Ein neuer, Das wirklich gefährliche Cryptocurrency Miner-Virus wurde von Sicherheitswissenschaftlern identifiziert. die Malware, namens Wmpps.exe können eine Reihe von Möglichkeiten, Ziel Opfer infizieren mit. Der Hauptpunkt hinter dem Wmpps.exe-Miner ist die Verwendung von Cryptocurrency-Miner-Aktivitäten auf den Computersystemen von Betroffenen, um Monero-Token auf Kosten der Betroffenen zu erhalten. The end result of this miner is the raised power expenses and also if you leave it for longer periods of time Wmpps.exe may also harm your computers elements.
Wmpps.exe: Verteilungsmethoden
Das Wmpps.exe Malware verwendet zwei beliebte Methoden, die verwendet werden, um Computerziele zu kontaminieren:
- Payload Lieferung mit Vor-Infektionen. If an older Wmpps.exe malware is released on the victim systems it can immediately upgrade itself or download a newer version. Dies ist möglich, den integrierten Upgrade-Befehl, der den Start erhält. Dies erfolgt durch Verknüpfung mit einem bestimmten vordefinierten, von Hackern kontrollierten Server, der den Malware-Code bereitstellt. Die heruntergeladene Infektion wird sicherlich den Namen eines Windows-Dienst erwerben und in die gestellt werden “%System% temp” Standort. Wichtige Wohn- oder Gewerbeimmobilien und auch laufende Systemkonfigurationsdokumente werden geändert, um eine konsistente und leise Infektion zu ermöglichen.
- Software Application Vulnerability Exploits. The newest variation of the Wmpps.exe malware have actually been located to be triggered by the some ventures, allgemein bekannt für die Verwendung bei Ransomware-Angriffen. Die Infektionen werden durch Targeting offene Lösungen über den TCP-Port erfolgen. Die Angriffe werden von einem Hacker-kontrollierten Rahmen automatisiert die für sucht, ob der Port offen ist. Wenn dieses Problem behoben ist, wird es sicherlich die Lösung überprüfen und Informationen darüber abrufen, einschließlich einer beliebigen Version und auch Konfigurationsdaten. Exploits sowie bevorzugte Kombinationen aus Benutzername und Passwort können durchgeführt werden. Wenn die Manipulation gegen den gefährdeten Code verursacht wird, wird der Bergmann zusammen mit der Hintertür freigelassen. Diese präsentiert sicherlich die eine Doppelinfektion.
Abgesehen von diesen Ansätzen können auch andere Strategien verwendet werden. Miner können durch Phishing-E-Mails verbreitet werden, die massenhaft in SPAM-ähnlicher Weise versendet werden und sich auch auf Social-Engineering-Methoden verlassen, um die Ziele so zu verwirren, dass sie glauben, eine Nachricht von einer echten Lösung oder Firma erhalten zu haben. Die Virendaten können entweder direkt angehängt oder in den Körperinhalt von Multimedia-Webinhalten oder Text-Weblinks eingefügt werden.
Die Bösewichte können ebenfalls zerstörerische Touchdown-Seiten erstellen, die sich als Download- und Installationsseiten von Anbietern ausgeben können, Portale zum Herunterladen von Softwareanwendungen und andere Bereiche, auf die häufig zugegriffen wird. Wenn sie ähnlich aussehende Domains wie echte Adressen und Sicherheitszertifizierungen verwenden, können die Personen dazu überredet werden, mit ihnen zu kommunizieren. In einigen Fällen öffnen sie einfach die Bergmann-Infektion aktivieren.
Eine weitere Strategie wäre die Nutzung von Transportdienstanbietern, die über diese Methoden oder über Netzwerke zur gemeinsamen Nutzung von Dokumenten verteilt werden können, BitTorrent ist eine der am meisten bevorzugt diejenigen,. Es wird regelmäßig verwendet, um sowohl legitime Softwareanwendungen als auch Dokumente und Raubkopien zu verbreiten. Zwei der am meisten bevorzugten Streckenträger sind die folgenden:
Andere Methoden, die von den Angreifern in Betracht gezogen werden können, umfassen die Verwendung von Browser-Hijackern – gefährliche Plugins, die mit den bekanntesten Internetbrowsern kompatibel gemacht werden. Sie werden mit gefälschten Benutzerbewertungen und Entwicklerqualifikationen in die entsprechenden Repositories hochgeladen. In den meisten Fällen können die Zusammenfassungen von Screenshots aus, Videos und auch komplizierte Beschreibungen, die wunderbare Funktionserweiterungen und Leistungsoptimierungen ansprechen. Dennoch wird sich das Verhalten der betroffenen Browser bei der Installation sicherlich ändern- Benutzer werden sicherlich feststellen, dass sie sicherlich auf eine von Hackern kontrollierte Landing-Webseite umgeleitet werden und ihre Einstellungen möglicherweise geändert werden – die Standard-Startseite, Suchmaschine sowie brandneue Registerkarten Seite.

Wmpps.exe: Analyse
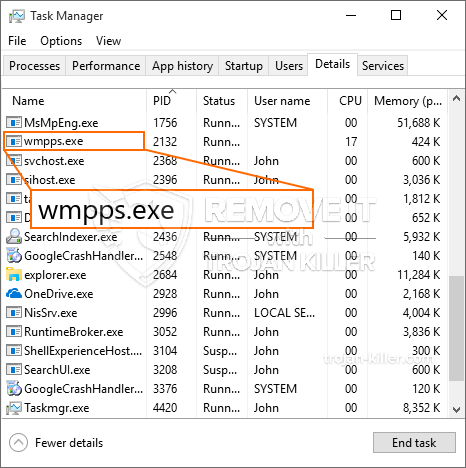
The Wmpps.exe malware is a classic situation of a cryptocurrency miner which depending on its configuration can create a wide array of dangerous actions. Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen: Zentralprozessor, GPU, Speicher und Festplattenspeicher. Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen. Sobald eine der Aufgaben heruntergeladen wird, wird es sofort gestartet werden, zahlreiche Umstände können so schnell durchgeführt werden, wie. Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen, oder ein vergleichbarer Anlass ist die Infektion erfolgt losgeworden. Kryptowährung wird sicherlich zu den kriminellen Controller vergeben (Hacker-Team oder eine einzelne cyber) gerade auf ihren Geldbeutel.
Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen. Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen. Diese Befehle werden Anpassungen zu Entscheidungen treffen, arrangement documents as well as Windows Registry values that will certainly make the Wmpps.exe malware start immediately once the computer system is powered on. Anordnungsdokumente sowie Windows-Registrierungswerte, die die Malware FTP.exe mit Sicherheit sofort starten lassen, sobald das Computersystem eingeschaltet wird.
Diese bestimmte Infektion Konfiguration Windows-Dienst für sich selbst, Nach der durchgeführten Sicherheitsanalyse wurden die folgenden Aktivitäten tatsächlich beobachtet:
. Durch ein Upgrade-Check-Modul kann die FTP.exe-Malware ständig prüfen, ob eine neue Variante der Gefahr veröffentlicht wird, und sie sofort verwenden. so dass die Systemmanager sehen nicht, dass die Quelle Last kommt aus einem anderen Verfahren Dadurch.
| Name | Wmpps.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware to detect and remove Wmpps.exe |

Diese Art von Malware-Infektionen sind besonders zuverlässig bei fortgeschrittenen Befehle erreichen, wenn so einrichten. Sie basieren auf einem modularen Rahmen, der es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichem Verhalten zu orchestrieren. Zu den beliebten Beispielen ist die Änderung der Windows-Registrierung – Durch das Betriebssystem verbundene Anpassungszeichenfolgen können zu schwerwiegenden Effizienzunterbrechungen und zum fehlgeschlagenen Zugriff auf Windows-Dienste führen. Je nach Umfang der Anpassungen kann der Computer dadurch auch völlig sinnlos werden. Auf der anderen Seite kann die Kontrolle von Registrierungswerten, die von installierten Anwendungen von Drittanbietern stammen, diese untergraben. Einige Anwendungen können möglicherweise nicht vollständig gestartet werden, während andere plötzlich nicht mehr funktionieren.
Dieser bestimmte Miner in seiner vorliegenden Variante konzentriert sich auf das Mining der Monero-Kryptowährung, die aus einer angepassten Version der XMRig-CPU-Mining-Engine besteht. If the projects confirm successful then future variations of the Wmpps.exe can be introduced in the future. Da die Malware nutzt Software-Schwachstellen Ziel-Hosts verunreinigen, es kann Teil eines gefährlichen Koinfektion mit Ransomware und Trojanern auch.
Elimination of Wmpps.exe is strongly advised, weil Sie nicht nur das Risiko großer Stromkosten eingehen, wenn es auf Ihrem COMPUTER läuft, Der Bergmann kann jedoch auch verschiedene andere unerwünschte Aktivitäten ausführen und Ihren COMPUTER dauerhaft schädigen.
Wmpps.exe removal process
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” button to remove Wmpps.exe
SCHRITT 5. Wmpps.exe Removed!
Video Guide: How to use GridinSoft Anti-Malware for remove Wmpps.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Wmpps.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Wmpps.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Wmpps.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Wmpps.exe”.







