Cybercriminals attack vulnerable Jira and Exim servers in order to infect them with the new version of Linux-Trojan Watchbog and Monero cryptocurrency mining.
Watchbog is a malicious software for infecting Linux-based servers by operating vulnerable software, such as Jenkins, Nexus Repository Manager 3, ThinkPHP or Linux Supervisord.According to a researcher from Intezer Labs, the latest version of the malware exploits the newly discovered template injection vulnerability (template injection) in Jira (CVE-2019-11581), which allows executing remote code.

The malware also exploits a RCE vulnerability in Exim (CVE-2019-10149), which allows attackers to execute commands with root permissions.
According to the Shodan search, there are currently more than 1,610,000 vulnerable Exim servers on the network, as well as over 54,000 vulnerable Atlassian JIRA servers.
“The fact that the Jira CVE-2019-11581 template injection vulnerability these attackers are targeting has been publicly disclosed just 12 days ago stands as proof to the speed at which threat actors are starting to abuse new security flaws”, — conclude Bleepingcomputer journalists.
Having exploited the vulnerabilities, Watchbog uploads a crypto-miner to extract Monero currency and takes steps to maintain its presence on the system. In particular, it adds itself to several crontab files to reinfect the system if the user deletes one of these files.
Extracted currency is sent to:
47k2wdnyyBoMT6N9ho5Y7uQg1J6gPsTboKP6JXfB5msf3jUUvTfEceK5U7KLnWir5VZPKgUVxpkXnJLmijau3VZ8D2zsyL7
During the campaign, attackers managed to get 53 XMR (approximately $4503).
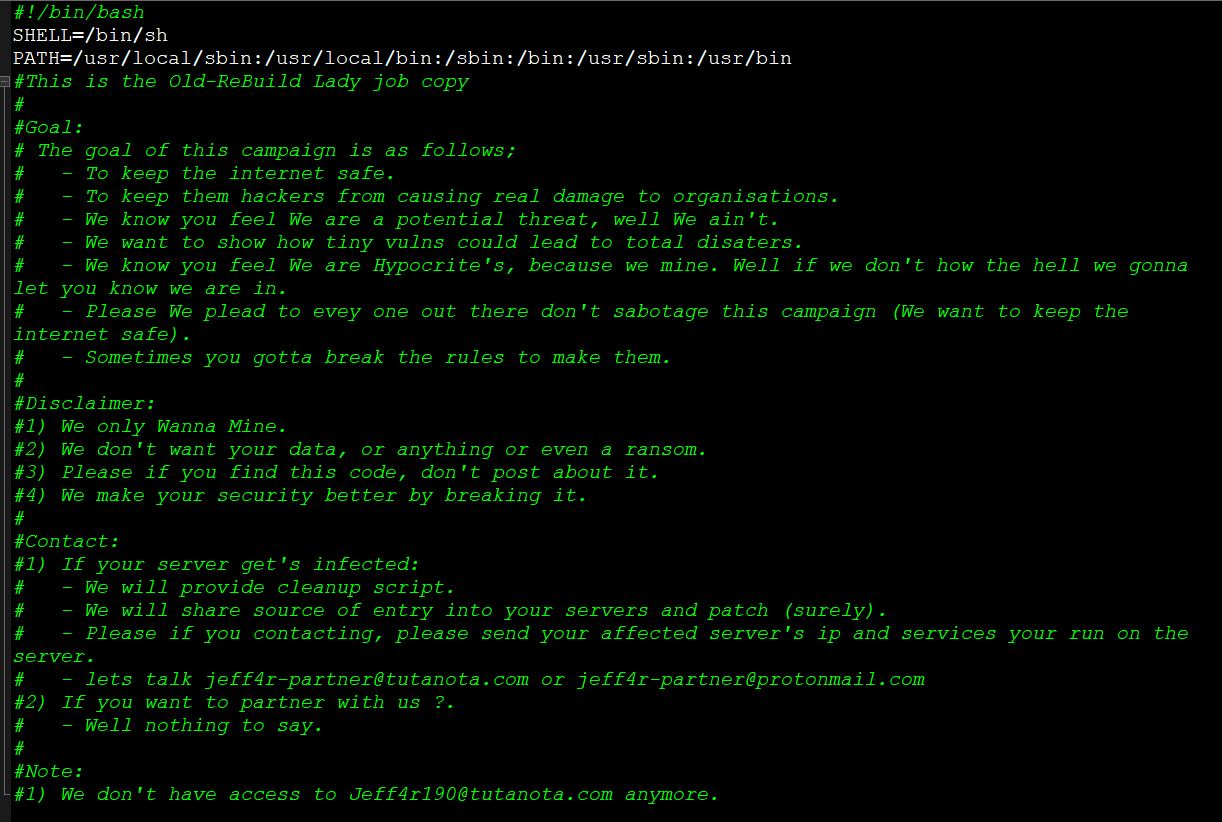
One of the distinguishing features of this campaign is that the malware leaves a message to its victims, according to which the motive of the intruders is “Internet security”.
What makes it highly dangerous is that this variant is not detected by any of the scanning engines on VirusTotal.
But, according to the Watchbog operators, the malware is intended only for mining cryptocurrency, and they have no intention to modify the data stored on the servers or demand a ransom.
