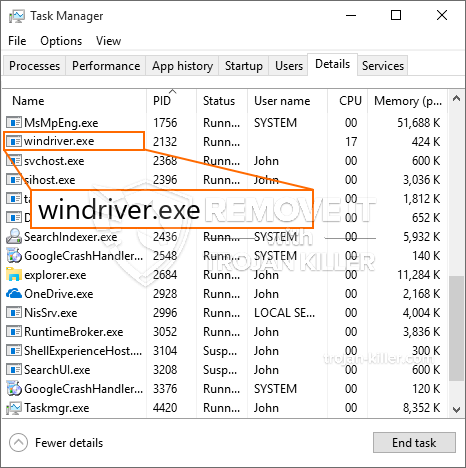
En ny, veldig skadelig kryptovaluta miner virus har blitt oppdaget av sikkerhetsforskere. den malware, kalt Windriver.exe kan forurense målet ofre ved hjelp av et utvalg av måter. Essensen bak Windriver.exe-gruvearbeideren er å bruke kryptovaluta-gruvearbeidere på datamaskinene til målene for å skaffe seg Monero-symboler til lidende bekostning. The outcome of this miner is the elevated power bills and if you leave it for longer periods of time Windriver.exe might even harm your computer systems components.
Windriver.exe: distribusjonsmetoder
De Windriver.exe malware uses two popular approaches which are utilized to contaminate computer targets:
- Nyttelast Levering ved hjelp av tidligere infeksjoner. If an older Windriver.exe malware is released on the target systems it can automatically upgrade itself or download and install a newer variation. This is possible via the built-in upgrade command which obtains the launch. Dette gjøres ved å koble til en spesifikk forhåndsdefinert hackerkontrollert webserver som leverer skadevarekoden. The downloaded and install infection will get the name of a Windows solution as well as be positioned in the “%Systemet% temp” sted. Crucial residential properties as well as running system configuration documents are altered in order to allow a consistent and also silent infection.
- Programvare Utnytter Program for sikkerhetsproblem. The most current variation of the Windriver.exe malware have been located to be triggered by the some exploits, famously understood for being made use of in the ransomware assaults. Infeksjoner er gjort ved å målrette åpne løsninger ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt rammeverk som søker etter om porten er åpen. If this condition is fulfilled it will certainly scan the service and fetch details concerning it, inkludert alle typer versjon og også ordningen informasjon. Foretak og fremtredende brukernavn samt passordkombinasjoner kan gjøres. When the manipulate is caused against the prone code the miner will be deployed together with the backdoor. Dette vil gi en dobbel infeksjon.
Aside from these methods various other methods can be made use of too. Miners can be distributed by phishing e-mails that are sent out wholesale in a SPAM-like way and depend on social engineering methods in order to perplex the victims right into believing that they have gotten a message from a legitimate service or firm. The infection files can be either directly attached or placed in the body components in multimedia content or message web links.
The offenders can likewise develop harmful touchdown pages that can impersonate vendor download and install pages, nettsteder for nedlasting av programvare og andre områder som ofte brukes. When they make use of similar seeming domain names to genuine addresses and protection certifications the users may be coerced right into communicating with them. I noen tilfeller bare åpne dem kan sette av miner infeksjon.
One more technique would certainly be to use haul carriers that can be spread out utilizing those methods or via documents sharing networks, BitTorrent er blant de mest foretrukne. It is often utilized to distribute both genuine software program and data as well as pirate material. 2 av en av de mest fremtredende hale tjenesteleverandører er følgende:
Various other methods that can be taken into consideration by the wrongdoers include using web browser hijackers -dangerous plugins which are made suitable with the most preferred internet browsers. They are posted to the relevant repositories with fake user evaluations and also developer qualifications. I mange tilfeller beskrivelsene kan inkludere skjermbilder, videos as well as sophisticated summaries promising terrific feature enhancements and efficiency optimizations. Nonetheless upon setup the habits of the impacted browsers will alter- customers will discover that they will be redirected to a hacker-controlled touchdown web page and their settings could be altered – standard startside, online søkemotor og splitter nye faner nettside.

Windriver.exe: Analyse
The Windriver.exe malware is a traditional situation of a cryptocurrency miner which depending upon its arrangement can create a wide range of dangerous activities. Its major objective is to carry out complicated mathematical jobs that will take advantage of the available system resources: prosessor, GPU, minne samt harddisk rom. The method they operate is by connecting to an unique server called mining swimming pool from where the called for code is downloaded and install. Så raskt som blant oppgavene lastes ned, vil den startes med en gang, flere forhold kan kjøres samtidig. When a provided job is finished another one will be downloaded in its place as well as the loop will certainly continue up until the computer is powered off, infeksjonen blir fjernet eller en mer sammenlignbar hendelse oppstår. Kryptovaluta vil sikkert bli kompensert for den kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) rett til sine lommebøker.
A dangerous characteristic of this classification of malware is that samples like this one can take all system sources and also practically make the victim computer system pointless up until the threat has been entirely gotten rid of. The majority of them feature a persistent setup that makes them actually tough to remove. Disse kommandoene vil selvfølgelig gjøre endringer også valg, setup data and also Windows Registry values that will certainly make the Windriver.exe malware begin automatically as soon as the computer system is powered on. Accessibility to healing menus and choices might be obstructed which makes many manual removal overviews virtually worthless.
Denne spesielle infeksjonen vil sette opp en Windows-løsning for seg selv, following the performed safety evaluation ther complying with actions have been observed:
. During the miner operations the linked malware can attach to already running Windows services and also third-party mounted applications. By doing so the system managers might not notice that the resource lots comes from a different procedure.
| Navn | Windriver.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Windriver.exe |

These kind of malware infections are specifically efficient at accomplishing sophisticated commands if configured so. They are based on a modular framework allowing the criminal controllers to manage all kinds of unsafe behavior. En av de populære eksemplene er justering av Windows-registeret – modifications strings related by the os can create significant performance interruptions as well as the failure to gain access to Windows services. Depending on the extent of changes it can also make the computer system entirely pointless. På den annen side kan justering av registerverdier som kommer fra tredjeparts installerte applikasjoner undergrave dem. Some applications might fail to launch altogether while others can suddenly quit working.
This particular miner in its existing variation is focused on extracting the Monero cryptocurrency consisting of a changed version of XMRig CPU mining engine. If the campaigns show effective then future versions of the Windriver.exe can be released in the future. Som malware benytter programvare susceptabilities å infisere målet verter, det kan være bestanddel av en farlig samtidig infeksjon med ransomware og også trojanere.
Elimination of Windriver.exe is highly recommended, considering that you take the chance of not only a large power bill if it is running on your PC, yet the miner might likewise carry out other unwanted tasks on it as well as also damage your COMPUTER completely.
Windriver.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Windriver.exe
SKRITT 5. Windriver.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Windriver.exe
Hvor å forhindre din PC blir infisert med “Windriver.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Windriver.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Windriver.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Windriver.exe”.







