En helt ny, svært usikre kryptovaluta miner virus har faktisk blitt oppdaget av sikkerhetsforskere. den malware, kalt Vcc2.exe kan forurense målofre på forskjellige måter. Hovedpoenget bak Vcc2.exe miner er å bruke kryptovaluta miner aktiviteter på datasystemene til mål for å få Monero symboler på ofrene utgifter. Resultatet av denne gruvearbeideren er de høye elektriske strømkostnadene, så vel som om du lar det ligge over lengre tid. Vcc2.exe kan til og med skade datamaskinens elementer.
Vcc2.exe: distribusjonsmetoder
De Vcc2.exe malware bruksområder 2 populære tilnærminger som brukes for å infisere datamaskinsystemmål:
- Nyttelast Levering ved hjelp av tidligere infeksjoner. Hvis en eldre Vcc2.exe malware er distribuert på offersystemene, kan den umiddelbart oppgradere seg selv eller laste ned og installere en nyere variant. Dette er mulig ved å bruke den integrerte oppdatert kommando som oppnår frigjøring. Dette gjøres ved å knytte til en bestemt forhåndsdefinert hacker-kontrollert webserver som leverer malware-koden. Den nedlastede og installere infeksjonen vil sikkert få navnet på en Windows-tjeneste og også være plassert i “%Systemet% temp” plassering. Viktige boligeiendommer og oppsettdata for operativsystemet endres for å tillate en nådeløs og lydløs infeksjon.
- Utnytter programvare for sikkerhetsproblem. Den siste variasjonen av Vcc2.exe-skadelig programvare har faktisk funnet å bli brakt videre av noen utnyttelser, populært anerkjent for å bli brukt i ransomware-angrepene. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt struktur som søker etter om porten er åpen. Hvis denne betingelsen er oppfylt, vil den skanne løsningen og også hente informasjon om den, inkludert alle typer versjons- og arrangementsdata. Utnyttelser og populære brukernavn samt passordkombinasjoner kan gjøres. Når bruken er satt av kontra den utsatte koden, skal gruvearbeideren distribueres i tillegg til bakdøren. Dette vil gi den en dobbel infeksjon.
I tillegg til disse tilnærmingene kan andre tilnærminger også brukes. Gruvearbeidere kan spres ved hjelp av phishing-e-post som sendes i bulk på en SPAM-lignende måte og er avhengige av sosialtekniske teknikker for å forvirre de syke rett til å tro at de har fått en melding fra en legitim løsning eller selskap. Infeksjonsfilene kan enten kobles direkte eller plasseres i innholdet i kroppen i multimedia webinnhold eller meldingslenker.
Skurkene kan i tillegg utvikle skadelige berøringssider som kan utgjøre leverandørens nedlasting og installere websider, laste ned nettsteder for programvare, så vel som andre steder som ofte er tilgjengelige. Når de bruker lignende tilsynelatende domene til anerkjente adresser og også sikkerhets- og sikkerhetssertifikater, kan brukerne bli presset til å koble seg til dem. Noen ganger er bare å åpne dem kan utløse miner infeksjonen.
En annen tilnærming vil absolutt være å bruke transportører som kan spres ved å bruke de ovennevnte metodene eller ved å bruke datadelingsnettverk, BitTorrent er en av de mest foretrukne. Det blir jevnlig benyttet til å distribuere både ekte programvare og dokumenter og også piratinnhold. 2 av de mest prominente hale leverandører er følgende:
Andre metoder som de kriminelle kan ta i betraktning, består i å bruke kapere av nettlesere - farlige plugins som er gjort egnet med en av de mest populære nettleserne.. De lastes opp til de relevante depotene med falske individuelle anmeldelser og også programmererkvalifikasjoner. Ofte sammendragene kan inkludere skjermbilder, videoer samt fancy sammendrag som lover utmerkede attribusforbedringer og ytelsesoptimaliseringer. Ikke desto mindre vil vanene til de påvirkede nettleserne sikkert installeres ved installasjonen- brukere vil sikkert oppdage at de vil bli omdirigert til en hacker-kontrollert touchdown-side, og også oppsettene deres kan bli endret – standard startside, online søkemotor og nye faner nettside.

Vcc2.exe: Analyse
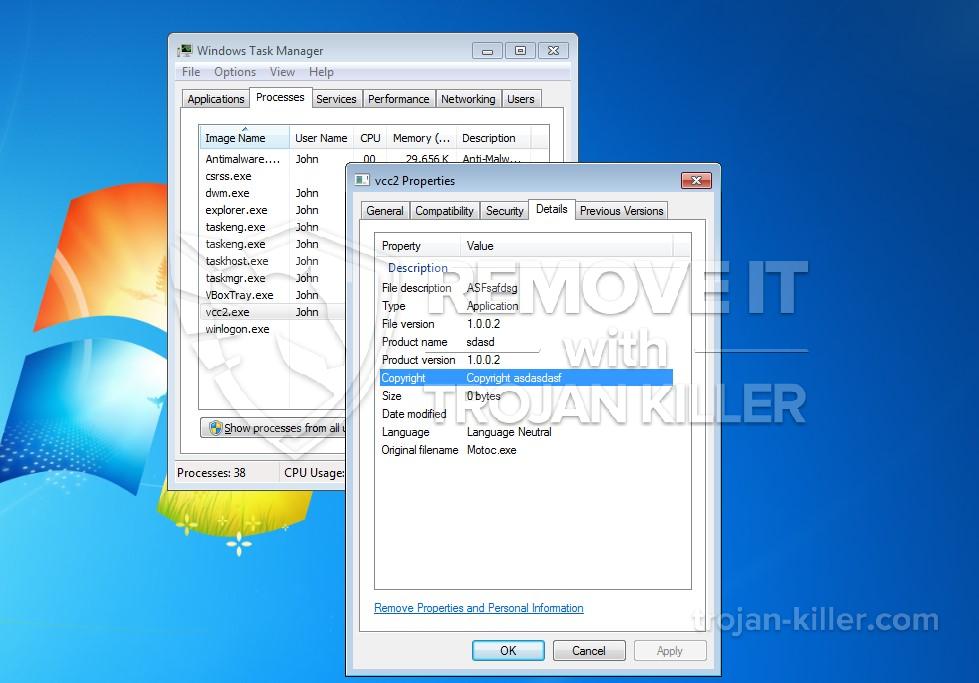
Vcc2.exe-malware er et tidløst tilfelle av en cryptocurrency-gruvearbeider, som avhengig av konfigurasjonen kan utløse en lang rekke usikre aktiviteter. Hovedmålet er å utføre kompliserte matematiske oppgaver som vil gjøre bruk av de lett tilgjengelige systemkildene: prosessor, GPU, minne og også harddiskområdet. Måten de opererer på er ved å koble til en unik server som heter mining swimming pool hvor den krevde koden lastes ned og installeres. Så snart en av jobbene er lastet ned, vil den helt sikkert startes samtidig, mange tilfeller kan være borte for når. Når en gitt oppgave er ferdig vil en til sikkert bli lastet ned på sin plassering, og loopen vil også fortsette til datamaskinen er slått av, infeksjonen blir kvitt eller en annen sammenlignbar anledning oppstår. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) rett til deres vesker.
Et utrygt attributt for denne kategorien malware er at eksempler som denne kan ta alle systemkilder og også praktisk talt gjøre det lidende datasystemet ubrukelig til faren er helt fjernet. De fleste av dem inkluderer en jevn avbetaling som gjør dem virkelig vanskelig å bli kvitt. Disse kommandoene vil selvfølgelig gjøre endringer også alternativer, ordningsdokumenter og Windows-registerverdier som sikkert vil gjøre at Vcc2.exe-skadelig programvare starter umiddelbart når datasystemet er slått på. Tilgang til helbredende menyer og alternativer kan hindres, noe som gir flere praktiske eliminasjonsveiledninger praktisk ineffektive.
Denne spesielle infeksjonen vil sikkert sette opp en Windows-løsning for seg selv, etterlevelse av den utførte sikkerhetsanalysen har etterlevelse av aktiviteter blitt observert:
. Under gruveprosedyrene kan den tilknyttede skadelig programvaren koble seg til allerede kjørte Windows-tjenester så vel som tredjepartsmonterte applikasjoner. Ved å gjøre det kan det hende at systemansvarlige ikke legger merke til at ressursbelastningen kommer fra en annen prosess.
| Navn | Vcc2.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Vcc2.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på en modulær struktur som tillater kriminelle kontrollører å håndtere alle slags farlige vaner. Blant de populære eksempler er endring av Windows-registeret – justeringsstrenger tilknyttet operativsystemet kan skape betydelige effektivitetsforstyrrelser og også mangelen på tilgjengelighet Windows-løsninger. Avhengig av omfanget av endringer kan det på samme måte gjøre datamaskinen helt meningsløs. På den annen side kan manipulering av registerverdier som tilhører tredjeparts konfigurerte applikasjoner, sabotere dem. Noen applikasjoner kan ikke komme til å starte helt, mens andre uventet kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin nåværende versjon er konsentrert om å gruve Monero cryptocurrency som inneholder en tilpasset versjon av XMRig CPU gruvedrift motor. Hvis kampanjene blir effektive etter at fremtidige versjoner av Vcc2.exe kan lanseres i fremtiden. Som malware bruker programmet susceptabilities å forurense målet verter, det kan være bestanddel av en usikker samtidig infeksjon med ransomware og trojanere.
Eliminering av Vcc2.exe foreslås sterkt, fordi du ikke bare risikerer en enorm elektrisk energikostnad hvis den opererer på PC-en, men gruvearbeideren kan i tillegg utføre andre uønskede oppgaver på den, og til og med skade PCen din fullstendig.
Vcc2.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” for å fjerne Vcc2.exe
SKRITT 5. Vcc2.exe fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Vcc2.exe
Hvor å forhindre din PC blir infisert med “Vcc2.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Vcc2.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Vcc2.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Vcc2.exe”.







