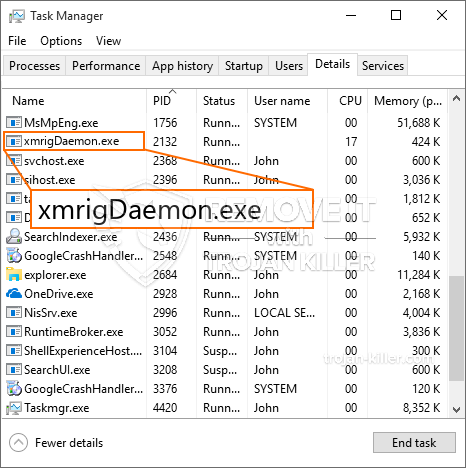
Um novo em folha, realmente infecção mineiro criptomoeda inseguro foi identificado por pesquisadores de segurança. o malware, chamado XmrigDaemon.exe can infect target sufferers making use of a range of ways. O ponto principal por trás do mineiro XmrigDaemon.exe é empregar tarefas criptomoeda mineiro sobre os sistemas de computador de doentes, a fim de obter Monero fichas em despesas sofredores. The outcome of this miner is the raised electricity bills and if you leave it for longer periods of time XmrigDaemon.exe might also damage your computers components.
XmrigDaemon.exe: Métodos de distribuição
o XmrigDaemon.exe malwares utiliza duas técnicas populares que são utilizados para infectar alvos de computador:
- Payload Entrega usando Infecções anteriores. If an older XmrigDaemon.exe malware is deployed on the sufferer systems it can automatically update itself or download and install a newer version. Isto é possível através do comando de atualização integrado que adquire o lançamento. Isto é feito através da ligação a um servidor controlado por hackers predefinido particular que dá o código de malware. O vírus baixado vai ter o nome de um serviço do Windows, bem como ser colocada no “%% Temp sistema” área. edifícios vitais e arquivos arranjo sistema operacional são alteradas de modo a permitir uma infecção implacável e silenciosa.
- Software exploração de vulnerabilidades Programa. The most current variation of the XmrigDaemon.exe malware have been discovered to be brought on by the some ventures, amplamente entendida para ser utilizado nos ataques ransomware. As infecções são feitas por alvo serviços abertos usando a porta TCP. Os ataques são automatizados por um quadro controlado por hackers que procura para fora se a porta é aberta. Se este problema for atendida ele irá verificar a solução e recuperar detalhes sobre ele, que consiste de qualquer variação, bem como dados de configuração. Exploits e nome de usuário popular, bem como misturas de senha pode ser feito. Quando a fazer uso de é imputado o risco código mineiro será lançado em adição ao backdoor. Isso certamente vai apresentar a uma dupla infecção.
Além desses métodos de outros métodos pode ser usado como bem. Mineiros podem ser dispersos por phishing e-mails que são enviados a granel em uma maneira SPAM-like, bem como dependem de métodos de projeto sociais, a fim de confundir o direito das vítimas a pensar que eles têm efectivamente obtida uma mensagem de um verdadeiro serviço ou empresa. Os dados de vírus pode ser de cadeia linear ligado ou colocado nos materiais do corpo no conteúdo da web multimédia ou ligações de mensagens.
Os infratores podem também produzir destrutivas páginas de aterragem da web que pode personificar o download fornecedor e instalar páginas da web, sites de programa de download de software, bem como outros locais freqüentemente acessados. Quando usar o domínio sonoridade parecida com os endereços originais, bem como certificações de segurança dos indivíduos pode ser coagida a se envolver com eles. Em alguns casos simplesmente abri-los pode ativar a infecção mineiro.
Uma estratégia adicional seria certamente usar provedores de serviços de transporte que podem ser espalhados utilizando essas abordagens ou através de redes de compartilhamento de arquivos, BitTorrent é apenas um dos mais proeminentes. É frequentemente utilizado para dispersar tanto programa de software legítimo e dados e também o conteúdo da web pirata. Dois dos provedores de curso mais populares são os seguintes:
Várias outras abordagens que podem ser pensado pelos bandidos consistem no uso de navegador de internet sequestradores plugins -unsafe que são feitas compatível com um dos navegadores de internet web mais proeminentes. Eles são submetidos aos repositórios apropriados com falsos comentários de clientes e também credenciais de programador. Na maioria dos casos, os resumos podem incluir screenshots, vídeos, bem como descrições intricadas atraentes excelentes aprimoramentos de recursos e também otimizações de eficiência. No entanto após a prestação das ações dos navegadores de internet impactados vai alterar- indivíduos certamente vai achar que eles vão certamente ser redirecionado para uma página de aterrissagem web controlado por hackers e também as suas configurações pode ser alterada – a página inicial padrão, motor de pesquisa e novas guias página web.

XmrigDaemon.exe: Análise
The XmrigDaemon.exe malware is a classic situation of a cryptocurrency miner which depending on its arrangement can cause a variety of unsafe activities. Its major goal is to perform complicated mathematical tasks that will certainly capitalize on the readily available system resources: CPU, GPU, memória e também área de disco rígido. The method they work is by connecting to an unique server called mining pool from where the called for code is downloaded and install. Tão rapidamente como entre as tarefas é baixado ele será iniciado imediatamente, várias instâncias podem ser ido pela primeira vez. When a given job is completed one more one will be downloaded in its location and also the loop will proceed till the computer system is powered off, a infecção é removido ou um evento comparável adicional acontece. Criptomoeda certamente será recompensado aos controladores criminais (grupo de hackers ou de um cyberpunk solitária) diretamente para suas carteiras.
A harmful quality of this classification of malware is that examples like this one can take all system sources and practically make the victim computer system unusable until the threat has been totally eliminated. A lot of them feature a consistent installation which makes them really difficult to remove. Estes comandos certamente vai fazer alterações para arrancar escolhas, configuration data as well as Windows Registry values that will make the XmrigDaemon.exe malware beginning automatically once the computer system is powered on. Accessibility to healing food selections and options may be blocked which renders lots of hand-operated elimination guides almost ineffective.
Esta infecção específica certamente arranjo uma solução Windows para si, adhering to the carried out security analysis ther following actions have been observed:
. Durante os procedimentos mineiro o malware associado pode ligar para já em execução soluções Windows e aplicativos também de terceiros instalados. By doing so the system administrators might not see that the source load comes from a different procedure.
| Nome | XmrigDaemon.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware to detect and remove XmrigDaemon.exe |

Esses tipos de infecções por malware são especialmente eficientes na execução de comandos inovadores se configurados de forma. They are based on a modular structure enabling the criminal controllers to manage all type of hazardous habits. Entre os exemplos populares é a modificação do Registro do Windows – alterations strings associated by the operating system can create severe efficiency disturbances and the inability to accessibility Windows services. Depending upon the range of changes it can additionally make the computer system totally unusable. Por vários outros manipulação mão de Valores do Registro vindo de qualquer tipo de terceiros configurar aplicativos podem sabotar-los. Alguns aplicativos podem ficar aquém de lançar inteiramente enquanto outros podem de repente parar de trabalhar.
This specific miner in its current version is focused on extracting the Monero cryptocurrency including a changed variation of XMRig CPU mining engine. If the campaigns verify successful after that future versions of the XmrigDaemon.exe can be launched in the future. Como o malware utiliza susceptabilities software para contaminar anfitriões alvo, ele pode ser componente de uma co-infecção perigosa com ransomware e também Trojans.
Elimination of XmrigDaemon.exe is highly recommended, considering that you risk not only a large electrical energy costs if it is running on your PC, yet the miner may also carry out various other unwanted activities on it and also damage your COMPUTER permanently.
XmrigDaemon.exe removal process
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” button to remove XmrigDaemon.exe
Degrau 5. XmrigDaemon.exe Removed!
Guia de vídeo: How to use GridinSoft Anti-Malware for remove XmrigDaemon.exe
Como evitar que o seu PC seja infectado novamente com “XmrigDaemon.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “XmrigDaemon.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “XmrigDaemon.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “XmrigDaemon.exe”.







