Un completamente nuevo, Realmente virus de la minera criptomoneda dañina ha sido encontrado por los científicos de protección y seguridad. el software malicioso, llamado Atnon.exe puede contaminar víctimas diana usando una gama de métodos. La idea principal detrás de la minera Atnon.exe es emplear actividades criptomoneda minero en los sistemas informáticos de las víctimas con el fin de obtener símbolos Monero a un costo enfermos. El resultado de este minero es los gastos de energía planteadas, así como si la deja durante períodos más largos de tiempo Atnon.exe también podría dañar los elementos de los sistemas informáticos.
Atnon.exe: Métodos de distribución de
los Atnon.exe utiliza de malware 2 métodos preferidos que se utilizan para infectar los objetivos del sistema de ordenador:
- Entrega de carga útil a través de infecciones previas. Si un software malicioso Atnon.exe mayores se libera en los sistemas víctima inmediatamente actualizará a sí mismo o descargar e instalar una versión más reciente. Esto es factible a través del comando integrado de actualización que adquiere el lanzamiento. Esto se realiza mediante la conexión a un servidor pirata informático controlado particular predefinida que suministra el código de malware. La infección descargado e instalar sin duda obtener el nombre de un servicio de Windows y se coloca en el “%sistema% temp” zona. casas esenciales, así como la ejecución de archivos disposición del sistema se transforman con el fin de permitir que una infección persistente y también tranquila.
- El aprovechamiento de vulnerabilidades de software. La última versión del software malicioso Atnon.exe han descubierto que ser provocado por la algunos exploits, comúnmente reconocida por ser hecho uso de los asaltos en ransomware. Las infecciones son realizadas por dirigir los servicios abiertos mediante el puerto TCP. Los ataques se realizan automáticamente por un marco de hackers controlada que mira hacia arriba si el puerto está abierto. Si se cumple esta condición sin duda va a escanear el servicio y también obtener información acerca de ella, incluyendo cualquier tipo de variación de datos y configuración. Exploits y nombre de usuario también prominente y también mezclas de contraseñas se pueden hacer. Cuando la manipulación es causada contra el código propenso al minero se desplegará junto con la puerta trasera. Esto servirá de una infección dual.
Además de estos enfoques otros métodos pueden hacer uso de, así. Los mineros pueden distribuirse por correos electrónicos de phishing que se envían a granel en forma de SPAM similares, así como dependen de los métodos de diseño sociales con el fin de confundir a los objetivos en la creencia de que han recibido un mensaje de un servicio de buena reputación o de la empresa. Los datos de la infección puede ser colocada directamente o poner en el contenido del cuerpo de material multimedia o mensajes de enlaces web.
Los delincuentes también pueden desarrollar páginas de destino destructivos que pueden suponer descargar e instalar páginas proveedor, aplicación de software sitios web de descarga y también varias otras áreas de acceso frecuente. Cuando hacen uso del dominio que suena similar a direcciones genuinas, así como certificaciones de seguridad de los clientes pueden ser persuadidos para que se conecte con ellos. A veces simplemente abrirlos puede activar la infección minero.
Una de las estrategias más sin duda sería hacer uso de portadores de carga útil que se pueden propagar a cabo haciendo uso de los métodos antes mencionados o por medio de redes de intercambio de archivos, BitTorrent es uno de los más populares. Se utiliza habitualmente para distribuir tanto el software original, así como datos y también el material pirata. 2 de uno de los portadores de acarreo más preferidos son los siguientes:
Otros métodos que pueden ser consideradas por los delincuentes consisten en hacer uso del navegador secuestradores plugins -harmful que se hacen adecuado con uno de los navegadores de Internet más destacados. Se publican las bases de datos apropiadas con testimonios de usuarios falsos y también las credenciales de programador. A menudo los resúmenes pueden consistir de capturas de pantalla, clips de vídeo y también descripciones de lujo que prometen excelentes mejoras de funciones, así como optimizaciones de rendimiento. Sin embargo a la configuración de los hábitos de los navegadores afectados alterarán- los clientes no van a encontrar que serán desviados a una página de destino pirata informático controlado, así como sus ajustes podrían ser alterados – la página web por defecto, motor de búsqueda y también la página web de pestañas nuevo.

Atnon.exe: Análisis
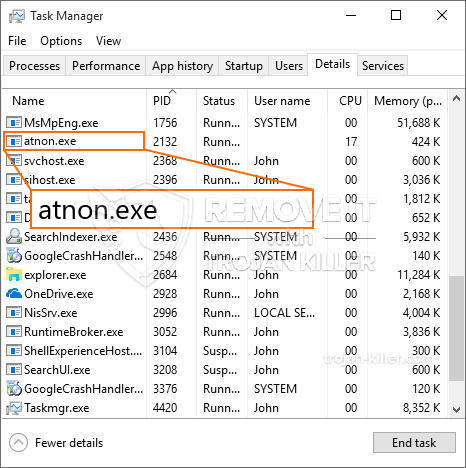
El software malicioso Atnon.exe es un ejemplo clásico de un minero criptomoneda que, dependiendo de su disposición se puede crear una variedad de actividades peligrosas. Su principal objetivo es llevar a cabo las tareas matemáticas complicadas que sin duda aprovechar las fuentes del sistema fácilmente disponibles: UPC, GPU, la memoria, así como espacio en disco duro. La forma de operar es mediante la vinculación a un servidor denominado piscina única en minería web desde donde el código necesario se descarga e instala. Tan rápidamente como uno de los trabajos que se descarga se iniciará simultáneamente, numerosos casos se pueden realizar en cuanto. Cuando se completa una tarea prevista una adicional se puede descargar e instalar en su lugar y también el bucle continuará hasta que el sistema de ordenador está apagado, la infección se elimina o un evento más parecido ocurre. Criptomoneda se compensará a los controladores criminales (un grupo de hackers o cyberpunk solitario) directamente a sus bolsillos.
Una característica de este grupo perjudiciales de malware es que las muestras como ésta pueden tomar todas las fuentes del sistema y también prácticamente hacer que el equipo de destino inutilizable hasta que el peligro ha sido eliminado por completo. Muchos de ellos cuentan con una instalación implacable que les hace realmente un reto para eliminar. Estos comandos harán ajustes para arrancar alternativas, archivos de disposición y los valores del Registro de Windows que harán que el software malicioso Atnon.exe inicia al instante cuando el ordenador está encendido. Accesibilidad a la curación de menús y opciones también pueden ser obstruido que hace un montón de eliminación manual guía a casi inútil.
Esta infección específica será sin duda disposición una solución de Windows por sí mismo, tras el análisis llevado a cabo la protección del ther siguientes actividades se han observado:
. Durante las operaciones minero el malware relacionado se puede conectar a la ejecución actualmente soluciones y aplicaciones de Windows también de terceros instaladas. Al hacerlo los administradores del sistema pueden no ver que la carga de recursos proviene de un proceso diferente.
| Nombre | Atnon.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware para detectar y eliminar Atnon.exe |

Este tipo de infecciones de malware son especialmente eficientes en el cumplimiento de órdenes sofisticados si se ha configurado de modo. Se basan en un marco modular que permite a los controladores criminales para orquestar todo tipo de comportamiento peligroso. Uno de los ejemplos populares es la alteración del registro de Windows – Ajustes por cadenas conectadas por el sistema operativo pueden crear perturbaciones graves de eficiencia, así como la imposibilidad de acceder a soluciones de Windows. Dependiendo de la magnitud de los ajustes que, además, puede hacer que el sistema informático totalmente inútil. Por otro lado el control de valores de las partes del Registro procedentes de cualquier tipo de terceros montada aplicaciones pueden sabotear ellas. Algunas aplicaciones podrían quedarse corto para liberar por completo, mientras que otros pueden cerrarse inesperadamente trabajando.
Esta cierta minero en su versión existente se concentra en la minería de la criptomoneda Monero que contiene una versión modificada del motor de minería CPU XMRig. Si las campañas resultan eficaces versiones futuras continuación de la Atnon.exe pueden ser liberados en el futuro. A medida que el malware utiliza vulnerabilidades de las aplicaciones de software para infectar a los hosts de destino, que puede ser componente de un co-infección peligrosa con ransomware y también troyanos.
Eliminación de Atnon.exe es muy recomendable, ya que se corre el riesgo de no sólo una enorme factura de energía eléctrica si se está ejecutando en el PC, pero el minero puede llevar adicionalmente a cabo otras tareas indeseables en él, así como incluso dañar su PC de forma permanente.
proceso de eliminación Atnon.exe
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” botón para eliminar Atnon.exe
PASO 5. Eliminado Atnon.exe!
Guía de vídeo: Cómo utilizar GridinSoft anti-malware para quitar Atnon.exe
Cómo evitar que su PC de reinfección con “Atnon.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “Atnon.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “Atnon.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “Atnon.exe”.







