Un completamente nuevo, extremadamente peligrosos virus de la minera criptomoneda ha sido detectado por los investigadores de seguridad. el software malicioso, llamado M2017.exe puede infectar a los enfermos de diana utilizando una variedad de medios. La idea principal detrás de la minera M2017.exe es utilizar las actividades minero criptomoneda en los ordenadores de los objetivos con el fin de obtener Monero fichas a un costo objetivos. The result of this miner is the elevated power costs and also if you leave it for longer time periods M2017.exe may also damage your computers parts.
M2017.exe: Métodos de distribución de
los M2017.exe malware utilizes two prominent techniques which are made use of to contaminate computer targets:
- Entrega de carga útil a través de infecciones previas. If an older M2017.exe malware is deployed on the sufferer systems it can immediately update itself or download and install a more recent version. Esto es posible mediante el comando de actualización integrado que recibe el lanzamiento. Esto se realiza mediante la conexión a un servidor web predefinido pirata informático controlado específica que da el código de malware. La infección descargada e instalada obtendrá el nombre de un servicio de Windows y se posicionará en el “%sistema% temp” ubicación. Crucial homes and also running system setup files are changed in order to allow a persistent and silent infection.
- El aprovechamiento de vulnerabilidades de software. The newest variation of the M2017.exe malware have been found to be caused by the some exploits, ampliamente entendido por ser hecho uso de los asaltos en ransomware. Las infecciones son realizadas por dirigir los servicios abiertos utilizando el puerto TCP. Los asaltos son automatizados por una estructura Hacker-controlada que busca si el puerto está abierto. If this problem is met it will check the service and also retrieve information concerning it, compuesto por cualquier versión y también datos de configuración. Ventures, así como nombre de usuario preferido, así como mezclas de contraseña se pueden hacer. When the make use of is triggered against the susceptible code the miner will certainly be released along with the backdoor. Esto servirá de una infección dual.
In addition to these approaches various other methods can be used also. Miners can be dispersed by phishing emails that are sent in bulk in a SPAM-like way as well as depend upon social design methods in order to puzzle the sufferers right into thinking that they have obtained a message from a genuine service or company. The infection files can be either straight attached or inserted in the body components in multimedia material or text links.
The crooks can likewise produce malicious landing web pages that can impersonate supplier download and install web pages, software download websites as well as various other frequently accessed places. When they utilize similar appearing domain to legit addresses and also safety certifications the customers might be persuaded into communicating with them. En muchos casos simplemente abrirlos puede causar la infección minero.
One more method would certainly be to utilize payload providers that can be spread making use of the above-mentioned techniques or through data sharing networks, BitTorrent es uno de los más destacados. It is often made use of to distribute both genuine software application and documents and pirate content. 2 de uno de los más destacados proveedores de servicios de carga útil son los siguientes:
Various other approaches that can be taken into consideration by the offenders consist of making use of web browser hijackers -harmful plugins which are made compatible with the most preferred internet browsers. They are posted to the pertinent repositories with phony customer reviews and also designer credentials. En muchos casos, las descripciones pueden consistir en imágenes, videos as well as elaborate descriptions promising wonderful attribute enhancements and also efficiency optimizations. Nonetheless upon setup the actions of the affected internet browsers will certainly alter- customers will certainly discover that they will be redirected to a hacker-controlled landing page and also their setups could be modified – la página web por defecto, motor de búsqueda y también nuevas pestañas página Web.

M2017.exe: Análisis
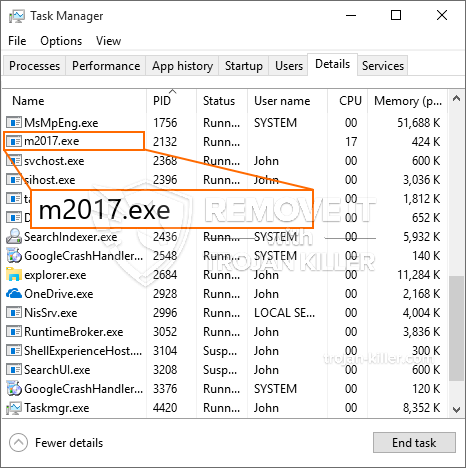
The M2017.exe malware is a classic situation of a cryptocurrency miner which relying on its configuration can cause a wide variety of dangerous activities. Its main objective is to perform complex mathematical jobs that will make use of the available system resources: UPC, GPU, memoria y también el área del disco duro. The means they work is by attaching to an unique server called mining swimming pool where the needed code is downloaded. Tan pronto como se descargue entre las tareas, se iniciará al mismo tiempo, varias circunstancias se pueden realizar en cuanto. When an offered task is completed an additional one will certainly be downloaded in its location and the loophole will proceed till the computer system is powered off, la infección se elimina o se produce una ocasión similar adicional. Criptomoneda será otorgado a los controladores de criminales (piratería equipo o un solo pirata informático) directamente a sus bolsillos.
A hazardous characteristic of this classification of malware is that samples such as this one can take all system sources and almost make the target computer system unusable until the danger has actually been totally gotten rid of. The majority of them include a relentless installment which makes them actually tough to get rid of. Estos comandos realizar cambios en las opciones de arranque, configuration files as well as Windows Registry values that will make the M2017.exe malware begin automatically once the computer system is powered on. Accessibility to healing food selections as well as choices may be obstructed which provides several manual elimination guides almost ineffective.
Esta configuración de la infección voluntad particular una solución de Windows por sí mismo, adhering to the carried out security analysis ther adhering to actions have actually been observed:
. During the miner procedures the linked malware can connect to already running Windows services and also third-party installed applications. By doing so the system administrators may not see that the resource lots originates from a different process.
| Nombre | M2017.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware to detect and remove M2017.exe |

Este tipo de infecciones de malware son específicamente eficientes para ejecutar comandos avanzados si se configuran así.. Se basan en un marco modular que permite a los controladores criminales orquestar todo tipo de acciones peligrosas.. Entre los ejemplos preferidos es el ajuste del registro de Windows – Las cadenas de alteraciones relacionadas con el sistema operativo pueden desencadenar importantes alteraciones en el rendimiento y también la falta de capacidad para acceder a los servicios de Windows.. Confiar en el rango de cambios también puede hacer que la computadora sea completamente inútil. Por otro lado, la manipulación de los valores del Registro provenientes de cualquier tipo de aplicaciones instaladas por terceros puede socavarlos.. Algunas aplicaciones pueden quedarse corto para poner en marcha por completo, mientras que otros pueden cerrarse inesperadamente trabajando.
Este determinado minero en su versión actual se enfoca en extraer la criptomoneda Monero incluyendo una versión modificada del motor de minería CPU XMRig. If the campaigns show successful after that future variations of the M2017.exe can be introduced in the future. A medida que el malware utiliza vulnerabilidades de software para infectar a los hosts de destino, puede ser componente de un co-infección dañina con ransomware y troyanos.
Elimination of M2017.exe is highly recommended, ya que corre el riesgo no solo de una factura de electricidad enorme si se está ejecutando en su COMPUTADORA, sin embargo, el minero también puede ejecutar otras actividades no deseadas en él y también dañar su COMPUTADORA de forma permanente.
M2017.exe removal process
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” button to remove M2017.exe
PASO 5. M2017.exe Removed!
Guía de vídeo: How to use GridinSoft Anti-Malware for remove M2017.exe
Cómo evitar que su PC de reinfección con “M2017.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “M2017.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “M2017.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “M2017.exe”.







