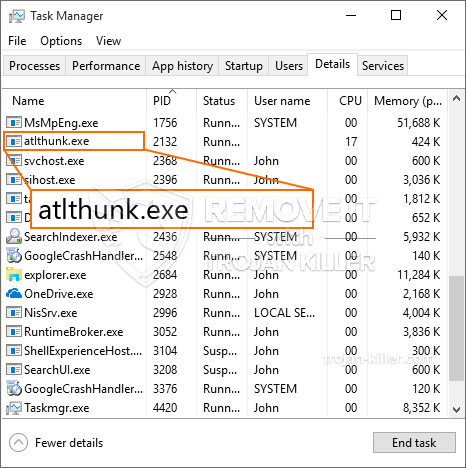
En ny, meget farlig kryptokurrency-minearbejdervirus er blevet set af sikkerheds- og sikkerhedsforskere. den malware, hedder Atlthunk.exe kan forurene ofre mål udnytte et udvalg af midler. Hovedpunktet bag Atlthunk.exe-minearbejderen er at bruge kryptovaluta-mineropgaver på ofrenes computere for at erhverve Monero-tokens til målpris. The outcome of this miner is the elevated power costs and also if you leave it for longer amount of times Atlthunk.exe might also damage your computers parts.
Atlthunk.exe: distributionssystemer Metoder
Det Atlthunk.exe malware udnytter 2 prominent approaches which are made use of to infect computer targets:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Atlthunk.exe malware is released on the sufferer systems it can immediately update itself or download a more recent version. Dette er muligt gennem den integrerede opgraderingskommando, der får lanceringen. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede server, som tilbyder den malware kode. The downloaded virus will obtain the name of a Windows service and also be placed in the “%systemet% temp” placere. Vital buildings as well as operating system setup data are transformed in order to allow a persistent and also quiet infection.
- Software programmet sårbarhed udnytter. The most recent variation of the Atlthunk.exe malware have been discovered to be caused by the some ventures, widely recognized for being used in the ransomware attacks. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Overgrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. If this problem is satisfied it will certainly check the solution and also get info about it, including any variation as well as arrangement information. Exploits and also prominent username as well as password combinations might be done. When the make use of is caused against the prone code the miner will certainly be released along with the backdoor. Dette vil bestemt præsentere en dobbelt infektion.
Bortset fra disse teknikker kan andre strategier også bruges. Miners can be dispersed by phishing emails that are sent in bulk in a SPAM-like manner and also rely on social design methods in order to perplex the targets into believing that they have obtained a message from a legit solution or company. Virussdokumenterne kan enten være direkte forbundet eller placeres i kropsmaterialet i multimediemateriale eller meddelelsesweblinks.
The crooks can additionally create harmful touchdown pages that can pose vendor download web pages, software program download portals and various other regularly accessed locations. When they use comparable sounding domain to reputable addresses as well as protection certifications the users may be pushed into connecting with them. I nogle tilfælde bare åbne dem kan modregne minearbejder infektion.
Another strategy would certainly be to use haul carriers that can be spread using those methods or through file sharing networks, BitTorrent er en af de mest fremtrædende dem. It is frequently used to disperse both reputable software and also documents and pirate content. To af en af de mest populære træk udbydere er følgende:
Various other approaches that can be thought about by the bad guys include making use of internet browser hijackers -hazardous plugins which are made compatible with one of the most popular web internet browsers. They are uploaded to the pertinent repositories with fake customer reviews as well as programmer qualifications. I mange tilfælde resuméerne kan omfatte skærmbilleder, videos and intricate descriptions encouraging terrific feature enhancements and also performance optimizations. Nonetheless upon setup the actions of the impacted browsers will certainly alter- customers will find that they will certainly be redirected to a hacker-controlled touchdown web page and also their setups may be modified – standard webside, søgemaskine og splinternye faneblad.

Atlthunk.exe: Analyse
The Atlthunk.exe malware is a traditional case of a cryptocurrency miner which depending upon its configuration can create a variety of hazardous actions. Its primary goal is to execute intricate mathematical tasks that will certainly benefit from the offered system sources: CPU, GPU, hukommelse og også harddisk område. The way they work is by connecting to an unique server called mining swimming pool from where the required code is downloaded and install. Så hurtigt som blandt opgaverne er hentet det vil helt sikkert blive startet samtidigt, flere tilfælde kan udføres ved så snart. When a provided job is finished one more one will certainly be downloaded and install in its area as well as the loophole will certainly proceed until the computer system is powered off, infektionen fjernes, eller der opstår en anden sammenlignelig hændelse. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres pengepung.
An unsafe feature of this classification of malware is that examples like this one can take all system resources as well as almost make the sufferer computer pointless up until the danger has been completely eliminated. Most of them feature a persistent setup which makes them really difficult to get rid of. Disse kommandoer vil foretage ændringer til at starte valg, configuration files and Windows Registry values that will certainly make the Atlthunk.exe malware start instantly as soon as the computer is powered on. Access to healing menus as well as choices may be blocked which renders lots of manual elimination overviews practically pointless.
Denne specifikke infektion vil arrangementet en Windows løsning for sig selv, overholdelse af den udførte sikkerhedsanalyse og overholdelse af handlinger er blevet observeret:
. During the miner operations the associated malware can connect to already running Windows services and also third-party mounted applications. By doing so the system administrators might not observe that the source lots comes from a different process.
| Navn | Atlthunk.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Atlthunk.exe |

These type of malware infections are specifically effective at executing advanced commands if set up so. They are based on a modular framework enabling the criminal controllers to coordinate all type of dangerous behavior. Et af de fremtrædende tilfælde er ændringen af Windows-registreringsdatabasen – adjustments strings connected by the operating system can cause significant performance disturbances as well as the inability to gain access to Windows services. Relying on the range of modifications it can also make the computer totally unusable. On the various other hand manipulation of Registry values coming from any type of third-party installed applications can sabotage them. Some applications might fail to introduce altogether while others can all of a sudden stop working.
This certain miner in its present variation is concentrated on mining the Monero cryptocurrency having a customized version of XMRig CPU mining engine. If the campaigns prove successful then future versions of the Atlthunk.exe can be released in the future. Da malware bruger software program sårbarheder til at inficere target værter, det kan være en del af et farligt co-infektion med ransomware samt trojanske heste.
Removal of Atlthunk.exe is strongly suggested, since you take the chance of not just a huge electrical power expense if it is operating on your PC, but the miner may additionally do other unwanted tasks on it as well as even damage your PC completely.
Atlthunk.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Atlthunk.exe
TRIN 5. Atlthunk.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Atlthunk.exe
Hvordan undgår din pc fra at blive inficeret med “Atlthunk.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Atlthunk.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Atlthunk.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Atlthunk.exe”.







