
Sixgill, ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht, ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht. ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht, Telegramm, ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht, ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht, ein israelisches B2B-Cyber-Intelligence-Unternehmen, das das Deep Web und das Dark Web auf Bedrohungsinformationen analysiert und überwacht (ICH BIN) service became the real “ choice of the year” for various kinds of cybercriminal enterprises. In a four part series they will cover the most popular trends in criminal communities on Telegram.
Cybercriminals moved their business to Telegram
Not long ago the main marketplace for cybercriminals was “dark web” sites with an .onion extension. But today the tendency moves towards something like Telegram. Because you have to put some effort into maintenance and work of a traditional “dark web” forum while Telegram offers you a quicker and easier way to establish connection to potential customers. Cyber-Kriminelle only have to create a channel and the marketplace is ready to tend to the needs of customers. Though such channels don`t live too long, they quickly get banned for violating the terms of service.
Security researchers decided to dive into the depths of the new cybercriminal favorite hub and see what trends go there. They explored the topics of compromised financial accounts, illicit items for sale and malware; topics that are the most popular among the cybercriminal community.

First part of the research focuses on financial cybercrimes and what tendencies are going on here. On this topic specialists reveal an interesting fact that despite the significant growth of e-commerce in the times of COVID-19 pandemic the crimes connected with compromised credit cards, bank logs (compromised accounts) and money transfers (laundering) dropped remarkably low in 2021, declining near 60% from its 2020 rate. But in spite of this, in the period between August 2020 till December 2021 the total number of suspicious mentions on these topics has stood steadily around 3,500.
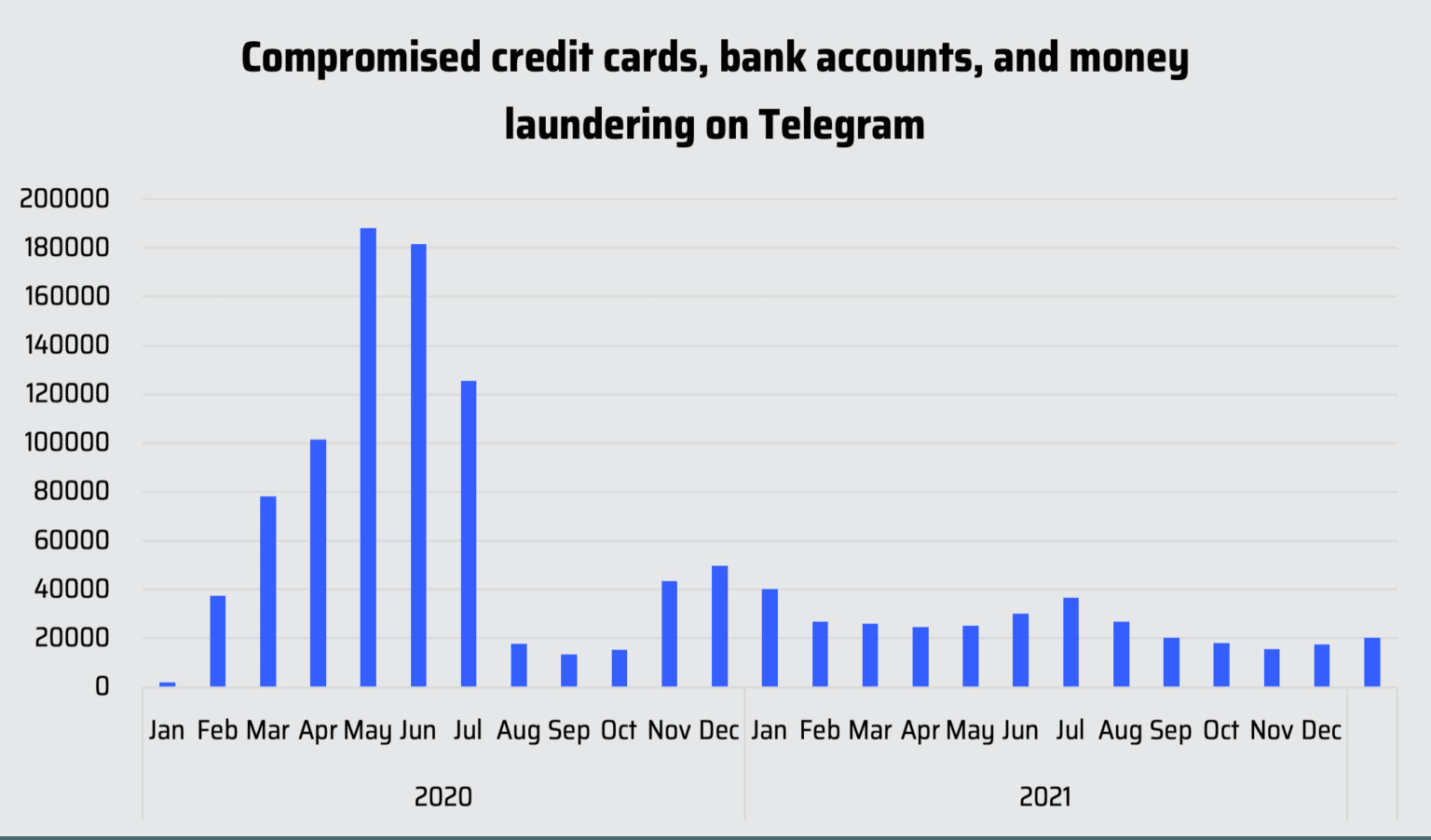
The specialists add that though the statistics might be surprising they detected the same tendencies with the selling of compromised credit cards sold on underground markets throughout the same period. In the Underground Financial Fraud report for H1 2021 the team connected the fact to the closure of several credit card markets ( either way done by some law enforcement or by cybercriminals themselves). Trends shifted towards contactless payments, general decrease of newly-issued cards summed up to it as well. It might also be the reason that ransomware (one the most evolved kind of cybercrime today) has proved itself quite a lucrative field in the past years and with everything steadily moving to the internet it promises more.
“You gotta keep working to keep money flowing”
So what’s in an agenda today among financial cybercriminals? The illicit activities in this field usually involve money transferring services, bank logs and compromised credit cards. They are the most popular and just by typing in for example “ bank logs” in the Telegram search bar you can find channels with up to thousands subscribers on it. Scrolling down some of them I thought but where’s these sort of the “guaranties” on the deal? Cyber security specialists definitely should try to run an experiment on the question.
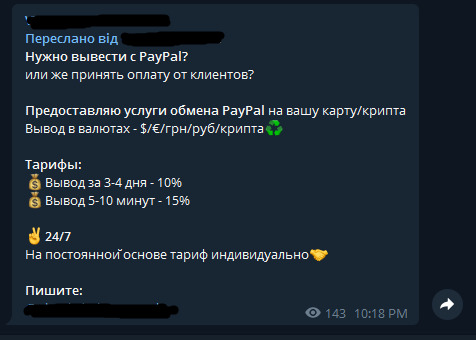
You know what money transferring services are. Users use them to move funds from one account and deposit them into another. The same with cybercriminals, using these services allows them to obfuscate the origin of stolen funds, launder them and successfully move them across the world. In Telegram criminal channels you can find the right service for the right price. meistens criminals use the most popular one money transferring services like PayPal, Cash App, und andere.
“Experienced” cybercriminals know very well that law enforcements may not yet knock on their door but they watching them. The thing is simple: if one cryptocurrency wallet was suspected in an illegal money flow activity then it can be “direct shot in the head” to use it again. The service is more popular with ransomware criminals especially if it`s some big groups of hackers with their affiliates. Money transfering service allows in such a case to quietly dissipate the stolen funds.

The screenshot below says in Russian: “ Need a cashout with PayPal? Or you need to receive the payment from clients? I offer the PayPal exchange service to your account/cryptocurrency wallet. Currency cashout: $/€/ hryvnias/rubles/cryptocurrency. Price: cashout in 3-4 days — 10%. Cashout in 5-10 minutes — 15%. 24/7. Prices for long term partnership are individual. Write to.”
The next kind of activity concerns bank logs. On a dark web logs refer to compromised bank credentials. Usually this kind of info includes more than just the username and password needed to login in to compromised accounts. But often it has highly sensitive information such as the personal answers to security verification questions. The price depends on the balances of the compromised bank account in an offer. Generally cybercriminals sell or buy them to conduct cashouts which means to fully empty the account of the funds.
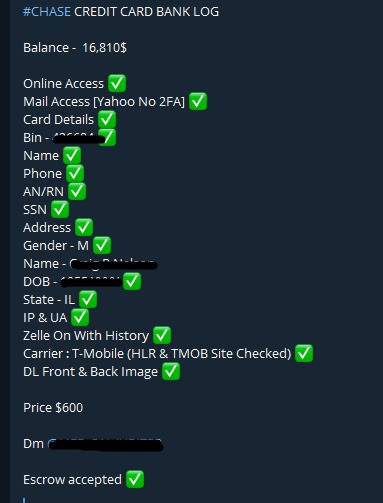
You may have noticed on both posts the interesting word “escrow”. No it`s not some kind of a code word for something criminal but instead this word means a normal legal term. And according to the investopedia.com “Escrow is a legal concept describing a financial instrument whereby an asset or escrow money is held by a third party on behalf of two other parties that are in the process of completing a transaction”. To explain it in the context of our topic it means when one criminal, Zum Beispiel, buy something in another criminal but they are not sure the one that they will receive the money and other will receive their goods or service. The common ground in this case would be escrow. The seller gets money when the buyer gets service or goods or vice versa. That`s what this word here stands for
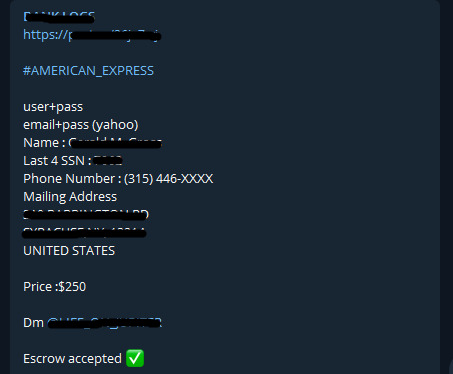
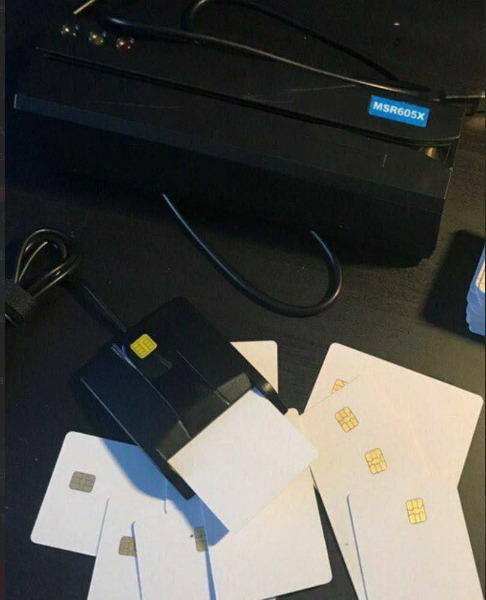
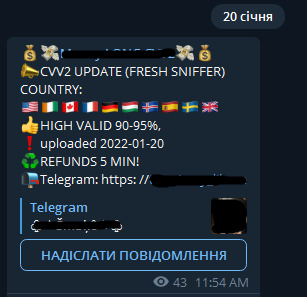
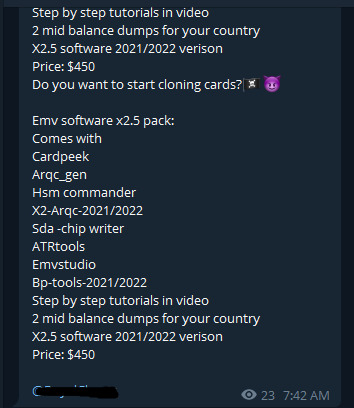
Compromised credit cards are another lucrative activity for cybercriminals. The compromised cards usually belong to the most widely used financial institutions like Mastercard, Visa, Western Union, Wells Fargo, the Bank of America and Chase Bank. The same as on the dark web markets you can buy cards`dumps or those including CVV/CVV2 information. Dumps mean the cards that contain segments of unencrypted data located on the magnetic strip of a card. The data includes account number, the cardholder’s name and other validating points that banks use to confirm the transaction. Criminals have to create the so-called physical clones of cards to use dumps.
With CVV/CVV2 ( used for remote transactions), Auf der anderen Seite, everything is much more simple because it allows criminals to empty funds online without risking that much. According to researchers CVV/CVV2 cards are more convenient offering the much needed anonymity for criminals and therefore they are in higher demand with ratio ~60% CVV/CVV2 to ~40% dumps.
For law enforcement, the rising popularity of this messaging app among cybercriminals makes everything harder. When they just shut another channel another one will appear after a while. You can say it’s like that whack a mole game that the current cybercrime industry begins to look like. And it concerns not only financial kinds of crimes but the selling of illicit goods, Malware, usw. And that lone drug dealer on the street quickly became a thing of the past.
