A new, extremely harmful cryptocurrency miner infection has been spotted by protection scientists. The malware, called Srvan6.exe can contaminate target victims making use of a range of means. The main point behind the Srvan6.exe miner is to use cryptocurrency miner tasks on the computer systems of sufferers in order to get Monero tokens at targets expense. The outcome of this miner is the raised power bills and if you leave it for longer periods of time Srvan6.exe might also harm your computer systems components.
Srvan6.exe: Distribution Methods
The Srvan6.exe malware utilizes two prominent approaches which are used to infect computer targets:
- Payload Delivery through Prior Infections. If an older Srvan6.exe malware is released on the sufferer systems it can automatically upgrade itself or download and install a more recent version. This is possible using the integrated upgrade command which acquires the launch. This is done by connecting to a certain predefined hacker-controlled server which offers the malware code. The downloaded virus will certainly obtain the name of a Windows service as well as be placed in the “%system% temp” location. Vital buildings and operating system configuration documents are altered in order to allow a consistent and also silent infection.
- Software Vulnerability Exploits. The most recent version of the Srvan6.exe malware have actually been discovered to be brought on by the some ventures, popularly recognized for being made use of in the ransomware assaults. The infections are done by targeting open services using the TCP port. The attacks are automated by a hacker-controlled structure which searches for if the port is open. If this condition is satisfied it will check the solution and get details regarding it, consisting of any kind of version as well as setup data. Ventures as well as prominent username as well as password mixes may be done. When the exploit is triggered against the at risk code the miner will certainly be deployed together with the backdoor. This will certainly present the a double infection.
In addition to these techniques other approaches can be used too. Miners can be distributed by phishing e-mails that are sent in bulk in a SPAM-like way and rely on social engineering techniques in order to confuse the sufferers right into thinking that they have actually obtained a message from a reputable solution or company. The infection data can be either directly attached or inserted in the body contents in multimedia material or text web links.
The wrongdoers can additionally develop harmful landing web pages that can pose supplier download pages, software application download websites as well as various other frequently accessed places. When they utilize comparable sounding domain names to legit addresses and security certifications the individuals might be coerced right into connecting with them. In some cases just opening them can activate the miner infection.
An additional technique would be to use payload service providers that can be spread out making use of the above-mentioned techniques or by means of data sharing networks, BitTorrent is one of one of the most preferred ones. It is regularly made use of to disperse both genuine software application and data as well as pirate material. Two of the most prominent haul providers are the following:
Various other approaches that can be taken into consideration by the offenders consist of the use of internet browser hijackers -unsafe plugins which are made suitable with the most popular web browsers. They are uploaded to the pertinent repositories with phony user evaluations and designer credentials. Oftentimes the summaries might consist of screenshots, videos as well as fancy summaries promising fantastic attribute enhancements and efficiency optimizations. However upon installation the habits of the affected web browsers will alter- individuals will certainly find that they will certainly be redirected to a hacker-controlled landing page as well as their setups might be modified – the default home page, search engine and also brand-new tabs web page.
Srvan6.exe: Analysis
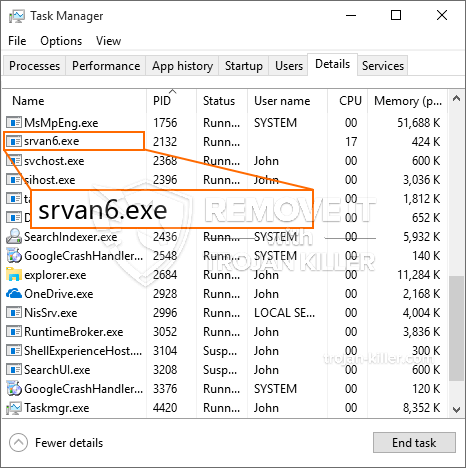
The Srvan6.exe malware is a traditional instance of a cryptocurrency miner which relying on its setup can trigger a variety of harmful activities. Its main goal is to carry out complicated mathematical jobs that will take advantage of the available system resources: CPU, GPU, memory as well as hard drive room. The way they operate is by linking to a special web server called mining swimming pool where the called for code is downloaded and install. As quickly as one of the tasks is downloaded it will be begun at the same time, numerous circumstances can be gone for as soon as. When a given task is finished one more one will certainly be downloaded in its area and also the loop will proceed until the computer is powered off, the infection is eliminated or one more comparable event happens. Cryptocurrency will be compensated to the criminal controllers (hacking team or a single hacker) straight to their purses.
A dangerous quality of this classification of malware is that examples such as this one can take all system resources and virtually make the victim computer system unusable until the danger has been totally eliminated. Most of them include a relentless installment which makes them truly hard to remove. These commands will certainly make adjustments to boot alternatives, arrangement files as well as Windows Registry values that will certainly make the Srvan6.exe malware begin instantly as soon as the computer system is powered on. Accessibility to recuperation menus and also alternatives might be obstructed which renders several hands-on elimination overviews practically pointless.
This specific infection will configuration a Windows service for itself, complying with the conducted security evaluation ther following activities have actually been observed:
. During the miner operations the associated malware can attach to already running Windows services as well as third-party mounted applications. By doing so the system managers may not see that the resource tons comes from a separate process.
| Name | Srvan6.exe |
|---|---|
| Category | Trojan |
| Sub-category | Cryptocurrency Miner |
| Dangers | High CPU usage, Internet speed reduction, PC crashes and freezes and etc. |
| Main purpose | To make money for cyber criminals |
| Distribution | Torrents, Free Games, Cracked Apps, Email, Questionable Websites, Exploits |
| Removal | Install GridinSoft Anti-Malware to detect and remove Srvan6.exe |
id=”82453″ align=”aligncenter” width=”600″] Srvan6.exe
Srvan6.exe
These kind of malware infections are particularly effective at performing advanced commands if set up so. They are based on a modular framework enabling the criminal controllers to manage all type of hazardous behavior. One of the popular examples is the adjustment of the Windows Registry – modifications strings related by the operating system can trigger severe efficiency interruptions and the inability to access Windows services. Relying on the scope of changes it can additionally make the computer totally unusable. On the various other hand manipulation of Registry values coming from any type of third-party installed applications can sabotage them. Some applications may fail to release entirely while others can unexpectedly stop working.
This specific miner in its current version is concentrated on extracting the Monero cryptocurrency consisting of a customized version of XMRig CPU mining engine. If the projects verify successful after that future variations of the Srvan6.exe can be introduced in the future. As the malware makes use of software vulnerabilities to infect target hosts, it can be component of a harmful co-infection with ransomware as well as Trojans.
Removal of Srvan6.exe is highly suggested, given that you risk not just a huge electrical energy costs if it is operating on your PC, but the miner might also execute other undesirable activities on it and even damage your COMPUTER permanently.
Srvan6.exe removal process
STEP 1. First of all, you need to download and install GridinSoft Anti-Malware.
STEP 2. Then you should choose “Quick scan” or “Full scan”.
STEP 3. Run to scan your computer
STEP 4. After the scan is completed, you need to click on “Apply” button to remove Srvan6.exe
STEP 5. Srvan6.exe Removed!
Video Guide: How to use GridinSoft Anti-Malware for remove Srvan6.exe
How to prevent your PC from being reinfected with “Srvan6.exe” in the future.
A Powerful Antivirus solution that can detect and block fileless malware is what you need! Traditional solutions detect malware based on virus definitions, and hence they often cannot detect “Srvan6.exe”. GridinSoft Anti-Malware provides protection against all types of malware including fileless malware such as “Srvan6.exe”. GridinSoft Anti-Malware provides cloud-based behavior analyzer to block all unknown files including zero-day malware. Such technology can detect and completely remove “Srvan6.exe”.