
This particular infection will certainly configuration a Windows service for itself, adhering to the conducted protection analysis ther complying with actions have actually been observed:
During the miner operations the linked malware can hook up to already running Windows services and also third-party installed applications. By doing so the system administrators may not observe that the source load originates from a different procedure.
| Name | Windows-upt.exe |
|---|---|
| Category | Trojan |
| Sub-category | Cryptocurrency Miner |
| Dangers | High CPU usage, Internet speed reduction, PC crashes and freezes and etc. |
| Main purpose | To make money for cyber criminals |
| Distribution | Torrents, Free Games, Cracked Apps, Email, Questionable Websites, Exploits |
| Removal | Install GridinSoft Anti-Malware to detect and remove Windows-upt.exe |

These kind of malware infections are especially reliable at accomplishing sophisticated commands if set up so. They are based upon a modular structure allowing the criminal controllers to orchestrate all sort of hazardous actions. One of the preferred examples is the adjustment of the Windows Registry – adjustments strings associated by the os can create severe performance interruptions and also the failure to accessibility Windows solutions. Relying on the extent of modifications it can additionally make the computer completely pointless. On the various other hand adjustment of Registry values coming from any third-party set up applications can sabotage them. Some applications might stop working to introduce altogether while others can suddenly quit working.
This certain miner in its current variation is concentrated on extracting the Monero cryptocurrency containing a customized variation of XMRig CPU mining engine. If the projects show successful then future versions of the Windows-upt.exe can be released in the future. As the malware uses software application vulnerabilities to contaminate target hosts, it can be part of an unsafe co-infection with ransomware and also Trojans.
Elimination of Windows-upt.exe is strongly recommended, since you take the chance of not just a huge electricity bill if it is operating on your COMPUTER, but the miner may additionally execute other unwanted tasks on it and also even damage your PC completely.
Windows-upt.exe removal process
STEP 1. First of all, you need to download and install GridinSoft Anti-Malware.
STEP 2. Then you should choose “Quick scan” or “Full scan”.
STEP 3. Run to scan your computer
STEP 4. After the scan is completed, you need to click on “Apply” button to remove Windows-upt.exe
STEP 5. Windows-upt.exe Removed!
Video Guide: How to use GridinSoft Anti-Malware for remove Windows-upt.exe
How to prevent your PC from being reinfected with “Windows-upt.exe” in the future.
A Powerful Antivirus solution that can detect and block fileless malware is what you need! Traditional solutions detect malware based on virus definitions, and hence they often cannot detect “Windows-upt.exe”. GridinSoft Anti-Malware provides protection against all types of malware including fileless malware such as “Windows-upt.exe”. GridinSoft Anti-Malware provides cloud-based behavior analyzer to block all unknown files including zero-day malware. Such technology can detect and completely remove “Windows-upt.exe”.







