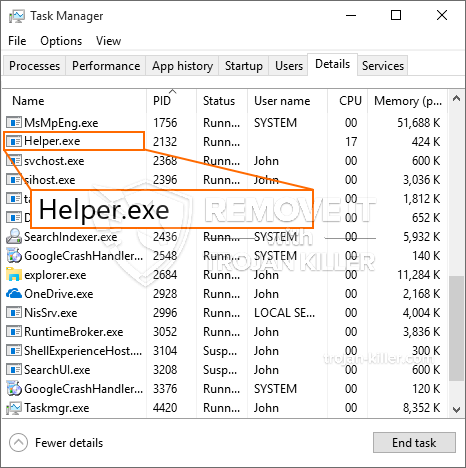
En ny, meget usikker cryptocurrency minearbejder virus er blevet identificeret af sikkerhedsmæssige forskere. den malware, hedder Helper.exe kan inficere ofre mål udnytte et udvalg af midler. Det vigtigste punkt bag Helper.exe minearbejder er at udnytte cryptocurrency minearbejder opgaver på edb-systemerne i syge med henblik på at opnå Monero tokens på ofrene udgifter. Resultatet af denne minearbejder er de forhøjede el-udgifter, og også hvis du lader det i længere tid Helper.exe kan endda skade din computer-systemer dele.
Helper.exe: distributionssystemer Metoder
Det Helper.exe malware bruger to prominente teknikker, som er gjort brug af til at inficere edb-mål:
- Payload Levering gennem Prior Infektioner. Hvis en ældre Helper.exe malware er indsat på målsystemerne det kan automatisk opgradere sig selv eller downloade en nyere variant. Dette er muligt via den indbyggede opgradering kommando, som får frigivelsen. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den hentet og installere virus vil få navnet på en Windows-løsning samt være placeret i “%systemet% temp” areal. Vigtige bygninger og kører systemkonfigurationsdata ændres for at muliggøre en konsistent og roligt infektion.
- Software sårbarhed udnytter. Den mest aktuelle variation af Helper.exe malware er blevet placeret til at blive udløst af nogle ventures, populært kendt for at blive udnyttet i ransomware overfald. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis problemet er opfyldt, vil kontrollere den service og få også oplysninger om det, herunder enhver form for versionen samt opsætningsdata. Ventures og foretrukne brugernavn og også adgangskode blander kan gøres. Når manipulere skyldes imod den modtagelige kode for minearbejder vil blive udgivet sammen med bagdør. Dette vil danne en dobbelt infektion.
Bortset fra disse tilgange forskellige andre strategier kan gøres brug af også. Minearbejdere kan spredes ved phishing e-mails, der sendes engros i en SPAM-lignende måde samt afhænge af social engineering teknikker for at forvirre ofrene til at tro, at de har fået en besked fra en legit tjeneste eller virksomhed. data virus kan enten lige tilsluttet eller sat i kroppen indhold i multimedie webindhold eller tekst weblinks.
De lovovertrædere kan også producere ondsindede landing websider, der kan efterligner leverandør downloade websider, software applikation downloade portaler og forskellige andre ofte adgang steder. Når de anvender lignende optræder domænenavne til ægte adresser samt sikkerhedscertificeringer kunderne kunne overtales til at engagere med dem. I mange tilfælde bare åbne dem kan modregne minearbejder infektion.
En yderligere metode ville være at gøre brug af træk udbydere, der kan spredes ud at gøre brug af disse teknikker eller ved hjælp af dokumenter, der deler netværk, BitTorrent er blot en af de mest populære. Det er ofte gjort brug af til at sprede både ægte software og data og pirat indhold. To af en af de mest populære distancer udbydere er følgende:
Forskellige andre metoder, der kan tages i betragtning ved de onde nævnes at gøre brug af web-browser flykaprere -hazardous plugins, der er lavet egnet med en af de mest populære webbrowsere. De er sendt til de relevante databaser med falske enkelte anmeldelser og designer kvalifikationer. Oftentimes beskrivelserne kan bestå af skærmbilleder, videoklip og sofistikerede beskrivelser opmuntrende forrygende har forbedringer og også effektiviseringer optimeringer. Ikke desto mindre efter installation vaner påvirket internet-browsere vil ændre- enkeltpersoner vil helt sikkert opdage, at de vil blive omdirigeret til en hacker-kontrolleret landing page samt deres opsætninger kan ændres – standard webside, søgemaskine samt nye faner side.

Helper.exe: Analyse
Den Helper.exe malware er en tidløs tilfælde af en cryptocurrency minearbejder, som afhængig af dens indretning kan udløse en række farlige aktiviteter. Dens primære formål er at udføre komplicerede matematiske job, der vil helt sikkert drage fordel af de tilgængelige systemressourcer: CPU, GPU, hukommelse og også harddisk område. Den måde, de fungerer, er ved at linke til en særlig web-server kaldet minedrift pulje, hvor den opfordrede til koden er downloadet. Så hurtigt som blandt de arbejdspladser downloades det vil helt sikkert blive påbegyndt samtidigt, flere omstændigheder kan være væk, så snart. Når en forudsat job er udført yderligere en vil blive hentet på sin plads og sløjfen vil helt sikkert fortsætte indtil computeren er slukket, infektionen er fjernet eller en mere ens lejlighed forekommer. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking team eller en ensom cyberpunk) direkte til deres pengepung.
En usikker karakteristisk for denne kategori af malware er, at eksemplerne ligner denne kan tage alle systemets kilder og næsten gøre computeren offer meningsløst, indtil truslen er blevet totalt sluppet af. Mange af dem har et vedholdende rate, der gør dem virkelig svært at fjerne. Disse kommandoer vil foretage justeringer også muligheder, setup filer og Windows Registry værdier, der vil gøre det Helper.exe malware begynder automatisk, når computeren er tændt. Adgang til nyttiggørelse mad valg og valgmuligheder er muligvis blokeret, hvilket gør flere håndbetjente fjernelse oversigter praktisk værdiløs.
Denne vis infektion vil helt sikkert arrangement en Windows løsning for sig selv, efter den gennemførte sikkerhed analyse ther overholde aktiviteter er blevet observeret:
. I løbet af minearbejder procedurer den tilhørende malware kan tilslutte op til allerede kører Windows-løsninger og også tredjeparts installerede applikationer. Ved at gøre dette systemets ledere kan ikke mærke, at kilden masser kommer fra en anden procedure.
| Navn | Helper.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware at opdage og fjerne Helper.exe |

Denne type malware infektioner er særligt effektive til at udføre avancerede kommandoer, hvis sat op, så. De er baseret på en modulær struktur gør det muligt for kriminelle controllere til at styre alle former for farlige handlinger. Et af de fremtrædende eksempler er ændringen af Windows-registreringsdatabasen – justeringer strenge forbundet af operativsystemet kan udløse alvorlige effektivitet forstyrrelser og også den manglende evne til tilgængelighed Windows-tjenester. Afhængig af omfanget af tilpasninger, som den kan desuden gøre computeren helt meningsløst. På den anden side regulering af Registry værdier, der tilhører nogen form for tredjeparts monteret programmer kan sabotere dem. Nogle programmer kan stoppe med at arbejde for at frigøre helt, mens andre pludselig kan afslutte arbejdet.
Denne særlige minearbejder i sin nuværende variation er koncentreret om minedrift Monero cryptocurrency have en ændret version af XMRig CPU minedrift motor. Hvis projekterne verificere effektive derefter fremtidige variationer af Helper.exe kan indføres i fremtiden. Da malware bruger software program susceptabilities at forurene mål værter, det kan være en del af et farligt co-infektion med ransomware og også trojanske heste.
Fjernelse af Helper.exe er meget anbefales, i betragtning af at du risikerer ikke kun en enorm magt omkostninger, hvis det kører på din PC, men minearbejder kan desuden gøre andre uønskede aktiviteter på det og også endda skade din PC helt.
Helper.exe fjernelsesprocessen
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne Helper.exe
TRIN 5. Helper.exe Fjernet!
Video guide: Sådan bruger GridinSoft Anti-Malware til fjerne Helper.exe
Hvordan undgår din pc fra at blive inficeret med “Helper.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Helper.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Helper.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Helper.exe”.







