Um número de vulnerabilidades foram identificadas no FreeBSD e Linux pilhas TCP que potencialmente permitir remotamente causando uma negação de serviço ou causar o consumo de recursos excessivo durante o processamento de pacotes TCP especialmente criados.
Problems exist due to errors in the handler of the maximum data block size in the TCP packet (MSS, O tamanho máximo do segmento) and the mechanism for selective acknowledgment of TCP SACK. These vulnerabilities can pose a threat to a significant number of devices, including servers, Android gadgets, and embedded devices.CVE-2019-11477 (SACK Panic) – this problem affects the Linux kernel, starting with version 2.6.29, and allows causing kernel crash by sending a series of SACK packets, which will cause an integer overflow in the handler. To prevent exploitation of the vulnerability, users are advised to disable SACK processing (escrever 0 para /proc/sys/net/ipv4/tcp_sack) or block connections with a small MSS (the measure is effective only if you set sysctl net.ipv4.tcp_mtu_probing para 0 and can lead to disruption some normal compounds with low MSS).
CVE-2019-11478 (SACK Slowness) – affects Linux kernel below 4.15 and leads to a failure of the SACK mechanism or excessive consumption of resources. It can be exploited by sending a series of specially crafted SACK packets.
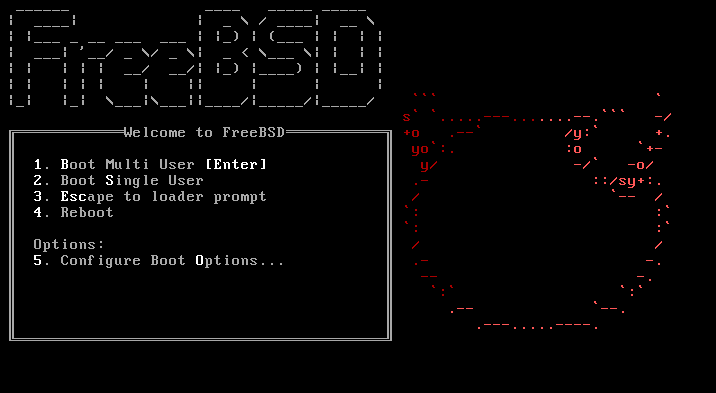
CVE-2019-5599 (SACK Slowness) – manifested in FreeBSD 12 with the RACK packet loss detection mechanism. This problem allows fragmentation of a map of sent packets when processing a specially crafted SACK sequence within a single TCP connection. To prevent exploitation of the vulnerability, it is recommended to disable the RACK module.
CVE-2019-11479 – affects all versions of the Linux kernel. An attacker in the Linux kernel can cause responses to be split into several TCP segments, each of which includes only 8 bytes of data. This leads to a significant increase in traffic and Consumption of additional resources.
Vulnerabilities are fixed in versions of the Linux kernel 4.4.182, 4.9.182, 4.14.127, 4.19.52 e 5.1.11. A patch for FreeBSD is also available. Kernel pack updates are released for Debian, RHEL, SUSE / openSUSE, ALT, Ubuntu, Fedora, and Arch Linux.
Good system and application coding and configuration practices (limiting write buffers to the necessary level, monitoring connection memory consumption via SO_MEMINFO, and aggressively closing misbehaving connections) can help to limit the impact of attacks against these kinds of vulnerabilities.
Fonte: https://www.openwall.com
