
Researchers at Anomali Threat Research have discovered a new eCh0raix encryptor written in Go. The malware attacks the QNAP NAS devices and encrypts the victims files.
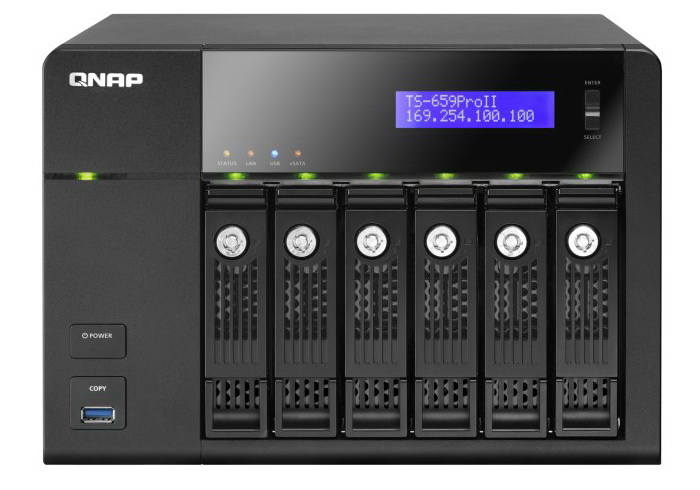
Unfortunately, by now there is no way to decrypt the data without paying the ransom to the attackers.Experts report that compromise of devices is mainly carried out by brute force weak credentials and the use of known vulnerabilities. So, in the forums of the publication BleepingComputer, users complained about hacking QNAP NAS: QNAP TS-251, QNAP TS-451, QNAP TS-459 Pro II and QNAP TS 253B.
Although the control server for the cryptographer is located in Tor, eCh0raix does not contain a Tor client. Instead, malware operators created a SOCKS5 proxy, through which ransomware communicates with the managing server.
In addition, authors of the malware seem to have developed a special API that can be used to query various information. For example, experts noticed that ransomware connected to the URL http://sg3dwqfpnr4sl5hh[.]Onion/api/GetAvailKeysByCampId/10 to get the public encryption key based on the campaign identifier (in this case, campaign number 10). It is not entirely clear whether these identifiers are associated with personal campaigns of virus creators or their partners.
Having penetrated a vulnerable device, eCh0raix first performs a language check to determine if the device belongs to certain countries (Belarus, Ukraine or Russia). For devices from these countries, ransomware will not encrypt files. If the attack continues, the malware searches for and eliminates the following processes using the
service stop %s
or
systemctl stop %s
commands. Where “%s” can be:
- apache2
- httpd
- nginx
- mysqld
- mysqd
- php-fpm
The ransomware then encrypts Microsoft Office and OpenOffice documents, PDF files, text files, archives, databases, photos, music, video, and image files. After that, the attackers demand a ransom from the victim in the amount of 0.05-0.06 BTC or more.
The researchers point out that most QNAP NAS devices do not have an active antimalware solution, which allows eCh0raix freely encrypting data. Worse, even if an anti-virus product is present on the device, the malware is unlikely to be detected: according to VirusTotal, so far only three of the 55 security products are able to notice the coder.
Interestingly, at the same time with Anomali, the same malware was discovered and studied by Intezer specialists, giving it the name QNAPCrypt. Although, overall, Intezer analysts came to the same conclusions as their colleagues, they also noticed that each victim of the cryptographer received the unique address of a bitcoin wallet for sending a ransom. Moreover, it turned out that QNAPCrypt encrypts devices only after the management server has allocated them the wallet address and the RSA public key.
Soon, Intezer researchers found that the list of such wallets was created in advance and is static (that is, the number of wallets is limited), and the attackers’ infrastructure does not perform any authentication when new devices are connected to it, reporting on their infection.
The experts decided to take advantage of this nuance and staged a DoS attack on malware operators. Imitating the infection of almost 1,100 devices, the researchers quickly exhausted the supply of unique Bitcoin wallets intruders. As a result, the malicious campaign was temporarily disrupted, because the information on the infected devices is encrypted only after assigning the purse to the infected NAS.
Unfortunately, the authors of the virus finally coped with the DoS-attack of experts and updated the code of their malware, making it look like Linux.Rex. To counter the attack of specialists, hackers placed the RSA key and information about the static wallet inside the executable file, which is delivered to the target machines.
