Et helt nyt, Virkelig usikker kryptovaluta-minearbejdervirus er faktisk blevet opdaget af forskere inden for sikkerhed og sikkerhed. den malware, hedder Ztem.exe kan forurene målramte ved at bruge en række forskellige måder. Hovedpointen bag Ztem.exe-minearbejderen er at bruge kryptovaluta-minearbejder på computere fra patienter med henblik på at erhverve Monero-tokens til målomkostninger. The outcome of this miner is the raised electricity expenses and if you leave it for longer amount of times Ztem.exe might also damage your computers elements.
Ztem.exe: distributionssystemer Metoder
Det Ztem.exe malware gør brug af 2 populære tilgange, der bruges til at inficere computermål:
- Payload Levering hjælp Prior Infektioner. If an older Ztem.exe malware is released on the sufferer systems it can instantly upgrade itself or download a newer version. Dette er muligt ved hjælp af den indbyggede opgradering kommando, som opnår lanceringen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. The downloaded infection will certainly get the name of a Windows service as well as be put in the “%systemet% temp” placere. Crucial residential or commercial properties as well as running system configuration files are altered in order to allow a relentless and quiet infection.
- Software sårbarhed udnytter. The latest variation of the Ztem.exe malware have been discovered to be triggered by the some exploits, populært anerkendt for at blive udnyttet i ransomware strikes. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som opsøger hvis porten er åben. If this condition is fulfilled it will scan the service and also obtain details concerning it, consisting of any version as well as configuration information. Foretagsomheder såvel som fremtrædende brugernavne og adgangskoder kan blandes. Når brugen af er udløst i forhold til risikokoden, vil minearbejderen helt sikkert blive indsat i tillæg til bagdøren. Dette vil helt sikkert give det en dobbelt infektion.
Besides these approaches other approaches can be used too. Miners can be distributed by phishing emails that are sent out wholesale in a SPAM-like manner and also depend upon social engineering techniques in order to puzzle the targets into believing that they have actually received a message from a legit solution or firm. The infection data can be either directly connected or inserted in the body contents in multimedia content or message web links.
The criminals can additionally create destructive landing pages that can pose supplier download pages, websteder til download af websteder og forskellige andre ofte tilgængelige steder. When they use similar sounding domain to reputable addresses and safety and security certificates the individuals might be pushed right into connecting with them. I nogle tilfælde blot at åbne dem kan forårsage minearbejder infektion.
An additional technique would certainly be to make use of haul providers that can be spread out making use of those techniques or by means of file sharing networks, BitTorrent er en af de mest populære dem. It is often used to disperse both genuine software and also data as well as pirate content. To af en af de mest prominente nyttelast luftfartsselskaber er følgende:
Various other methods that can be taken into consideration by the lawbreakers include using internet browser hijackers -unsafe plugins which are made suitable with the most prominent web internet browsers. They are uploaded to the relevant databases with phony individual testimonials as well as designer qualifications. I mange tilfælde beskrivelserne kan bestå af screenshots, videos as well as sophisticated descriptions appealing great function enhancements as well as efficiency optimizations. Nonetheless upon setup the habits of the impacted web browsers will certainly alter- individuals will certainly discover that they will be rerouted to a hacker-controlled landing web page and their setups may be altered – standard startside, søgemaskine og nye faner webside.
Ztem.exe: Analyse
The Ztem.exe malware is a timeless case of a cryptocurrency miner which relying on its configuration can create a variety of unsafe actions. Its primary objective is to do intricate mathematical jobs that will take advantage of the offered system sources: CPU, GPU, hukommelse samt harddisk plads. The method they function is by attaching to an unique web server called mining pool where the needed code is downloaded and install. Så snart en af opgaverne er hentet det vil helt sikkert blive startet på samme tid, flere forekomster kan køres på, når. When a provided job is completed another one will be downloaded in its location and the loophole will continue till the computer system is powered off, infektionen er fjernet eller en supplerende sammenlignelig lejlighed finder sted. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres tegnebøger.
A dangerous characteristic of this classification of malware is that samples like this one can take all system sources and also practically make the target computer system pointless until the risk has actually been entirely eliminated. A lot of them include a persistent installment which makes them truly hard to remove. Disse kommandoer vil helt sikkert gøre ændringer også valg, configuration files and also Windows Registry values that will make the Ztem.exe malware start automatically when the computer is powered on. Access to recovery food selections and options may be blocked which makes several manual elimination overviews almost pointless.
Denne specifikke infektion vil konfigurationshåndtering en Windows løsning for sig selv, adhering to the carried out protection analysis ther following activities have been observed:
. During the miner operations the connected malware can connect to already running Windows services as well as third-party installed applications. By doing so the system managers might not observe that the source lots originates from a different process.
| Navn | Ztem.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Ztem.exe |
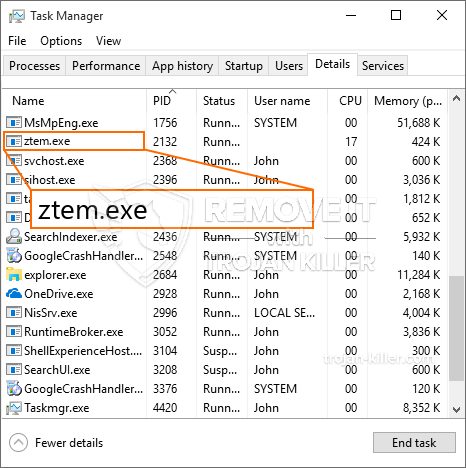
id =”81624″ align =”aligncenter” width =”600″]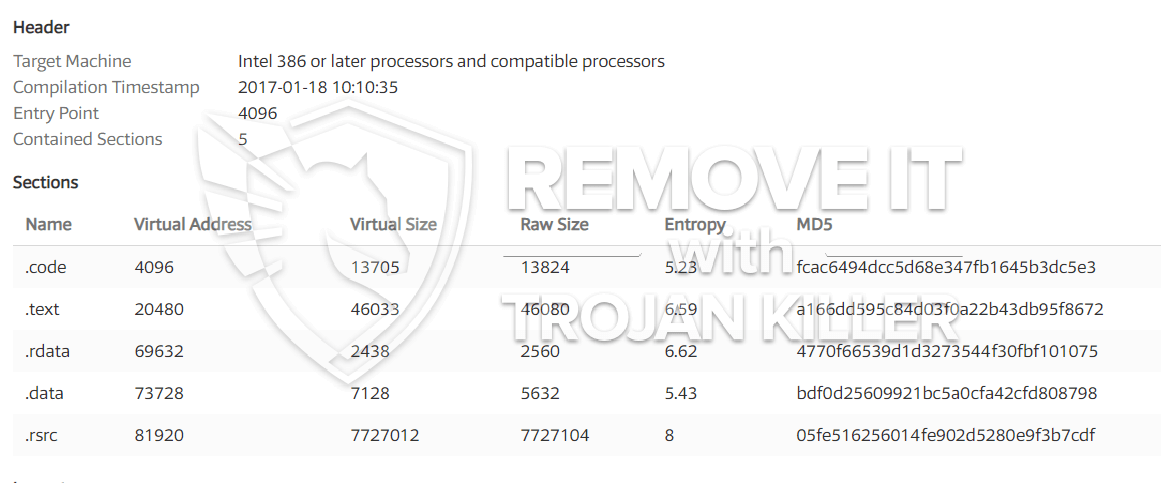 Ztem.exe
Ztem.exe
These sort of malware infections are specifically effective at carrying out sophisticated commands if set up so. They are based on a modular structure permitting the criminal controllers to manage all sort of unsafe habits. Blandt de foretrukne tilfælde er modifikationen af Registry Windows – adjustments strings connected by the os can trigger major performance disruptions as well as the inability to accessibility Windows services. Depending on the range of adjustments it can additionally make the computer completely unusable. On the various other hand control of Registry values coming from any third-party mounted applications can undermine them. Some applications may fail to introduce altogether while others can all of a sudden quit working.
Denne specifikke miner i sin nuværende variation er koncentreret om minedrift af Monero cryptocurrency med en ændret variation af XMRig CPU-minedriftmotor. If the projects confirm successful after that future variations of the Ztem.exe can be released in the future. Da de malware gør brug af software program susceptabilities forurene mål værter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Elimination of Ztem.exe is highly recommended, because you take the chance of not only a large power bill if it is operating on your PC, yet the miner may also perform various other unwanted tasks on it and also even harm your COMPUTER completely.
Ztem.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Ztem.exe
TRIN 5. Ztem.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Ztem.exe
Hvordan undgår din pc fra at blive inficeret med “Ztem.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Ztem.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Ztem.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Ztem.exe”.