Ein neuer, sehr unsichere Kryptowährung Bergmann-Virus wird von Sicherheitsexperten entdeckt worden. die Malware, namens Vsmic.exe kann eine Vielzahl von Methoden Ziel Erkrankten infizieren Verwendung. Das Wesentliche hinter dem Vsmic.exe-Miner ist die Verwendung von Cryptocurrency-Miner-Aufgaben auf den Computersystemen von Betroffenen, um Monero-Symbole zu Zielkosten zu erhalten. The end result of this miner is the elevated electrical energy bills and if you leave it for longer amount of times Vsmic.exe might even damage your computer systems components.
Vsmic.exe: Verteilungsmethoden
Das Vsmic.exe Malware nutzt 2 beliebte Ansätze, die verwendet werden, um Computersystemziele zu kontaminieren:
- Payload Lieferung durch Vor-Infektionen. If an older Vsmic.exe malware is released on the victim systems it can automatically upgrade itself or download a newer version. Dies ist mit dem integrierten Upgrade-Befehl möglich, der den Start erhält. Dies wird durch die Verknüpfung zu einem bestimmten vordefinierten Hacker gesteuerten Web-Server durchgeführt, die den Malware-Code gibt. Die heruntergeladene und installierte Infektion erhält den Namen einer Windows-Lösung und wird in die Datei eingefügt “%System% temp” Platz. Wesentliche Eigenschaften und Betriebssystem-Setup-Dateien werden geändert, um eine konsistente und auch leise Infektion zu ermöglichen.
- Software-Programm Ausnutzen von Sicherheitslücken. The newest version of the Vsmic.exe malware have been found to be brought on by the some exploits, Bekannt dafür, dass es in den Ransomware-Streiks verwendet wird. Die Infektionen werden durch Targeting offene Dienste über den TCP-Port erfolgen. Die Angriffe werden von einem Hacker-kontrollierten Rahmen automatisiert die für sucht, ob der Port offen ist. Wenn diese Bedingung erfüllt ist, wird der Dienst mit Sicherheit gescannt und es werden Informationen dazu eingeholt, bestehend aus jeder Art von Version sowie Setup-Informationen. Exploits und auch prominente Benutzernamen- und Passwortkombinationen können durchgeführt werden. Wenn der Exploit im Vergleich zum Risikocode verursacht wird, wird der Miner sicherlich zusammen mit der Hintertür bereitgestellt. Dies wird die eine doppelte Infektion bieten.
Neben diesen Methoden können auch andere Methoden verwendet werden. Bergleute können durch Phishing-E-Mails verteilt werden, die SPAM-artig in großen Mengen gesendet werden, und können von Tricks des sozialen Designs abhängen, um die Ziele zu verwirren und zu glauben, dass sie tatsächlich eine Nachricht von einer seriösen Lösung oder Firma erhalten haben. Die Infektionsdaten können entweder direkt angebracht oder in Multimedia-Inhalten oder Nachrichten-Weblinks in den Körperkomponenten platziert werden.
Die Gesetzesbrecher können auch schädliche Landing-Webseiten entwickeln, auf denen Seiten von Anbietern heruntergeladen und installiert werden können, Software-Programm-Download-Websites sowie verschiedene andere Orte, auf die häufig zugegriffen wird. Wenn sie ähnlich klingende Domainnamen wie seriöse Adressen und auch Schutzzertifizierungen verwenden, können die Personen gezwungen werden, mit ihnen zu interagieren. In vielen Fällen öffnen sie nur können die Bergmann-Infektion aktivieren.
Eine andere Technik wäre die Verwendung von Nutzlastdienstanbietern, die unter Verwendung dieser Ansätze oder über Datenaustauschnetzwerke verteilt werden können, BitTorrent ist unter einer der prominentesten. Es wird regelmäßig verwendet, um sowohl echte Software als auch Dateien sowie Pirateninhalte zu verbreiten. 2 von einem der beliebtesten Nutzlastanbieter sind die folgenden:
Andere Methoden, die von den Gaunern in Betracht gezogen werden können, bestehen darin, Browser-Hijacker zu verwenden - unsichere Plugins, die mit einem der bekanntesten Webbrowser kompatibel gemacht werden. Sie werden mit gefälschten Einzelbewertungen und Entwicklerqualifikationen in die entsprechenden Datenbanken hochgeladen. In den meisten Fällen können die Zusammenfassungen von Screenshots bestehen, Videos und ausgefeilte Beschreibungen bieten großartige Funktionsverbesserungen sowie Effizienzoptimierungen. Trotzdem ändern sich beim Einrichten die Aktionen der betroffenen Browser- Einzelpersonen werden feststellen, dass sie auf eine von Hackern gesteuerte Touchdown-Seite umgeleitet werden und ihre Einstellungen geändert werden können – die Standard-Webseite, Suchmaschine und neue Registerkarten Seite.

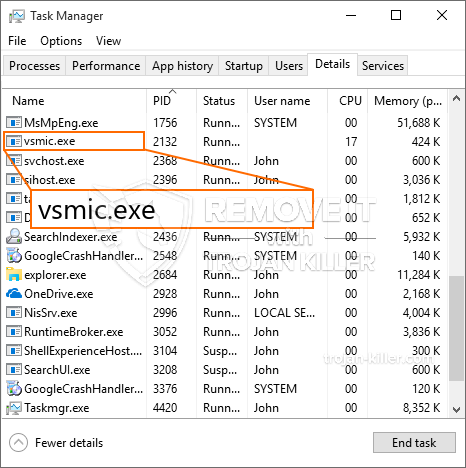
Vsmic.exe: Analyse
The Vsmic.exe malware is a classic instance of a cryptocurrency miner which depending on its setup can trigger a wide array of unsafe actions. Its major objective is to carry out complicated mathematical tasks that will certainly make the most of the offered system resources: Zentralprozessor, GPU, Speicher und Festplatte auch Raum. The way they function is by linking to an unique web server called mining swimming pool where the needed code is downloaded and install. Sobald bei den Arbeitsplätzen heruntergeladen wird es sicherlich zugleich begonnen werden, mehrere Umstände können ausgeführt werden, um, wenn. When a given job is finished an additional one will be downloaded and install in its location as well as the loophole will proceed till the computer system is powered off, die Infektion beseitigt oder eine andere vergleichbare Gelegenheit findet. Kryptowährung werden zu den kriminellen Controller kompensiert werden (Hacker-Gruppe oder ein einsames cyber) direkt an ihre Geldbörsen.
A harmful feature of this group of malware is that samples like this one can take all system resources and practically make the target computer unusable until the risk has actually been completely gotten rid of. The majority of them feature a consistent installation which makes them actually tough to remove. Diese Befehle werden Änderungen auch Alternativen machen, configuration files as well as Windows Registry values that will certainly make the Vsmic.exe malware beginning automatically as soon as the computer is powered on. Access to recuperation menus and alternatives might be blocked which makes numerous hands-on removal overviews virtually ineffective.
Diese bestimmte Infektion wird sicherlich Konfiguration Windows-Dienst für sich selbst, following the performed protection evaluation ther adhering to actions have actually been observed:
. During the miner procedures the associated malware can link to already running Windows services and also third-party set up applications. By doing so the system administrators may not see that the source lots originates from a different process.
| Name | Vsmic.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware to detect and remove Vsmic.exe |

These kind of malware infections are especially efficient at accomplishing sophisticated commands if set up so. They are based on a modular framework enabling the criminal controllers to coordinate all sort of hazardous habits. Unter den prominenten Fällen ist die Einstellung der Windows-Registrierung – alterations strings connected by the os can cause major performance disruptions and the inability to access Windows services. Depending upon the range of changes it can likewise make the computer totally unusable. On the various other hand manipulation of Registry worths coming from any kind of third-party set up applications can sabotage them. Some applications may fail to release completely while others can all of a sudden quit working.
This certain miner in its present version is focused on extracting the Monero cryptocurrency consisting of a modified variation of XMRig CPU mining engine. If the projects show successful then future versions of the Vsmic.exe can be introduced in the future. Da die Malware machen Schwachstellen Einsatz von Software Ziel-Hosts zu infizieren, es kann mit Ransomware-Komponente eines schädlichen Koinfektion und Trojanern auch.
Elimination of Vsmic.exe is strongly suggested, given that you run the risk of not just a large electrical energy bill if it’s operating on your PC, however the miner might likewise carry out other undesirable activities on it and also even damage your PC permanently.
Vsmic.exe removal process
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” button to remove Vsmic.exe
SCHRITT 5. Vsmic.exe Removed!
Video Guide: How to use GridinSoft Anti-Malware for remove Vsmic.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Vsmic.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Vsmic.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Vsmic.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Vsmic.exe”.







