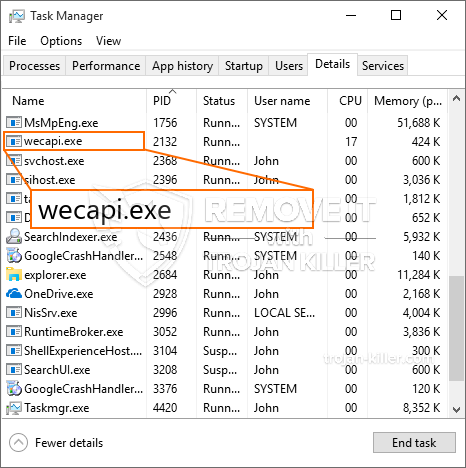
Et helt nyt, meget usikker cryptocurrency minearbejder virus er blevet spottet af sikkerhed og sikring forskere. den malware, hedder Wecapi.exe can contaminate target sufferers using a selection of means. Hovedideen bag Wecapi.exe-minearbejderen er at udnytte cryptocurrency-minearbejder på computersystemer til mål for at opnå Monero-symboler til målomkostninger. The end result of this miner is the raised electrical power expenses and if you leave it for longer time periods Wecapi.exe may also damage your computer systems parts.
Wecapi.exe: distributionssystemer Metoder
Det Wecapi.exe malware benytter sig af to fremtrædende tilgange, der bruges til at forurene computermål:
- Payload Levering gennem Prior Infektioner. If an older Wecapi.exe malware is released on the sufferer systems it can automatically update itself or download and install a more recent version. Dette er muligt ved hjælp af den integrerede opdateringskommando, som henter udgivelsen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den downloadede virus får navnet på en Windows-løsning og placeres også i “%systemet% temp” Beliggenhed. Vigtige bygninger og også operativsystemets konfigurationsdokumenter transformeres for at tillade en vedvarende og også stille infektion.
- Software sårbarhed udnytter. The most recent version of the Wecapi.exe malware have actually been discovered to be triggered by the some ventures, almindeligt anerkendt for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert scanne tjenesten og gendanne oplysninger om den, bestående af enhver version og også arrangementsoplysninger. Ventures og også fremtrædende brugernavn samt adgangskodekombinationer kan gøres. Når udnyttelsen er forårsaget versus den sårbare kode, vil minearbejderen helt sikkert blive installeret sammen med bagdøren. Dette vil give den en dobbelt infektion.
Udover disse metoder kan der også gøres brug af forskellige andre strategier. Minearbejdere kan distribueres af phishing-e-mails, der sendes engros på en SPAM-lignende måde og også stole på social engineering-metoder for at pusle ofrene til at tro, at de faktisk har modtaget en besked fra en ægte løsning eller virksomhed. Infektionsfilerne kan enten anbringes direkte eller placeres i kropsindholdet i multimediewebindhold eller tekstweblinks.
Forbryderne kan også producere destruktive touchdown-websider, der kan efterligne leverandørens download- og installationssider, websteder til download af software og forskellige andre ofte tilgåede steder. Når de gør brug af lignende domænenavne som legitime adresser samt beskyttelsescertifikater, kan kunderne blive tvunget til at kommunikere med dem. I nogle tilfælde bare åbne dem kan modregne minearbejder infektion.
En anden tilgang ville være at bruge transportudbydere, der kan spredes ved at bruge disse metoder eller via netværk til deling af dokumenter, BitTorrent er en af en af de mest foretrukne dem. Det bliver jævnligt brugt til at distribuere både ægte softwareapplikationer og filer samt piratwebindhold. 2 af en af de mest populære nyttelast udbydere er følgende:
Andre metoder, der kan overvejes af de uretfærdige, omfatter brug af internetbrowser hijackers - farlige plugins, som er gjort egnede med de mest foretrukne webbrowsere. De uploades til de relevante databaser med falske individuelle vidnesbyrd og også udviklerkvalifikationer. I mange tilfælde kan resuméerne bestå af skærmbilleder, videoklip samt indviklede resuméer, der lover store funktionsforbedringer og også effektivitetsoptimeringer. Men ved afbetaling vil vanerne for de påvirkede browsere helt sikkert ændre sig- enkeltpersoner vil helt sikkert finde, at de vil blive omdirigeret til en hacker-kontrolleret landingsside, og deres indstillinger kan også ændres – standard startside, søgemaskine samt helt nye side faner.

Wecapi.exe: Analyse
The Wecapi.exe malware is a classic situation of a cryptocurrency miner which depending upon its configuration can create a wide range of harmful activities. Its major goal is to execute complex mathematical jobs that will certainly capitalize on the readily available system sources: CPU, GPU, hukommelse samt harddisk område. The method they work is by linking to a special web server called mining pool from where the needed code is downloaded and install. As quickly as one of the jobs is downloaded it will be begun simultaneously, adskillige tilfælde kan køres på når. When a given task is finished another one will be downloaded in its place and the loop will proceed up until the computer is powered off, infektionen fjernes, eller der opstår en anden lignende begivenhed. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres punge.
An unsafe quality of this category of malware is that samples such as this one can take all system sources as well as almost make the sufferer computer system unusable up until the danger has been entirely removed. A lot of them feature a persistent installation that makes them really difficult to remove. Disse kommandoer vil helt sikkert foretage justeringer for at starte valg, arrangement documents and also Windows Registry values that will certainly make the Wecapi.exe malware start automatically as soon as the computer system is powered on. Access to recovery food selections as well as alternatives might be blocked which makes many hand-operated elimination overviews virtually ineffective.
Denne vis infektion vil helt sikkert sætte en Windows-tjeneste for sig selv, following the carried out safety analysis ther following actions have actually been observed:
. During the miner operations the linked malware can attach to currently running Windows services and also third-party installed applications. By doing so the system administrators may not see that the source lots originates from a different procedure.
| Navn | Wecapi.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Wecapi.exe |

These kind of malware infections are especially effective at performing sophisticated commands if set up so. They are based on a modular framework enabling the criminal controllers to coordinate all type of harmful behavior. Et af de populære eksempler er ændringen af Windows-registreringsdatabasen – alterations strings associated by the os can trigger significant efficiency disruptions and also the failure to gain access to Windows services. Depending on the extent of adjustments it can likewise make the computer completely pointless. On the various other hand adjustment of Registry values belonging to any third-party mounted applications can undermine them. Some applications may fall short to release entirely while others can unexpectedly stop working.
This particular miner in its existing variation is concentrated on extracting the Monero cryptocurrency consisting of a changed variation of XMRig CPU mining engine. If the campaigns verify effective then future versions of the Wecapi.exe can be introduced in the future. Da de malware gør brug af software program susceptabilities forurene mål værter, det kan være del af en skadelig co-infektion med ransomware samt trojanske heste.
Removal of Wecapi.exe is strongly suggested, given that you take the chance of not only a huge electrical power expense if it is working on your COMPUTER, however the miner might also perform other unwanted tasks on it as well as also harm your COMPUTER permanently.
Wecapi.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Wecapi.exe
TRIN 5. Wecapi.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Wecapi.exe
Hvordan undgår din pc fra at blive inficeret med “Wecapi.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Wecapi.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Wecapi.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Wecapi.exe”.







