Een gloednieuw, zeer onveilig cryptogeld mijnwerker virus daadwerkelijk is gespot door onderzoekers bescherming. de malware, riep 1Google.exe infecteren doel patiënten samen met een selectie van middelen. De essentie achter de 1Google.exe mijnwerker is om cryptogeld mijnwerker activiteiten op de computers van de doelen te gebruiken om Monero verkrijgen tokens op doelen ten koste. Het resultaat van deze mijnwerker wordt de verhoogde elektrische energie kosten en als je het laten voor langere perioden 1Google.exe kan zelfs schade toebrengen aan uw computer componenten.
1Google.exe: distributiemethoden
De 1Google.exe malware gebruikmaakt van twee populaire methoden die worden gebruikt om doelen computersysteem infecteren:
- Payload bezorging via Prior Infecties. Als een oudere 1Google.exe malware wordt uitgebracht op het slachtoffer systemen kunnen het zich meteen upgrade of download een recentere versie. Dit is mogelijk via de ingebouwde update-commando dat de lancering krijgt. Dit gebeurt door verbinding met een bepaalde voorgedefinieerde-hacker gecontroleerde webserver die malware code levert. De gedownloade en installeer virus zal zeker de naam van een Windows-service te verwerven en in het worden geplaatst “%systeem% temp” plaats. Belangrijke gebouwen evenals lopende configuratie gegevens worden omgezet in om een consistente en stille infectie toestaan.
- Software Application Vulnerability Exploits. De nieuwste versie van de 1Google.exe malware daadwerkelijk zijn ontdekt te worden veroorzaakt door het aantal ondernemingen, volksmond begrepen te worden gebruikt in de ransomware aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. Als aan deze voorwaarde wordt voldaan zal de oplossing ook controleren als om alles over, bestaande uit elke vorm van versie en configuratiegegevens. Ventures evenals prominente gebruikersnaam en ook met een wachtwoord mixen zou kunnen worden gedaan. Als de exploit wordt veroorzaakt tegen de gevoelige code de mijnwerker zullen samen worden ingezet met de achterdeur. Dit zal het een dubbele infectie bieden.
Naast deze technieken verschillende andere methoden eveneens kunnen worden toegepast. Mijnwerkers kunnen worden gedistribueerd door phishing e-mails die in bulk in een SPAM-achtige manier worden verzonden en ook rekenen op social design trucs om de slachtoffers verwarren recht te laten denken dat ze een bericht van een betrouwbare oplossing of bedrijf hebben gekregen. Het virus bestanden kan direct worden aangesloten of zet in het lichaam componenten in multimedia-inhoud of de tekst weblinks.
De criminelen kunnen ook schadelijke bestemmingspagina's die leverancier te downloaden webpagina's kunnen nabootsen, softwaretoepassing downloaden portals en ook andere veelgebruikte locaties. Wanneer zij gebruik maken van soortgelijke verschijnen domein legitieme adressen en certificaten bescherming maken van de individuen kunnen worden gedwongen recht in met hen te communiceren. Soms alleen het openen van hen kan verrekenen de mijnwerker infectie.
Een extra aanpak zou zeker zijn om payload service providers die verspreiding kan gebruikt worden uit het gebruik van deze technieken of door middel van het delen van gegevens netwerken, BitTorrent is slechts een van een van de meest geprefereerde. Het wordt vaak gebruikt om zowel legale software applicatie en ook documenten en ook piraten materiaal te verspreiden. Twee van de meest populaire haul providers zijn de volgende:
Diverse andere methoden die in aanmerking door de overtreders kunnen worden genomen zijn het gebruik van browser hijackers -Schadelijk plug-ins die geschikt zijn gemaakt met de meest prominente internet browsers. Ze worden geüpload naar de relevante databanken met nep individuele getuigenissen en ook programmeur geloofsbrieven. In de meeste gevallen zijn de samenvattingen kunnen zijn screenshots, video's en fancy samenvattingen aansprekende prachtig attribuut verbeteringen en ook de prestaties optimalisaties. Toch bij de installatie van de gewoonten van de beïnvloed browsers zal zeker veranderen- klanten zullen vinden dat ze zullen worden omgeleid naar een hacker gecontroleerde landing page en ook hun instellingen kunnen worden gewijzigd – de standaard startpagina, internet zoekmachine en ook nieuwe tabbladen pagina.

1Google.exe: Analyse
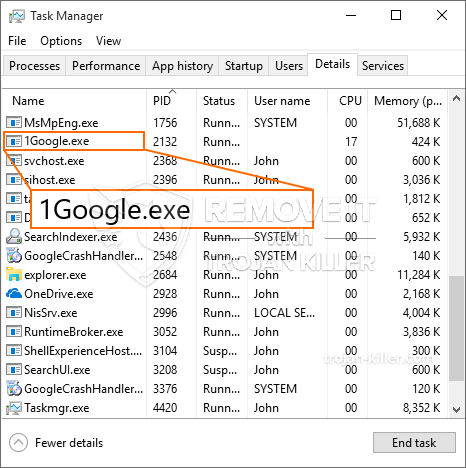
De 1Google.exe malware is een tijdloos voorbeeld van een cryptogeld mijnwerker die, afhankelijk van de configuratie van een breed scala aan gevaarlijke activiteiten kunnen creëren. Het primaire doel is om complexe wiskundige banen die zeker zal profiteren van de beschikbare systeembronnen te doen: processor, GPU, geheugen en ook de ruimte op de harde schijf. De methode die ze functioneren is door te verbinden met een speciale server genaamd mijnbouw zwembad waar de opgeroepen voor de code is gedownload en geïnstalleerd. Zodra één van de banen wordt gedownload zal tegelijkertijd worden begonnen, tal van omstandigheden kunnen zo snel worden uitgevoerd bij. Wanneer een voorwaarde taak is voltooid één meer men wordt gedownload in zijn gebied en ook zal de maas in de wet zeker blijven totdat de computer is uitgeschakeld, de infectie is geëlimineerd of extra vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal worden toegekend aan de criminele controllers (hacken team of een enkele cyberpunk) direct naar hun portemonnee.
Een onveilige kwaliteit van deze categorie malware is dat voorbeelden zoals deze alle systeembronnen kan nemen en bijna de lijder computersysteem onbruikbaar maken tot het risico volledig is verwijderd. De meesten van hen hebben een aanhoudende aflevering waardoor ze eigenlijk uitdagend om te verwijderen. Deze opdrachten zullen aanpassingen ook alternatieven, setup-bestanden en Windows-register waarden die de 1Google.exe zal maken malware onmiddellijk beginnen zodra de computer wordt ingeschakeld. De toegankelijkheid van het helen van voedsel selecties en opties kunnen worden belemmerd die tal van handmatige verwijdering overzichten vrijwel zinloos maakt.
Deze bijzondere infectie zal zeker arrangement een Windows-oplossing voor zichzelf, aanleiding van de uitgevoerde veiligheid en beveiliging evaluatie ther zich te houden aan de activiteiten daadwerkelijk waargenomen:
. Tijdens de mijnwerker operaties kunnen de aangesloten malware te koppelen aan reeds met Windows oplossingen en set van derden up applicaties. Door dit te doen zodat het systeem beheerders mogen niet zien dat de bron ton afkomstig is van een afzonderlijke procedure.
| Naam | 1Google.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware op te sporen en te verwijderen 1Google.exe |

Dit soort malware-infecties zijn specifiek betrouwbaar bij het vervullen van geavanceerde commando's als zo opgezet. Ze zijn gebaseerd op een modulair kader dat de criminele controllers om allerlei schadelijke acties orkestreren. Een van de favoriete gevallen is de wijziging van het Windows-register – aanpassingen strings gerelateerd door de os kan leiden tot ernstige efficiency verstoringen en het gebrek aan vermogen om toegang te krijgen tot Windows-services. Afhankelijk van de omvang van de veranderingen die het kan bovendien maken de computer volledig onbruikbaar. Anderzijds aanpassing van register waardes behorende tot elk type derden geïnstalleerde applicaties te saboteren. Sommige toepassingen te kort zou schieten om geheel vrij te geven, terwijl anderen plotseling werken kan stoppen.
Deze bijzondere mijnwerker in de bestaande versie is geconcentreerd op het extraheren van de Monero cryptogeld met een veranderde variatie van XMRig CPU mijnbouw motor. Als het project succesvol blijkt na dat toekomstige versies van de 1Google.exe in de toekomst kan worden ingevoerd. Als de malware maakt gebruik van software applicatie kwetsbaarheden te misbruiken doelhosts infecteren, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en ook Trojaanse paarden.
Verwijdering van 1Google.exe is aangeraden, omdat je het risico niet alleen een groot elektriciteitsrekening lopen als het werkt op uw pc, maar de mijnwerker kan voeren ook diverse andere ongewenste activiteiten op het zo goed als zelfs je pc volledig beschadigen.
1Google.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om 1Google.exe verwijderen
STAP 5. 1Google.exe verwijderd!
video Guide: Hoe wordt GridinSoft Anti-Malware gebruiken voor het verwijderen 1Google.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “1Google.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “1Google.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “1Google.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “1Google.exe”.







