Un completamente nuevo, muy inseguro virus de la minera criptomoneda ha sido descubierto por los científicos de protección y seguridad. el software malicioso, llamado Wecapi.exe puede contaminar los enfermos de diana usando una selección de medios. La idea principal detrás de la minera Wecapi.exe es utilizar actividades criptomoneda minero en los sistemas informáticos de los objetivos con el fin de obtener símbolos Monero a expensas de los objetivos. El resultado final de este minero es el aumento de los gastos de energía eléctrica y si lo deja por períodos de tiempo más largos, Wecapi.exe también puede dañar las partes de sus sistemas informáticos..
Wecapi.exe: Métodos de distribución de
los Wecapi.exe marcas de malware uso de dos enfoques importantes que se hacen uso de la computadora a los objetivos contaminan:
- Entrega de carga útil a través de infecciones previas. Si se lanza un malware Wecapi.exe más antiguo en los sistemas afectados, puede actualizarse automáticamente o descargar e instalar una versión más reciente.. Esto es factible mediante el comando de actualización integrado que obtiene la versión. Esto se realiza mediante la conexión a un determinado predefinido servidor web pirata informático controlado que da el código de malware. El virus descargado obtendrá el nombre de una solución de Windows y también se colocará en el “%sistema% temp” ubicación. Los edificios importantes y también los documentos de configuración del sistema operativo se transforman para permitir una infección persistente y también silenciosa.
- El aprovechamiento de vulnerabilidades de software. Se ha descubierto que la versión más reciente del malware Wecapi.exe fue activada por algunas empresas, ampliamente reconocido por ser hecho uso de los asaltos en ransomware. Las infecciones se llevan a cabo por la orientación soluciones abiertas a través del puerto TCP. Los ataques son automatizados por una estructura pirata informático controlado que busca determinar si el puerto está abierto. Si se cumple esta condición, ciertamente escaneará el servicio y recuperará la información al respecto., que consta de cualquier versión y también información de disposición. Empresas y también nombre de usuario prominente, así como combinaciones de contraseñas se pueden hacer. Cuando el exploit es causado contra el código vulnerable, el minero ciertamente se implementará junto con la puerta trasera.. Esto ofrecerá la doble infección.
Además de estos métodos, también se pueden utilizar otras estrategias.. Los mineros se pueden distribuir mediante correos electrónicos de phishing que se envían al por mayor de forma similar al SPAM y también se basan en métodos de ingeniería social para confundir a las víctimas y hacerles creer que realmente han recibido un mensaje de una solución o empresa genuina.. Los archivos de infección pueden adjuntarse directamente o colocarse en el contenido del cuerpo en contenido web multimedia o enlaces web de texto..
Los malhechores también pueden producir páginas web destructivas de touchdown que pueden hacerse pasar por páginas de descarga e instalación del proveedor., sitios web de descarga de software y varios otros lugares a menudo se accede. Cuando hacen uso de nombres de dominio aparentemente similares para direcciones legítimas, así como certificaciones de protección, los clientes pueden verse obligados a comunicarse con ellos.. En algunos casos simplemente abrirlos pueden desencadenar la infección minero.
Un enfoque más sería utilizar proveedores de transporte que se puedan distribuir utilizando esos métodos o mediante redes de intercambio de documentos., BitTorrent es una de una de las más preferidas. Se utiliza con regularidad para distribuir archivos y aplicaciones de software originales, así como contenido web pirata.. 2 de uno de los proveedores de servicios de carga útil más populares son los siguientes:
Otros métodos que pueden ser considerados por los malhechores incluyen el uso de secuestradores de navegadores de Internet, complementos peligrosos que se adaptan a los navegadores web preferidos.. Se cargan en las bases de datos apropiadas con testimonios individuales falsos y también calificaciones de desarrollador.. En muchos casos, los resúmenes pueden consistir en imágenes, videoclips, así como intrincados resúmenes que prometen grandes mejoras de funciones y también optimizaciones de eficiencia. Sin embargo, tras la instalación, los hábitos de los navegadores influidos ciertamente cambiarán.- las personas seguramente se darán cuenta de que serán redirigidas a una página de destino controlada por piratas informáticos y también se podría modificar su configuración – la página de inicio por defecto, motor de búsqueda, así como la página pestañas nuevo.

Wecapi.exe: Análisis
El malware Wecapi.exe es una situación clásica de un minero de criptomonedas que, dependiendo de su configuración, puede crear una amplia gama de actividades dañinas.. Su objetivo principal es ejecutar trabajos matemáticos complejos que sin duda capitalizarán las fuentes del sistema fácilmente disponibles.: UPC, GPU, memoria, así como área del disco duro. El método con el que funcionan es mediante la vinculación a un servidor web especial llamado grupo de minería desde donde se descarga e instala el código necesario.. Tan rápidamente como uno de los trabajos que se descarga se comenzará simultáneamente, numerosos casos se pueden ejecutar en cuando. Cuando se termina una tarea determinada, se descargará otra en su lugar y el ciclo continuará hasta que la computadora se apague, la infección se elimina o se produce otro evento similar. Criptomoneda será otorgado a los controladores de criminales (piratería equipo o un solo pirata informático) directamente a sus bolsillos.
Una cualidad insegura de esta categoría de malware es que muestras como esta pueden tomar todas las fuentes del sistema y casi inutilizar el sistema informático de la víctima hasta que el peligro haya sido eliminado por completo.. Muchos de ellos cuentan con una instalación persistente que los hace realmente difíciles de eliminar.. Estos comandos desde luego hacer los ajustes para arrancar opciones, documentos de disposición y valores del Registro de Windows que sin duda harán que el malware Wecapi.exe se inicie automáticamente tan pronto como se encienda el sistema informático. El acceso a las selecciones de alimentos de recuperación, así como a las alternativas, puede estar bloqueado, lo que hace que muchas descripciones generales de eliminación manuales sean prácticamente ineficaces..
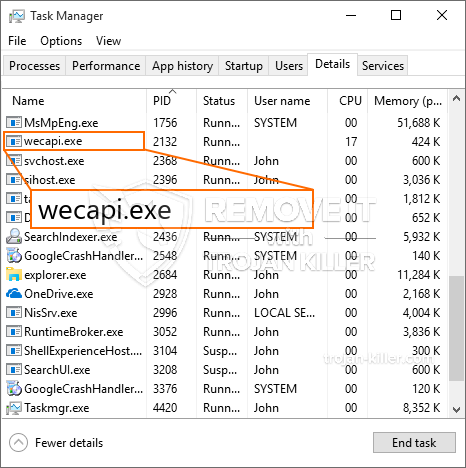
Este será sin duda cierta infección configurar un servicio de Windows por sí mismo, tras el análisis de seguridad realizado, se han observado las siguientes acciones:
. Durante las operaciones minero el malware relacionado se puede unir a la ejecución de los servicios actualmente en Windows y las aplicaciones de terceros también instalados. Al hacerlo, es posible que los administradores del sistema no vean que los lotes de origen se originan en un procedimiento diferente.
| Nombre | Wecapi.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware para detectar y eliminar Wecapi.exe |

Este tipo de infecciones de malware son especialmente eficaces para ejecutar comandos sofisticados si se configuran de esta manera.. Se basan en un marco modular que permite a los controladores penales coordinar todo tipo de comportamientos nocivos.. Uno de los ejemplos populares es la modificación del registro de Windows – Las cadenas de alteraciones asociadas por el sistema operativo pueden desencadenar importantes interrupciones en la eficiencia y también la imposibilidad de acceder a los servicios de Windows.. Dependiendo de la magnitud de los ajustes que asimismo puede hacer que el equipo completamente inútil. Por otro lado, el ajuste de los valores del Registro que pertenecen a cualquier aplicación montada por terceros puede socavarlos.. Es posible que algunas aplicaciones no se publiquen por completo, mientras que otras pueden dejar de funcionar inesperadamente.
Este minero en particular en su variación existente se concentra en extraer la criptomoneda Monero que consiste en una variación modificada del motor de minería de CPU XMRig. Si las campañas verifican que son efectivas, se pueden introducir versiones futuras de Wecapi.exe en el futuro.. A medida que el software malicioso hace uso del programa de software susceptabilities contaminar los hosts de destino, puede ser componente de una coinfección con ransomware perjudiciales, así como troyanos.
Se recomienda encarecidamente la eliminación de Wecapi.exe, dado que se arriesga no solo a incurrir en un gran gasto de energía eléctrica si está funcionando en su COMPUTADORA, sin embargo, el minero también podría realizar otras tareas no deseadas en él, así como también dañar su COMPUTADORA permanentemente.
Proceso de eliminación de Wecapi.exe
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” botón para eliminar Wecapi.exe
PASO 5. Wecapi.exe eliminado!
Guía de vídeo: Cómo utilizar GridinSoft Anti-Malware para eliminar Wecapi.exe
Cómo evitar que su PC de reinfección con “Wecapi.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “Wecapi.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “Wecapi.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “Wecapi.exe”.







