Um novo em folha, vírus de minerador de criptomoeda extremamente perigoso foi encontrado por cientistas de proteção. o malware, chamado Lsass2.exe pode infectar vítimas-alvo utilizando uma variedade de métodos. A essência por trás do minerador Lsass2.exe é empregar atividades do minerador de criptomoeda nos computadores das vítimas para obter tokens Monero às custas das vítimas. The outcome of this miner is the elevated electrical power expenses and also if you leave it for longer time periods Lsass2.exe might also damage your computer systems components.
Lsass2.exe: Métodos de distribuição
o Lsass2.exe malware utilizes two preferred techniques which are utilized to contaminate computer targets:
- Payload Entrega através de infecções anteriores. If an older Lsass2.exe malware is released on the sufferer systems it can instantly update itself or download a newer variation. This is possible using the built-in upgrade command which acquires the release. Isso é feito conectando-se a um servidor específico controlado por hacker predefinido que fornece o código do malware. A infecção baixado e instalar certamente vai obter o nome de uma solução Windows e ser colocado no “%% Temp sistema” área. Crucial residential or commercial properties as well as running system arrangement data are changed in order to allow a consistent and also silent infection.
- Software exploração de vulnerabilidades de aplicativos. The newest variation of the Lsass2.exe malware have actually been discovered to be caused by the some exploits, widely understood for being made use of in the ransomware strikes. As infecções são feitas por alvo serviços abertos usando a porta TCP. Os ataques são automatizados por uma estrutura controlada hacker que procura se a porta é aberta. If this problem is met it will check the solution and fetch info regarding it, consisting of any kind of variation and also setup data. Ventures and prominent username and password mixes might be done. When the make use of is set off against the susceptible code the miner will be released along with the backdoor. Isto irá fornecer a uma infecção dupla.
Apart from these techniques various other approaches can be used too. Miners can be dispersed by phishing e-mails that are sent out in bulk in a SPAM-like fashion as well as rely on social engineering techniques in order to puzzle the sufferers right into thinking that they have obtained a message from a legitimate service or company. The infection data can be either straight connected or inserted in the body contents in multimedia content or text web links.
The criminals can additionally develop malicious touchdown web pages that can pose supplier download web pages, software application download websites as well as other regularly accessed locations. When they make use of similar sounding domain names to legit addresses as well as safety certificates the users may be coerced into communicating with them. Em alguns casos, apenas abri-los pode desencadear a infecção mineiro.
Another technique would certainly be to make use of payload carriers that can be spread utilizing the above-mentioned approaches or via data sharing networks, BitTorrent é um dos mais preferidos. It is regularly used to distribute both legitimate software application as well as data and also pirate material. 2 de um dos transportadores de carga útil mais preferidos são os seguintes:
Various other methods that can be taken into consideration by the bad guys consist of using internet browser hijackers -unsafe plugins which are made suitable with the most popular web internet browsers. They are uploaded to the relevant repositories with fake customer reviews and also programmer qualifications. Na maioria dos casos, os resumos podem incluir screenshots, videos as well as intricate summaries promising terrific attribute enhancements and also efficiency optimizations. Nevertheless upon installment the habits of the affected browsers will certainly alter- customers will certainly discover that they will be rerouted to a hacker-controlled landing page and also their settings could be changed – a página web padrão, motor de pesquisa e também a página web novas guias.
Lsass2.exe: Análise
The Lsass2.exe malware is a traditional instance of a cryptocurrency miner which relying on its arrangement can trigger a variety of unsafe actions. Its primary objective is to execute complex mathematical tasks that will make use of the available system sources: CPU, GPU, memória e também área de disco rígido. The means they operate is by connecting to a special web server called mining swimming pool where the called for code is downloaded. Tão rapidamente como uma das tarefas é baixado será iniciado simultaneamente, numerosas circunstâncias pode ficar fora por uma vez. When a provided job is finished an additional one will certainly be downloaded and install in its location and also the loophole will proceed until the computer is powered off, a infecção é eliminada ou mais um evento semelhante acontece. Criptomoeda será recompensado aos controladores criminais (Hacker equipe ou um cyberpunk solitária) direto para suas carteiras.
A hazardous attribute of this category of malware is that examples such as this one can take all system resources and practically make the victim computer pointless until the danger has actually been entirely gotten rid of. Most of them include a persistent installment which makes them truly challenging to eliminate. Estes comandos certamente vai fazer modificações para arrancar escolhas, configuration documents and also Windows Registry values that will certainly make the Lsass2.exe malware begin instantly once the computer is powered on. Accessibility to healing menus and choices may be blocked which provides lots of hand-operated elimination guides virtually useless.
Esta determinada infecção certamente configuração um serviço do Windows por si mesmo, conformidade com a avaliação de segurança realizada, tendo sido observado o cumprimento das atividades:
. During the miner procedures the associated malware can hook up to currently running Windows solutions as well as third-party mounted applications. By doing so the system administrators may not discover that the source tons comes from a different process.
| Nome | Lsass2.exe |
|---|---|
| Categoria | troiano |
| Subcategoria | criptomoeda Miner |
| perigos | alto uso da CPU, redução de velocidade à Internet, PC trava e congela e etc. |
| Propósito principal | Para ganhar dinheiro para os criminosos cibernéticos |
| Distribuição | torrents, Jogos grátis, Aplicativos Cracked, O email, sites duvidosos, exploits |
| Remoção | Instalar GridinSoft Anti-Malware to detect and remove Lsass2.exe |
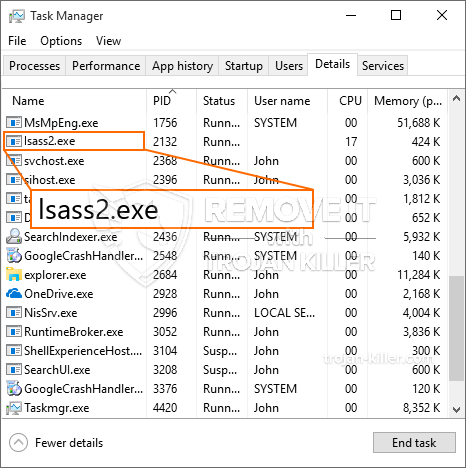
id =”81268″ alinhar =”aligncenter” largura =”600″] Lsass2.exe
Lsass2.exe
Este tipo de infecções por malware são especificamente eficazes na execução de comandos inovadores, se configurado para. They are based upon a modular structure permitting the criminal controllers to coordinate all sort of hazardous habits. Entre os exemplos preferidos é a alteração do Registro do Windows – adjustments strings associated by the os can create serious efficiency disruptions and also the lack of ability to access Windows services. Depending upon the extent of adjustments it can likewise make the computer system completely unusable. On the other hand adjustment of Registry values belonging to any type of third-party mounted applications can undermine them. Some applications may stop working to introduce completely while others can all of a sudden stop working.
This specific miner in its present variation is focused on extracting the Monero cryptocurrency consisting of a customized variation of XMRig CPU mining engine. If the projects verify effective then future versions of the Lsass2.exe can be introduced in the future. Como o malware utiliza susceptabilities software para contaminar anfitriões alvo, pode ser parte de uma co-infecção perigosos com ransomware e Trojans.
Removal of Lsass2.exe is strongly advised, because you risk not only a large electricity bill if it is working on your COMPUTER, however the miner might also perform various other undesirable tasks on it and even damage your PC completely.
Lsass2.exe removal process
Degrau 1. Em primeiro lugar, você precisa baixar e instalar GridinSoft Anti-Malware.
Degrau 2. Em seguida, você deve escolher “Escaneamento rápido” ou “Verificação completa”.
Degrau 3. Corra para analisar o seu computador
Degrau 4. Após a verificação for concluída, você precisa clicar em “Aplique” button to remove Lsass2.exe
Degrau 5. Lsass2.exe Removed!
Guia de vídeo: How to use GridinSoft Anti-Malware for remove Lsass2.exe
Como evitar que o seu PC seja infectado novamente com “Lsass2.exe” no futuro.
Uma solução poderoso antivírus que pode detectar e malware bloco fileless é o que você precisa! As soluções tradicionais detectar malware com base em definições de vírus, e, portanto, eles muitas vezes não consegue detectar “Lsass2.exe”. GridinSoft Anti-Malware oferece proteção contra todos os tipos de malware, incluindo malwares fileless tais como “Lsass2.exe”. GridinSoft Anti-Malware fornece analisador de comportamento baseado em nuvem para bloquear todos os arquivos desconhecidos, incluindo malware zero dia. Essa tecnologia pode detectar e remover completamente “Lsass2.exe”.