
Gran cantidad de plugins para instrumento abierto de la integración ininterrumpida de software Jenkins contienen diferentes errores y vulnerabilidades.
Vvulnerabilidades relacionadas principalmente con el almacenamiento de contraseñas en forma no cifrada. Adicionalmente, en suaves CSRF-bugs encontrados Jenkins’ que permiten steaking credenciales y cometen ataques CSRF-.Viktor Rich, especialista de Grupo CNC que probó una gran cantidad de complementos de Jenkins, puesto de manifiesto estos problemas.
“Estas pruebas dieron como resultado más de 100 complementos encontrados vulnerables y varias divulgaciones públicas coordinadas y responsables”, — informa investigador.
Como explicó el experto, aunque Jenkins cifra las contraseñas en el archivo credentials.xml, algunos desarrolladores utilizan otros métodos de almacenamiento de datos. En la mayoría de los casos, estas decisiones no sugieren que estén encriptadas.. Además, algunos formularios web, donde los usuarios ingresan las credenciales, permitir la fuga de contraseñas o tokens secretos.
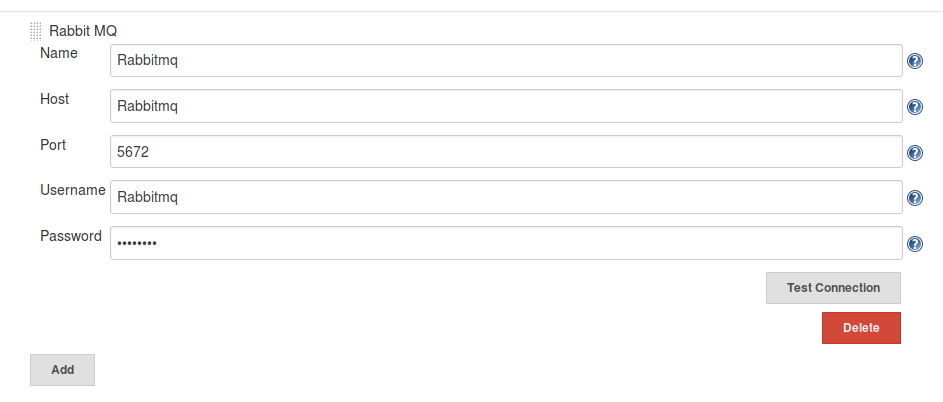
Las vulnerabilidades CSRF están conectadas con las funciones de los complementos, con el uso del cual los usuarios pueden verificar las credenciales y conectarse a un servidor. En su mayoría existen, ya que los desarrolladores no aplican solicitudes POST que evitan ataques con el uso del token CSRF.
En los últimos dos años, Los desarrolladores de Jenkins lanzaron varias notificaciones que describen vulnerabilidades en diferentes complementos, incluyendo una serie de errores, descubierto por Gazdag.
Los complementos vulnerables interactúan con un amplio círculo de servicios, incluso Gorjeo, AWS, vmware y Azur. En la mayoría de los casos, el software fue creado por desarrolladores secundarios que no están conectados con el proveedor., cuyo software explota el complemento.
Como se ha señalado, los autores de varios complementos ya han corregido errores en su software, aunque muchos siguen siendo vulnerables. En su turno, Los desarrolladores de Jenkins publicaron una amplia lista de complementos que aún no están reparados.
Fuente: https://www.nccgroup.trust
