A Swiss PRODAFT Threat Intelligence (PTI) Team recently published a report on their findings that relate to one of the most notorious cybercriminal gangs in the world. The team managed to get access to Conti`s infrastructure and obtained the real IP addresses of their servers. The report gives insights on how the Conti ransomware gang works, how many targets they have already attacked and more.
Conti ransomware suffered data leakage
“We strongly believe that this report will serve as an important medium for understanding inner workings of high-profile ransomware groups such as Conti, especially for the purpose of creating more efficient cooperation and remediation strategies by all authorized public and private officials,” PRODAFT Threat Intelligence (PTI) Team wrote at their site with a pdf file of a report attached.
Conti is particularly known to be quite a ruthless cyber criminal gang which indiscriminately will target hospitals, police dispatchers and emergency service providers. They often won’t provide a decryption key to victims even when the payment is made. This particular ransomware group often makes headlines with it`s high-profile targets and large sums they subsequently demand.
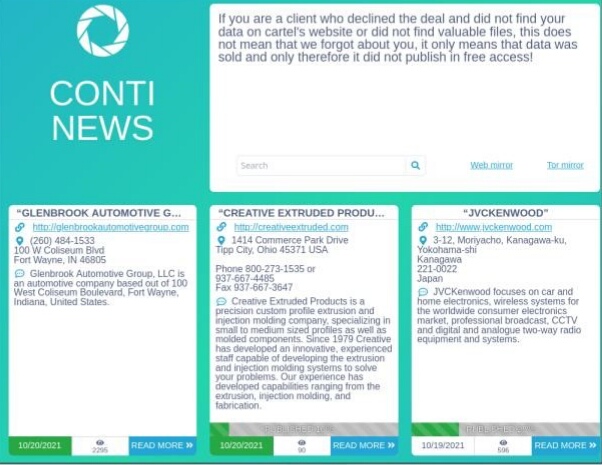
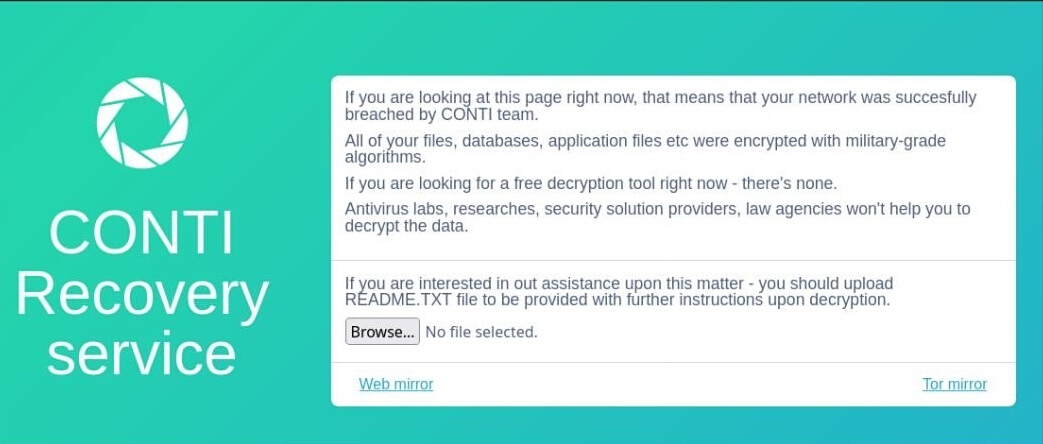
Conti ransomware ( a.k.a. Wizard Spider, Ryuk and Hermes) is a malicious program that stops users from accessing their data unless the victims pay a ransom. Conti automatically scans networks for profitable targets, expands through the network, and encrypts every device and account it can detect. Unlike similar ransomware variants, Conti ransomware works as a ransomware-as-a-service (RaaS) business model. That means that there are ransomware developers who sell or lease their ransomware technologies to affiliates. The affiliates in their turn use that technology to conduct ransomware attacks.
First time the Conti ransomware group was detected in October 2019. Since then the gang upgraded to a ransomware variant known as Conti v3.0. As the group works as an RaaS affiliate model it actively recruits new members. On 05.08.2021 it seems one of such affiliates leaked Conti`s team data. It exposed the group`s training materials, guides, internal documents and much more. Something like this happens in the affiliate business model. A user named m1Geelka made the accusations that the group mistreated them in regard to money.
Cyber criminal gang uses up-to-date security exploits
Conti ransomware is constantly evolving in it`s attack pattern. They use up-to-date security exploits such as FortiGate and PrintNightmare, which are known exploits with already available official patches. Many users still have not applied the patches and the gang successfully manipulates this fact. As Conti operates as the RaaS service model it gives the gang an immense flexibility in terms of how to conduct an attack. Conti`s affiliates apply wide range of methods and among them:
Among those, phishing is by far the most common one. Another common method includes mass vulnerability scanning. That’s when automated bots check publicly exposed networks for known vulnerabilities. Conti affiliates also use high-end Malware-as-a-Service technologies such as BazarLoader, Trickbot and Emotet for the purposes of distributing Conti ransomware.
The report finishes with the detailed description of Conti`s Management Panel, statistics on the group`s activity and how the gang manages their money flow.