En ny, veldig skadelig kryptovaluta-gruvevirus har faktisk blitt oppdaget av sikkerhets- og sikkerhetsforskere. den malware, kalt Wudfhosts.exe kan infisere målet ofrene å gjøre bruk av en rekke måter. Hovedideen bak Wudfhosts.exe-gruvearbeideren er å bruke kryptovalutearbeidere på datamaskinsystemene til pasienter for å få Monero-tokens til kostnad for pasienter. Resultatet av denne gruvearbeideren er de forhøyede strømkostnadene, og hvis du lar den stå i lengre perioder kan Wudfhosts.exe også skade datasystemets deler.
Wudfhosts.exe: distribusjonsmetoder
De Wudfhosts.exe malware bruker to foretrukne tilnærminger som brukes til å forurense datamaskinmål:
- Nyttelast Levering bruke Prior Infeksjoner. Hvis en eldre Wudfhosts.exe-malware utgis på de lidende systemene, kan den umiddelbart oppgradere seg selv eller laste ned og installere en nyere variant. Dette er mulig gjennom den innebygde oppdateringskommandoen som får lanseringen. Dette gjøres ved å koble til en bestemt forhåndsdefinert hacker styrt server som tilveiebringer den skadelige koden. Den nedlastede og installerte infeksjonen vil sikkert få navnet på en Windows-tjeneste og bli satt i “%Systemet% temp” område. Essensielle egenskaper så vel som operativsystemarrangementsfiler transformeres for å tillate en konsekvent så vel som stille infeksjon.
- Programvare Utnytter Program for sikkerhetsproblem. Den nyeste versjonen av Wudfhosts.exe skadelig programvare har blitt lokalisert for å bli utløst av noen utnyttelser, famously anerkjent for å bli tatt i bruk i ransomware angrep. Infeksjoner er gjort ved å målrette åpne løsninger gjennom TCP-port. Angrepene er automatiserte av hackere styrt struktur som søker etter om porten er åpen. Hvis denne betingelsen er oppfylt, vil den skanne løsningen samt gjenopprette informasjon om den, inkludert alle typer variasjoner og også konfigurasjonsdataene. Foretak og også fremtredende brukernavn og passord blandinger kan gjøres. Når manipulasjonen er satt av mot den utsatte koden, vil gruvearbeideren sikkert bli løslatt sammen med bakdøren. Dette vil sikkert gi en dobbel infeksjon.
I tillegg til disse teknikkene kan forskjellige andre strategier også brukes. Gruvearbeidere kan distribueres ved phishing-e-poster som sendes ut i engros på en SPAM-lignende måte, i tillegg til at de er avhengige av sosiale designteknikker for å forvirre pasientene rett til å tro at de har fått en melding fra en ekte tjeneste eller virksomhet. Virusfilene kan enten vedlegges direkte eller legges inn i kroppsmaterialet i multimedienettinnhold eller meldingslenker.
Skurkene kan i tillegg produsere skadelige landingssider som kan etterligne leverandørnedlasting og installering av nettsider, nettsteder for nedlasting av programvare og forskjellige andre ofte tilgjengelige områder. Når de bruker lignende domene som anerkjente adresser samt sikkerhetssertifikater, kan kundene bli tvunget rett til å kommunisere med dem. I mange tilfeller kan det bare føre til gruvearbeid å åpne dem.
En ekstra tilnærming ville være å bruke transportleverandører som kan spres ut ved å bruke disse teknikkene eller gjennom dokumentdelingsnettverk, BitTorrent er en av de mest foretrukne. Det brukes ofte til å spre både anerkjent programvare og data og piratinnhold. To av de mest fremtredende nyttelast bærere er følgende:
Ulike andre tilnærminger som kan vurderes av overtredere inkluderer bruken av nettleserkaprere - usikre plugins som er laget egnet med de mest fremtredende nettleserne. De publiseres til de relevante depotene med falske individuelle attester så vel som designerlegitimasjon. Ofte kan beskrivelsene inkludere skjermbilder, videoklipp og fancy beskrivelser tiltalende flotte funksjonsforbedringer og også ytelsesoptimaliseringer. Ikke desto mindre vil oppførselen til de påvirkede nettleserne endres ved oppsett- kunder vil helt sikkert oppdage at de vil bli omdirigert til en hackerkontrollert landingsside, i tillegg til at oppsettene deres kan bli endret – standard startside, søkemotor og nye faner siden.

Wudfhosts.exe: Analyse
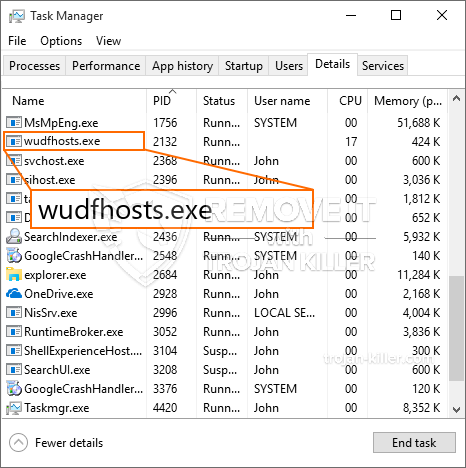
Wudfhosts.exe malware er en tradisjonell situasjon for en kryptovaluta-gruvearbeider som avhengig av konfigurasjonen kan skape et bredt spekter av farlige aktiviteter. Dens primære mål er å gjøre kompliserte matematiske jobber som vil få mest mulig ut av de tilgjengelige systemkildene: prosessor, GPU, minne samt harddisk rom. Metoden de fungerer er ved å koble til en unik webserver kalt mining pool hvor den nødvendige koden lastes ned. Så raskt som en av jobbene er lastet ned vil det bli startet samtidig, flere forekomster kan kjøres på en gang. Når en gitt oppgave er fullført, vil en ekstra en sikkert bli lastet ned i stedet, og smutthullet vil sikkert fortsette til datamaskinen slås av, infeksjonen er blitt kvitt eller en mer sammenlignbare hendelsen finner sted. Kryptovaluta vil bli kompensert for den kriminelle kontrollerne (hacking gruppe eller en enkelt hackere) direkte til sine vesker.
Et farlig kjennetegn ved denne klassifiseringen av skadevare er at eksempler som dette kan ta alle systemkilder og praktisk talt gjøre den lidende datamaskinen ubrukelig inntil risikoen er fullstendig fjernet. De fleste av dem inkluderer en vedvarende installasjon som gjør dem veldig vanskelige å eliminere. Disse kommandoene vil gjøre endringer også valg, oppsettfiler og også Windows-registerverdier som vil gjøre at Wudfhosts.exe skadelig programvare starter umiddelbart så snart datamaskinen slås på. Tilgang til utvalg av rekreasjonsmat så vel som alternativer kan bli hindret, noe som gjør flere manuelle fjerningsoversikter praktisk talt verdiløse.
Denne infeksjonen vil sikkert konfigurasjons en Windows-løsning for seg selv, etter den utførte sikkerhetsanalysen er det observert at det er i samsvar med aktiviteter:
. Under gruvedriften kan den tilknyttede skadelige programvaren feste seg til Windows-løsninger som kjører for øyeblikket, så vel som tredjeparts oppsettprogrammer. Ved å gjøre det kan det hende at systemansvarlige ikke oppdager at kildebelastningen stammer fra en separat prosedyre.
| Navn | Wudfhosts.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Wudfhosts.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre innovative kommandoer hvis de er konfigurert slik. De er basert på en modulær struktur som tillater de kriminelle kontrollørene å orkestrere alle slags farlige handlinger. Blant de foretrukne tilfellene er endringen av Windows-registeret – justeringsstrenger knyttet til OS kan utløse betydelige effektivitetsforstyrrelser og manglende evne til tilgjengelighet av Windows-løsninger. Avhengig av utvalget av endringer kan det i tillegg gjøre datamaskinen helt meningsløs. På den annen side kan manipulering av registerverdier som kommer fra alle slags tredjepartsoppsettprogrammer undergrave dem. Noen programmer kan slutte å virke for å frigis fullstendig, mens andre uventet kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin nåværende versjon er konsentrert om å utvinne Monero-kryptovalutaen med en tilpasset variant av XMRig CPU-gruvemotoren. Hvis prosjektene viser effektive, kan fremtidige varianter av Wudfhosts.exe utgis i fremtiden. Som malware bruker programvare sårbarheter forurense målet verter, det kan være en del av en skadelig samtidig infeksjon med ransomware samt trojanere.
Eliminering av Wudfhosts.exe anbefales på det sterkeste, gitt at du risikerer ikke bare store strømkostnader hvis den fungerer på DATAMASKINEN din, men gruvearbeideren kan også utføre forskjellige andre uønskede oppgaver på den, i tillegg til å skade DATAMASKINEN din permanent.
Wudfhosts.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” for å fjerne Wudfhosts.exe
SKRITT 5. Wudfhosts.exe er fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Wudfhosts.exe
Hvor å forhindre din PC blir infisert med “Wudfhosts.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Wudfhosts.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Wudfhosts.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Wudfhosts.exe”.







