Et helt nyt, meget farlig kryptokurrency-minearbejde er blevet opdaget af sikkerhedsforskere. den malware, hedder Gpapi.exe can infect target victims utilizing a variety of ways. Essensen bag Gpapi.exe-minearbejderen er at bruge cryptocurrency-minearbejderopgaver på ofrenes computere for at opnå Monero-tokens på ofrets bekostning. The outcome of this miner is the elevated power expenses and also if you leave it for longer time periods Gpapi.exe might even harm your computer systems components.
Gpapi.exe: distributionssystemer Metoder
Det Gpapi.exe malware utilizes two popular approaches which are used to infect computer targets:
- Payload Levering gennem Prior Infektioner. If an older Gpapi.exe malware is deployed on the target systems it can automatically upgrade itself or download a newer variation. Dette er muligt ved hjælp af den integrerede opdateringskommando, som henter udgivelsen. Dette gøres ved at binde sig til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. The downloaded virus will get the name of a Windows solution as well as be placed in the “%systemet% temp” placere. Vital residential or commercial properties and also running system setup files are transformed in order to allow a relentless and also silent infection.
- Software programmet sårbarhed udnytter. The most current version of the Gpapi.exe malware have actually been discovered to be triggered by the some ventures, widely understood for being used in the ransomware assaults. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Strejkerne er automatiseret af en hacker-kontrollerede rammer, som ser op, hvis porten er åben. If this problem is fulfilled it will check the service and retrieve information about it, bestående af enhver form for variation samt installationsdata. Udnytter og fremtrædende brugernavn og adgangskode blandinger kan gøres. When the exploit is triggered against the vulnerable code the miner will certainly be released together with the backdoor. Dette vil præsentere en dobbelt infektion.
In addition to these approaches other methods can be used as well. Miners can be dispersed by phishing emails that are sent in bulk in a SPAM-like fashion and rely on social engineering tricks in order to confuse the sufferers right into thinking that they have actually obtained a message from a legit service or business. The infection data can be either directly connected or put in the body contents in multimedia content or message web links.
The bad guys can also develop harmful landing pages that can pose vendor download web pages, software download websites and various other frequently accessed areas. When they use comparable appearing domain to legitimate addresses and protection certifications the users may be pushed into engaging with them. I nogle tilfælde kan blot åbning af dem forårsage minearbejdsinfektion.
One more approach would be to utilize payload carriers that can be spread out utilizing those methods or via file sharing networks, BitTorrent er blot en af de mest foretrukne dem. It is regularly used to disperse both reputable software and also documents and also pirate web content. To af de mest populære distancer udbydere er følgende:
Other approaches that can be taken into consideration by the lawbreakers consist of making use of web browser hijackers -hazardous plugins which are made suitable with the most preferred web browsers. They are posted to the appropriate databases with phony user testimonials and programmer credentials. I de fleste tilfælde resuméerne kan omfatte skærmbilleder, videos and also elaborate descriptions encouraging fantastic feature improvements and performance optimizations. Ikke desto mindre, når rate handlinger de påvirkede internet-browsere vil omdanne- users will discover that they will certainly be redirected to a hacker-controlled touchdown web page as well as their settings might be altered – standard startside, søgemaskine på internettet samt nye faner webside.

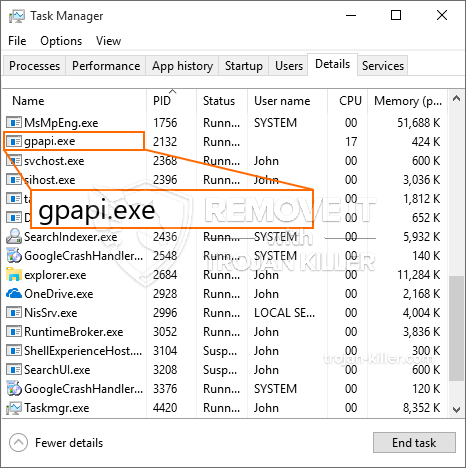
Gpapi.exe: Analyse
The Gpapi.exe malware is a traditional situation of a cryptocurrency miner which depending on its setup can cause a wide range of harmful activities. Dets hovedmål er at udføre komplicerede matematiske opgaver, der gør brug af de let tilgængelige systemkilder: CPU, GPU, hukommelse og også harddisk område. Den måde, de arbejder på, er ved at linke til en unik server kaldet minedrift, hvor den opfordrede kode downloades og installeres. Så snart en af opgaverne er downloadet det vil blive startet på en gang, flere omstændigheder kan udføres ved så snart. Når et givent job er færdigt, vil en mere blive downloadet og installeret i stedet, og smuthullet fortsætter, indtil computeren er slukket, infektionen elimineres, eller der sker en mere sammenlignelig lejlighed. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres tegnebøger.
Et skadeligt træk ved denne kategori af malware er, at prøver som denne kan tage alle systemressourcer samt praktisk talt gøre offerets computersystem ubrugeligt, indtil truslen er helt fjernet. Mange af dem har en vedvarende installation, der gør dem virkelig svære at slippe af med. Disse kommandoer vil helt sikkert gøre ændringer til at starte valg, setup documents as well as Windows Registry values that will certainly make the Gpapi.exe malware begin instantly once the computer system is powered on. Adgang til helbredende madvalg samt valg kan være blokeret, hvilket gør mange praktiske fjernelsesoversigter næsten meningsløse.
Denne særlige infektion vil arrangement en Windows-tjeneste for sig selv, efter den udførte beskyttelsesanalyse, er følgende handlinger blevet observeret:
. Under minearbejderne kan den tilsluttede malware oprette forbindelse til allerede kørende Windows-løsninger og installerede tredjepartsapplikationer. Ved at gøre dette kan systemadministratorerne muligvis ikke opdage, at ressourcebelastningen stammer fra en separat procedure.
| Navn | Gpapi.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Gpapi.exe |

Denne form for malware-infektioner er specifikt effektive til at udføre avancerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontrollører at håndtere alle former for farlig adfærd. En af de foretrukne tilfælde er justeringen af Windows-registreringsdatabasen – ændringsstrenge relateret af OS kan udløse alvorlige ydeevneforstyrrelser og også manglende adgang til Windows-tjenester. Afhængigt af omfanget af justeringer kan det desuden gøre computersystemet helt ubrugeligt. På den anden side kan kontrol af registreringsværdier, der kommer fra tredjepartsprogrammer, sabotere dem. Nogle applikationer holder muligvis op med at fungere for at frigive helt, mens andre pludselig kan stoppe med at fungere.
Denne specifikke minearbejder i sin nuværende variation er koncentreret om at udvinde Monero-kryptovalutaen med en ændret version af XMRig CPU-minemotoren. If the projects verify successful then future versions of the Gpapi.exe can be released in the future. Da malware bruger softwaresårbarheder til at inficere målværter, det kan være en del af en usikker co-infektion med ransomware og trojanske heste.
Elimination of Gpapi.exe is strongly suggested, fordi du tager chancen for ikke kun store elektriske strømomkostninger, hvis den kører på din COMPUTER, men minearbejderen kan desuden udføre andre uønskede opgaver på den og endda beskadige din COMPUTER fuldstændigt.
Gpapi.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Gpapi.exe
TRIN 5. Gpapi.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Gpapi.exe
Hvordan undgår din pc fra at blive inficeret med “Gpapi.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Gpapi.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Gpapi.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Gpapi.exe”.







