Brandneu, Eine sehr schädliche Cryptocurrency Miner-Infektion wurde tatsächlich von Schutzforschern entdeckt. die Malware, namens CONH0ST.EXE können Ziel Erkrankten kontaminieren eine Auswahl von Mitteln unter Verwendung von. Die Hauptidee des CONH0ST.EXE-Miners besteht darin, Cryptocurrency-Miner-Aufgaben auf den Computern der Opfer einzusetzen, um Monero-Token auf Kosten der Betroffenen zu erhalten. The outcome of this miner is the raised electrical energy bills and also if you leave it for longer periods of time CONH0ST.EXE might even damage your computer systems components.
CONH0ST.EXE: Verteilungsmethoden
Das CONH0ST.EXE malware utilizes two prominent methods which are made use of to contaminate computer system targets:
- Payload Lieferung mittels Vor-Infektionen. If an older CONH0ST.EXE malware is deployed on the target systems it can immediately update itself or download a more recent variation. Dies ist möglich, den integrierten Upgrade-Befehl, der die Freigabe erhält. Dies wird durch das Anbringen an einen bestimmten vordefinierten Hacker gesteuerten Web-Server durchgeführt, die den Malware-Code bietet. Die heruntergeladene Infektion wird sicherlich den Namen einer Windows-Lösung erhalten und auch in der positioniert werden “%System% temp” Standort. Crucial buildings and operating system setup data are changed in order to allow a relentless and also quiet infection.
- Software Application Vulnerability Exploits. The most current version of the CONH0ST.EXE malware have been discovered to be brought on by the some exploits, weithin bekannt für die Verwendung in den Ransomware-Angriffen. Die Infektionen werden durch Targeting offene Dienste über den TCP-Port erfolgen. Die Streiks werden von einem Hacker gesteuerte Struktur automatisiert die für sucht, ob der Port offen ist. If this problem is satisfied it will scan the solution and also fetch details about it, einschließlich aller Versions- und Anordnungsdaten. Ventures sowie populäre Benutzername und Passwort Mixes getan werden könnte. When the make use of is activated against the prone code the miner will be deployed along with the backdoor. Diese präsentiert sicherlich die eine Doppelinfektion.
In addition to these techniques various other approaches can be made use of too. Miners can be dispersed by phishing e-mails that are sent in bulk in a SPAM-like fashion as well as depend on social design techniques in order to perplex the victims right into thinking that they have gotten a message from a legitimate solution or firm. The infection documents can be either directly attached or put in the body components in multimedia web content or message web links.
The wrongdoers can likewise develop destructive landing pages that can pose vendor download pages, Software-Download-Sites und verschiedene andere Bereiche, auf die regelmäßig zugegriffen wird. When they utilize similar sounding domain to legit addresses and protection certificates the individuals might be coerced right into connecting with them. Manchmal öffnen sie einfach die Bergmann-Infektion aktivieren.
An additional method would be to make use of haul carriers that can be spread using the above-mentioned methods or via data sharing networks, BitTorrent ist eine der prominentesten. It is regularly used to disperse both legit software program and also data and pirate content. Two of the most popular payload service providers are the following:
Other approaches that can be thought about by the crooks include using web browser hijackers -harmful plugins which are made suitable with the most preferred internet browsers. They are published to the relevant databases with phony user evaluations and programmer credentials. In vielen Fällen können die Beschreibungen von Screenshots bestehen, video clips and fancy summaries encouraging terrific attribute improvements and also efficiency optimizations. However upon installation the habits of the influenced web browsers will alter- customers will locate that they will certainly be rerouted to a hacker-controlled touchdown page and also their setups may be modified – die Standard-Startseite, Online-Suchmaschine sowie brandneue Registerkarten Webseite.

CONH0ST.EXE: Analyse
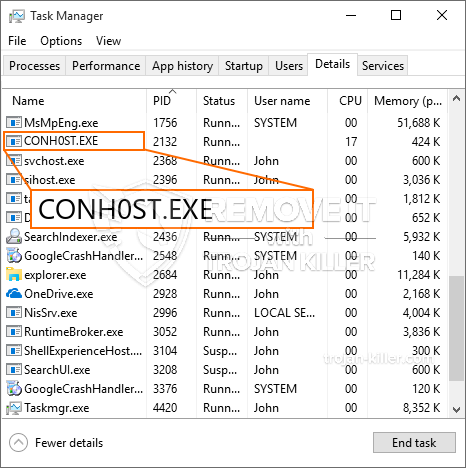
The CONH0ST.EXE malware is a traditional case of a cryptocurrency miner which relying on its configuration can cause a wide array of unsafe actions. Its main objective is to carry out complicated mathematical jobs that will certainly benefit from the readily available system sources: Zentralprozessor, GPU, Speicher und Festplatte auch Raum. Sie funktionieren, indem sie sich mit einem speziellen Webserver namens Mining Pool verbinden, von dem der erforderliche Code heruntergeladen und installiert wird. So schnell, wie bei den Aufgaben heruntergeladen wird es zur gleichen Zeit wird begonnen, mehrere Instanzen können gleichzeitig ausgeführt werden. When an offered task is completed another one will certainly be downloaded in its location and also the loop will proceed till the computer is powered off, die Infektion beseitigt wird oder ein weiterer vergleichbarer Anlass eintritt. Kryptowährung werden zu den kriminellen Controller belohnt (Hacker-Team oder ein einsames cyber) gerade zu ihrem Geldbeutel.
A hazardous quality of this group of malware is that samples such as this one can take all system sources and also almost make the sufferer computer system pointless till the risk has been entirely eliminated. Most of them include a relentless installment which makes them truly tough to get rid of. Diese Befehle werden sicherlich Modifikationen zu Entscheidungen treffen, setup data and Windows Registry values that will make the CONH0ST.EXE malware beginning automatically when the computer system is powered on. Access to recovery menus as well as options might be blocked which makes numerous manual removal overviews almost useless.
Diese spezifische Infektion Anordnung ein Windows-Dienst für sich, auf die durchgeführten Sicherheitsbewertung anhaftende Ther auf Maßnahmen der Einhaltung beobachtet:
. During the miner procedures the associated malware can link to currently running Windows services and also third-party set up applications. By doing so the system administrators may not observe that the resource tons comes from a separate procedure.
| Name | CONH0ST.EXE |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware to detect and remove CONH0ST.EXE |

These kind of malware infections are specifically efficient at carrying out advanced commands if configured so. They are based on a modular framework permitting the criminal controllers to manage all type of dangerous behavior. Zu den bevorzugten Beispielen ist die Änderung der Windows-Registrierung – adjustments strings related by the operating system can trigger major performance interruptions and also the failure to access Windows services. Je nach Umfang der Anpassung kann es ebenfalls der Computer macht völlig sinnlos. On the other hand adjustment of Registry worths coming from any type of third-party set up applications can undermine them. Some applications might fall short to introduce entirely while others can all of a sudden stop working.
This certain miner in its current variation is focused on mining the Monero cryptocurrency having a changed version of XMRig CPU mining engine. If the campaigns prove effective after that future versions of the CONH0ST.EXE can be introduced in the future. Da die Malware verwendet Software susceptabilities Ziel-Hosts zu infizieren, es kann Bestandteil einer gefährlichen Koinfektion mit Ransomware und Trojaner sein.
Removal of CONH0ST.EXE is strongly advised, given that you take the chance of not only a huge electrical power expense if it is working on your PC, however the miner may likewise execute other unwanted activities on it as well as also harm your COMPUTER completely.
CONH0ST.EXE removal process
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” button to remove CONH0ST.EXE
SCHRITT 5. CONH0ST.EXE Removed!
Video Guide: How to use GridinSoft Anti-Malware for remove CONH0ST.EXE
Wie Sie Ihren PC vor einer reinfected mit verhindern “CONH0ST.EXE” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “CONH0ST.EXE”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “CONH0ST.EXE”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “CONH0ST.EXE”.







