En ny, veldig farlig kryptovaluta miner virus har blitt oppdaget av beskyttelses forskere. den malware, kalt CPUInfo.exe can contaminate target victims making use of a selection of ways. Essensen bak CPUInfo.exe miner er å ansette kryptovaluta miner aktiviteter på datamaskinene til sufferers for å skaffe Monero symboler på lider utgifter. The outcome of this miner is the elevated power costs and also if you leave it for longer amount of times CPUInfo.exe might also damage your computers parts.
CPUInfo.exe: distribusjonsmetoder
De CPUInfo.exe malware bruker to fremtredende metoder som brukes for å forurense datamaskinsystemmål:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older CPUInfo.exe malware is deployed on the target systems it can immediately update itself or download and install a more recent variation. Dette er mulig å bruke den integrerte oppdateringskommandoen som får utgivelsen. Dette gjøres ved å knytte til en bestemt forhåndsdefinert hacker-kontrollert server som gir malware-koden. Den nedlastede og installere infeksjonen vil få navnet på en Windows-løsning, samt bli plassert i “%Systemet% temp” plassering. Viktige hjem og også kjørende systemordningsfiler blir transformert for å tillate en jevn og rolig infeksjon.
- Utnytter programvare for sikkerhetsproblem. The most current version of the CPUInfo.exe malware have been discovered to be brought on by the some ventures, mye forstått for å ha blitt benyttet i ransomware-streikene. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt struktur som vender opp om porten er åpen. Hvis denne betingelsen er oppfylt, vil den skanne tjenesten samt hente informasjon angående den, som består av hvilken som helst versjon og også konfigurasjonsinformasjon. Utnytter og populær brukernavn samt passord mikser kan gjøres. Når bruken er satt av mot den sårbare koden, blir gruvearbeideren frigjort i tillegg til bakdøren. Dette vil sikkert presentere en dobbelinfeksjon.
Bortsett fra disse teknikkene kan det også benyttes forskjellige andre tilnærminger. Gruvearbeidere kan spres ved hjelp av phishing-e-post som blir sendt ut i bulk på en SPAM-lignende måte og er også avhengige av sosialtekniske triks for å pusle ofrene til å tro at de faktisk har mottatt en melding fra en ekte tjeneste eller selskap. Infeksjonsdataene kan enten kobles rett inn eller settes inn i kroppens innhold i multimediainnhold eller nettleser for meldinger.
Kriminelle kan på samme måte lage skadelige destinasjonssider som kan utgjøre seg for leverandørens nedlasting og installering av websider, programvare last ned portaler og andre ofte tilgjengelige steder. Når de bruker lignende tilsynelatende domenenavn som legit adresser og også sikkerhetssertifiseringer, kan kundene bli tvunget til å samarbeide med dem. I mange tilfeller rett og slett å åpne dem kan aktivere miner infeksjon.
En annen strategi vil absolutt være å bruke transportører som kan spres ut ved å bruke disse metodene eller via nettverk for deling av dokumenter, BitTorrent er en av de mest populære. Det blir ofte brukt til å spre både legit programvare så vel som dokumenter og piratinnhold. To av de mest populære transportørene er følgende:
Ulike andre metoder som skurkene kan tenke på inkluderer bruk av nettleserkaprere - skrekkelige plugins som er gjort egnet med de mest foretrukne nettlesere.. De blir publisert til de aktuelle depotene med falske kundeavtaler og programmeringskvalifikasjoner. I mange tilfeller beskrivelsene kan bestå av skjermbilder, videoer samt sofistikerte sammendrag som lover utmerkede attribusforbedringer og ytelsesoptimaliseringer. Ikke desto mindre vil vanene til de påvirkede nettleserne ved innstilling endre seg- enkeltpersoner vil oppdage at de vil bli omdirigert til en hacker-kontrollert destinasjonsside og innstillingene deres kan bli endret – standard startside, internett søkemotor og også nye faner side.
CPUInfo.exe: Analyse
The CPUInfo.exe malware is a timeless instance of a cryptocurrency miner which depending on its setup can trigger a wide range of unsafe actions. Its primary goal is to perform intricate mathematical jobs that will certainly benefit from the available system sources: prosessor, GPU, minne og harddiskplass. Metoden de fungerer er ved å feste til en unik server som kalles gruvedrift, hvor den nødvendige koden lastes ned og installeres. As soon as one of the tasks is downloaded it will be started simultaneously, flere forhold kan være borte så snart. When a given task is finished an additional one will be downloaded and install in its place and the loop will continue up until the computer system is powered off, the infection is eliminated or one more similar occasion happens. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking team eller en enslig cyberpunk) direkte til sine budsjetter.
An unsafe quality of this category of malware is that samples like this one can take all system resources as well as virtually make the target computer pointless up until the risk has actually been entirely eliminated. Most of them include a persistent installment that makes them really difficult to remove. Disse kommandoene vil sikkert gjøre justeringer i oppstartsvalg, setup documents and Windows Registry values that will make the CPUInfo.exe malware start immediately as soon as the computer is powered on. Accessibility to healing food selections as well as alternatives might be blocked which renders numerous hand-operated elimination overviews virtually ineffective.
Denne spesifikke infeksjonen vil sikkert arrangere en Windows-løsning for seg selv, adhering to the carried out safety and security analysis ther adhering to actions have actually been observed:
. During the miner procedures the connected malware can connect to already running Windows solutions and third-party installed applications. By doing so the system administrators might not observe that the resource tons comes from a different procedure.
| Navn | CPUInfo.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove CPUInfo.exe |
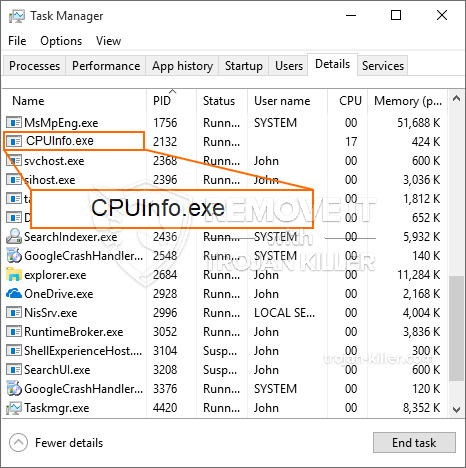
id =”83115″ juster =”aligncenter” width =”600″] CPUInfo.exe
CPUInfo.exe
These type of malware infections are especially reliable at executing innovative commands if set up so. They are based on a modular framework enabling the criminal controllers to orchestrate all type of harmful behavior. Blant de foretrukne tilfellene er endringen av Windows-registeret – alterations strings connected by the os can cause serious efficiency interruptions and the lack of ability to gain access to Windows solutions. Relying on the range of changes it can likewise make the computer system completely unusable. På den annen side kan manipulering av registerverdier som kommer fra alle typer tredjepartsoppsettprogrammer sabotere dem. Some applications might fall short to release completely while others can suddenly quit working.
This specific miner in its present variation is concentrated on extracting the Monero cryptocurrency including a modified version of XMRig CPU mining engine. If the campaigns verify effective then future versions of the CPUInfo.exe can be launched in the future. Som malware benytter program sårbarheter for å forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Removal of CPUInfo.exe is highly advised, because you run the risk of not just a big electrical power expense if it is working on your COMPUTER, but the miner may likewise do various other undesirable tasks on it and even harm your COMPUTER permanently.
CPUInfo.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove CPUInfo.exe
SKRITT 5. CPUInfo.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove CPUInfo.exe
Hvor å forhindre din PC blir infisert med “CPUInfo.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “CPUInfo.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “CPUInfo.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “CPUInfo.exe”.