About Popn
Popn is classified by our virus analyst team as the DJVU virus infection. Another variants of this family here: About STOP/Djvu Ransomware. There are certain scanners that bypass it as well as therefore permitting its invasion. Actually, we have to call it that, because of the “.popn” extension that it attaches at the end of your files.
Let’s clarify. Popn malware assaults your laptop through stealth and sleight also. After that, once embedded it applies AES or RSA encryption methods to lock your files.
Popn encrypted your files, but that might not be the only damage done to you. The viruses might still be in your computer. To remove them, we suggest downloading GridinSoft Anti-Malware.
Download GridinSoft Anti-Malware
GridinSoft Anti-Malware Review, How to get free trial?, EULA, and Privacy Policy.
Then, they blackmail you for their unblocke. After Popn slips right into your computer, it places every one of your data under isolation. It adds its very personal extension “.popn” at the end, thus making records isolated.
Files with “.popn” extension appended by the Popn virus:
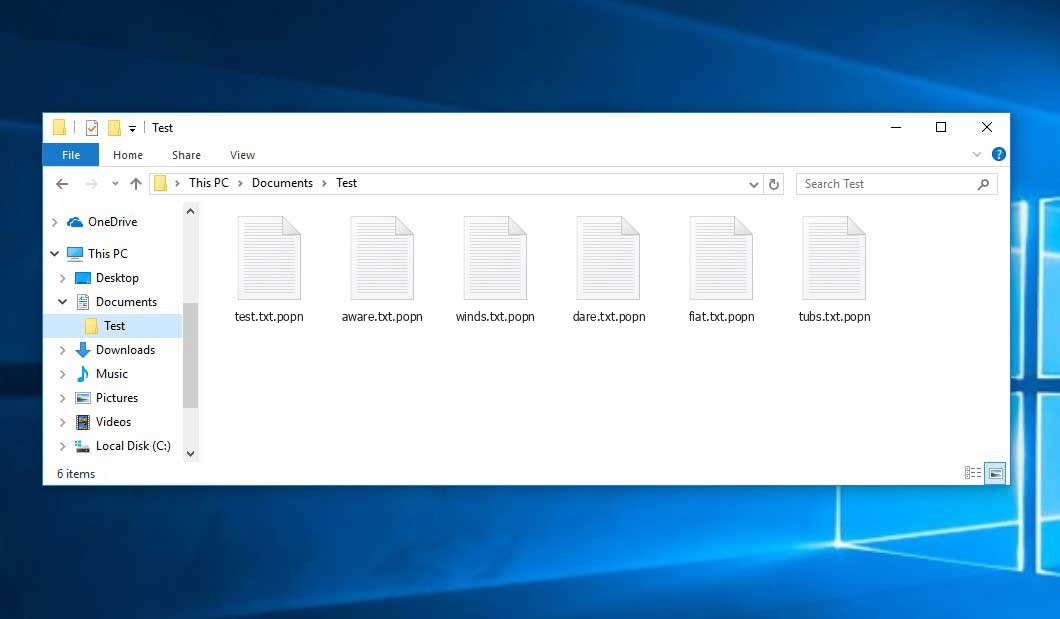
It reaches files, archives, photos, songs, filmings, all of it! Thereafter, you can’t longer open them. Relocating records or renaming it will not facilitate. The only means to unblocke your data from the virus’ keep is decryption. The virus is aimed you to disburse blackmail cash if you wish to get your documents back. It makes that clear (in the ransom note) it will decipher records after defrayal.
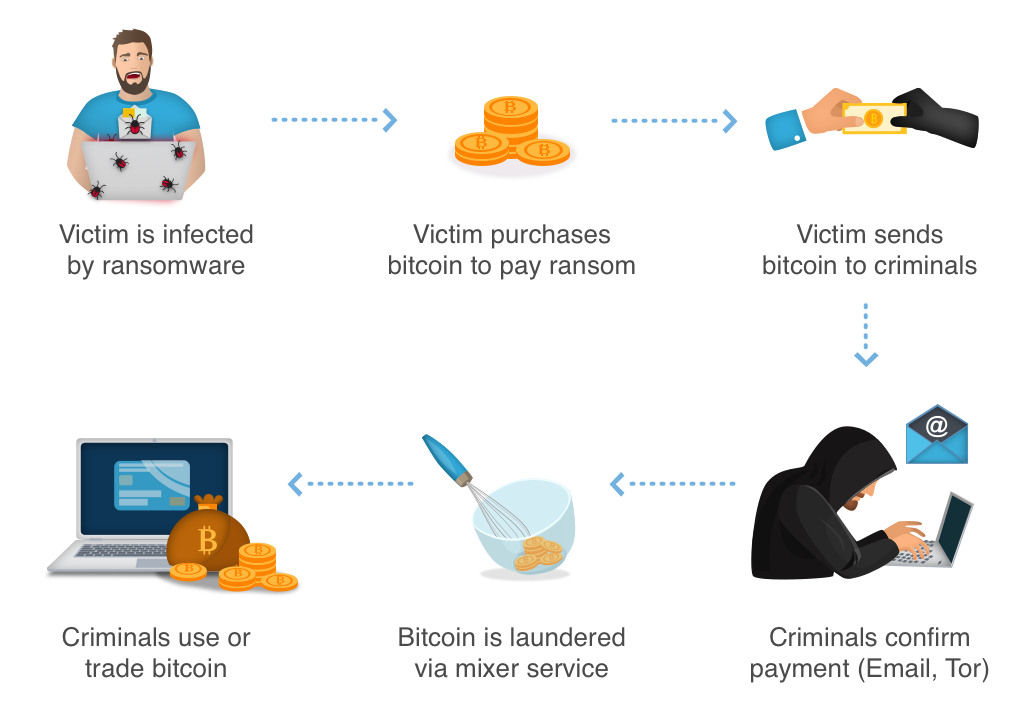
The note is generally a text file, left on your desktop. You can also find it in each folder that contains enciphered records. It describes your troubles and also proposes you an answer. According to Popn, the only means to decode your files is with an only decoding code. And also, to obtain it you have to send a buyout. The sum is $980, as well as it’s usually asked for in Bitcoins.
The note by the Popn ransomware states the following information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WbgTMF1Jmw Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: restorealldata@firemail.cc Reserve e-mail address to contact us: gorentos@bitmessage.ch Our Telegram account: @datarestore Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Do NOT pay for decrypt of “popn” files!
The Popn infection guarantees, to send you the code after you disburse. As well as, that’s it. That’s all you obtain – a promise. You have no assurances that subordination finishes in something appropriate. Do not rest on words of virtual crooks. That is people, that will cheat you. Do NOT disburse them a cent. Don’t call them Do NOT comply with their needs.
How did my PC got harmed by Popn?
Your devices get contaminated with the Popn virus because of your incapacity to be on the guard. Some people do not notice essential details while surfing the web or downloading various programs.
The Popn infection uses the old but good annexationist methods to deceive you. And rushes in unnoticed. That involves disguising behind broken web links, sites, and torrents. It applies free tools as a way to hide itself. And forms as a phony system or application update. Like, Adobe Flash Player or Java.
Yet more often than not, it makesuse of junk emails. You obtain an email that seems to find from a well-known company. Like, Amazon or PayPal. And, the email incites you to visit a web link, or download and install an tool. If you do, you end up with malware.
Remember that these types of risks are deluding your inadvertence. They need you to rush and lose doing due diligence. That enable their covert penetration. They rely on you to leave your fate to chance. Do not! Don’t pick recklessness over care. One keeps viruses out. The other welcomes them in.
Therefore, do not send them a fee. Don’t contact to the virtual frauds. If you do, you’ll regret it. It’s a vain attempt to recover your data, as well as it will not finish well for you. Below’s why.
There are a few cases that can interpret when you see the redemption cash note on your desctop. Claim, you make a decision to comply. You contact to the racketeers, send their redemption money, and wait. You wait on them to send you the deciphering trick they guaranteed. Well, what happens if they do not?
Even so, you have no guarantees. All, you rely on, is a faith. Can you absolutely think words of cyber kidnappers? The answer is ‘No.’ These are individuals, who will clearly disappoint you. Don’t give a cent! There’s also another alternative.
They can actually send you a decryption key. However, when you attempt to apply it, it fails to work.
Yes, they can send you the wrong key. After that, you have much less funds, as well as your files continues to be blocked. Don’t pay! And also your prime case isn’t a reason for enjoyment. What takes place after you pay the buyout money, obtain the appropriate trick, as well as totally free your documents? Well? Consider it. You paid ransom to eliminate a sign and symptom, yet not the malware triggering it.
So, you remove the encryption, yet the Popn malware stays. It’s still prowling in the corners of your system, complimentary to harm once again. After that, you’re back at a new start.
Why is Popn unsafe?
Moreover, to encipher a injured’s records, the Popn virus has also started to install the Azorult Spyware on PC to steal account credentials, cryptocurrency wallets, desktop records, and more.
So, your PC obtained assaulted by Popn and also probably you have actually lost time trying to fix it manually. We are absolutely positive that the remedy below will certainly be effective in removing Popn in an automated method.
How to protect PC from Popn ransomware?
However, let us initially speak about prevention of such malware attacks in the future. There is something exists that you can do to escape this kind of critical danger from entering into your device previously?
There are a couple of things we wish to talk about here. First one is your personal blame for being beyond belief careful while you utilize your computer and largely while you surf the internet. When examining your e-mail and see some distrustful accessories consisted of, do not hurry to open them.
The same way, when you get on Facebook and social networks also someone you know sends you messages attaching accessories, be very attentive, especially if these are some executable files.
Another thing to take into consideration is researching the reliability of your current anti-virus program. Sadly, there are plurals safety and security programs presently that just declare to be credible, whereas in times of real malware intrusions they simply unable to do the task as promoted.
In case Popn intruded into your laptop this indicates that your current anti-virus did not do its promoted assignment as well as really fell short to protect your system. So obviously it is a point for you to overrate your choices and also definitely change over to some other program that can most definitely provide the wanted degree of security.
Not all antiviruses are good
We can extra discuss some portion of users that like not to have any kind of anti-virus software program at all. Definitely, this is a big mistake on their component, due to the fact that presently the web has lots of cyber jeopardies that may covertly penetrate perceptive systems, particularly those that are not appointed with some standard level of safety.
So, having protection tool constantly working and guiding your computer is a necessary point in today’s cyber world.
Popn is getting on the nerves of many users, so you’re not its only victim.
People ask how to repair the problem effectively. Getting rid of the infection manually may be a long-lasting undertaking and can damage other important system files. Scan your PC with GridinSoft Anti-Malware to detect and delete Popn in the right way.

15 Reasons to Choose GridinSoft, How to get free trial?, EULA, and Privacy Policy.
Popn removal guide
STEP 1. Recover files from Popn ransomware encryption
You can download free decryption tool here: Decryptor for STOP Djvu. But it work when the Popn virus used an offline key for encryption.
If key does not found, we advice to restore your PC
There are a lot of different ransomware viruses on the internet. Some of them are more dangerous than the others because they not only leaving malicious processes to protect themselves, but also removing backups of your system to make the recovery process impossible.
Please Note: Not all ransomware infections are able to remove backups of your system, so it is always worth to try a windows recovery.
We recommend use Safe Mode with command prompt to safely perform a recovery of your files. You will have to reboot your computer, so you better save this instruction:
How to Restore Files from a Backup in Windows 7/8/10
STEP 2. Removing Popn ransomware malicious files
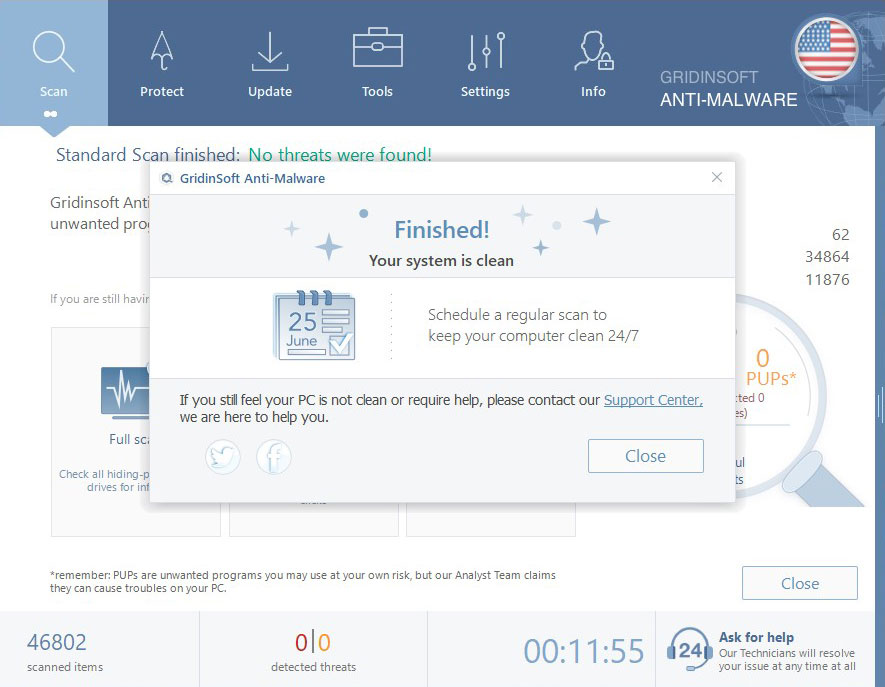
Once the recovery process is complete, you should consider scanning your computer with a GridinSoft Anti-Malware in order to find any traces of Popn infection. Though some ransomware viruses are removing themselves right after the encryption of your files, some may leave malicious processes on your computer for special purposes of cyber criminals.
-
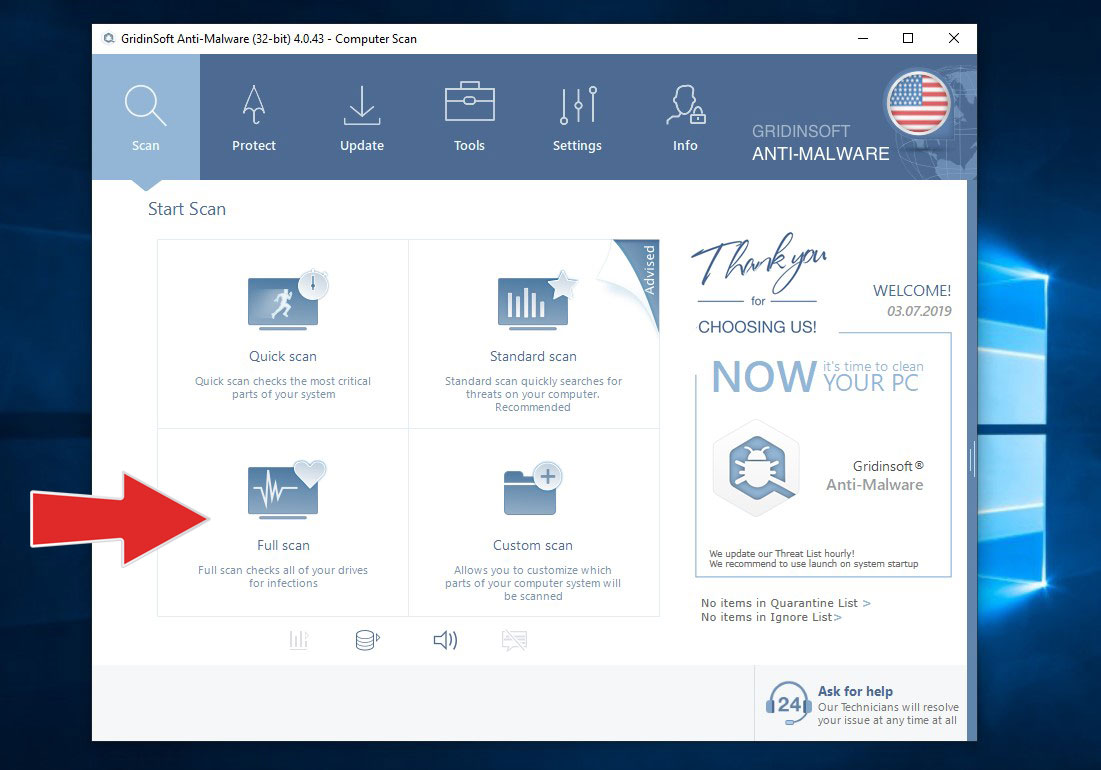
Run GridinSoft Anti-Malware and choose the scan type, which is suitable for your needs. Of course, for the accuratest scan results we recommend you to choose the “Full Scan”.
-
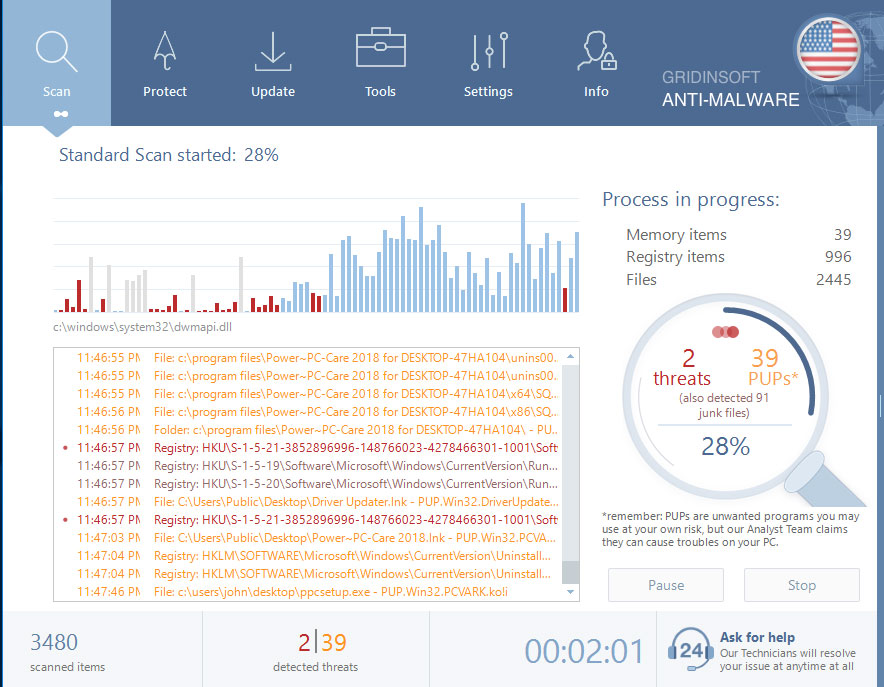
Give Anti-Malware a little time to check your system:
-
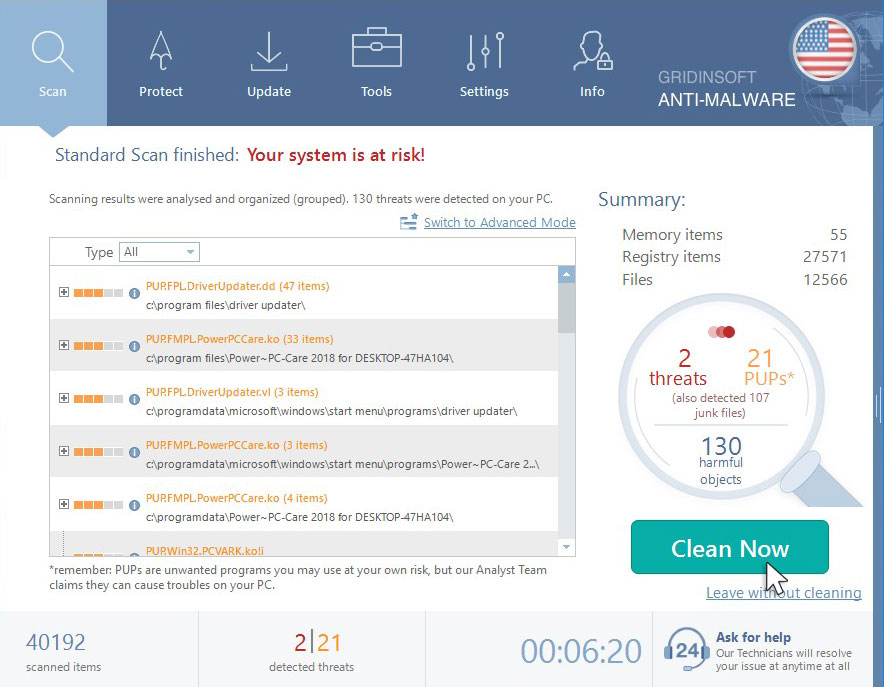
Move to quarantine all the viruses and unwanted files, that you see in the results list:
-
Enjoy the malware removal process:
-
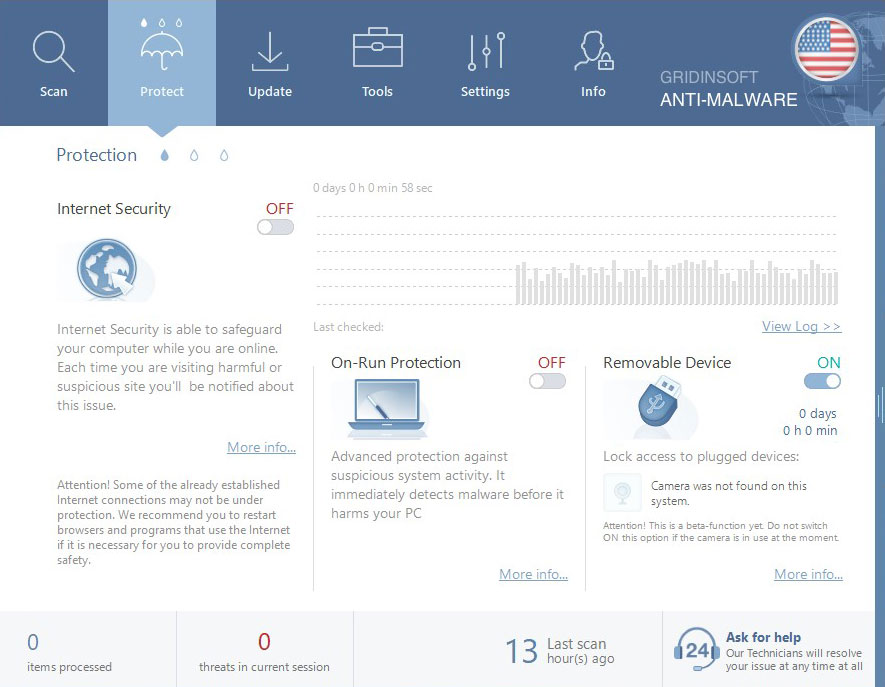
Use of On-run protection may additionaly prevent different types of cyber attacks, our protect may flag the downloader of the ransomware as a malicious application preventing the download of Popn.
STEP 3. Prevent the Popn virus infection
Besides the protection tool, you should read and learn few simple rules. Follow them every time you work on your computer and your will decrease chances of your infection to a minimum:
- Don’t open suspicious letters. No way! Be very careful with your downloads. Download and install software preferably from its trusted website.
- Do backups of your important files regularly. Storing your really important files in few different places is a good decision.
- Keep your computer free from adware, hijackers and PUPs The infected computer will be more likely compromised with other malicious software, and ransomware is not an exception in this case.
- Don’t panic and be reasonable. Don’t pay the ransom fee right after you got infected, it is always best to search on the internet for some answers. It is possible that someone have developed a decryption tool that might help you.