En helt ny, veldig farlig kryptovaluta-gruveinfeksjon har blitt oppdaget av sikkerhetsforskere. den malware, kalt Logs.exe kan forurense målrammede ved hjelp av en rekke midler. The main idea behind the Logs.exe miner is to utilize cryptocurrency miner activities on the computer systems of victims in order to obtain Monero tokens at victims expense. The outcome of this miner is the elevated electrical energy expenses as well as if you leave it for longer time periods Logs.exe might even harm your computers components.
Logs.exe: distribusjonsmetoder
De Logs.exe malware bruker to fremtredende metoder som brukes til å infisere datamaskinsmål:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older Logs.exe malware is deployed on the victim systems it can automatically update itself or download and install a newer variation. Dette er mulig via den innebygde oppdateringskommandoen som kjøper utgivelsen. Dette gjøres ved å feste til en spesiell forhånds hacker styrt web-server som gir den skadelige koden. Det nedlastede viruset vil skaffe seg navnet på en Windows-tjeneste og bli lagt i “%Systemet% temp” område. Viktige egenskaper så vel som oppsettdokumenter for operativsystemet endres for å tillate en nådeløs og lydløs infeksjon.
- Utnytter programvare for sikkerhetsproblem. The latest variation of the Logs.exe malware have been found to be caused by the some ventures, ofte kjent for å være brukt i ransomware-angrepene. Infeksjoner er gjort ved å målrette åpne tjenester via TCP port. Overfallene er automatiserte av hackere styrt rammeverk som søker etter om porten er åpen. Hvis dette problemet oppfylles, vil det skanne løsningen og også få informasjon om det, bestående av hvilken som helst versjon samt oppsettinformasjon. Ventures så vel som fremtredende brukernavn og passordkombinasjoner kan gjøres. Når bruken er forårsaket mot den utsatte koden, vil gruvearbeideren absolutt bli distribuert sammen med bakdøren. Dette vil gi en dobbel infeksjon.
I tillegg til disse teknikkene kan forskjellige andre teknikker også brukes. Gruvearbeidere kan spres ved hjelp av phishing-e-post som sendes engros på en SPAM-lignende måte, samt avhenger av triks for sosialt design for å forvirre ofrene til å tro at de faktisk har fått en melding fra en anerkjent tjeneste eller et selskap. Infeksjonsfilene kan enten kobles direkte eller plasseres i kroppsinnholdet i multimediainnhold eller tekstlenker.
Forbrytere kan i tillegg produsere ondsinnede touchdown-sider som kan utgi seg for nedlastingssider fra leverandører, programvare nedlastingsportaler og også forskjellige andre steder som ofte er tilgjengelige. Når de bruker et tilsvarende domene som vises til ekte adresser og sikkerhetssertifikater, kan individene overtales til å koble seg til dem. I noen tilfeller kan bare å åpne dem aktivere gruveinfeksjonen.
En annen teknikk vil absolutt være å benytte transporttjenesteleverandører som kan spres ut ved hjelp av ovennevnte metoder eller via fildelingsnettverk., BitTorrent er bare en av en av de mest populære. Den brukes regelmessig til å distribuere både legit programvare og dokumenter og piratnettinnhold. 2 av de mest prominente hale leverandører er følgende:
Andre tilnærminger som kan vurderes av lovbryterne består i å bruke nettleserkaprere - farlige plugins som er egnet for en av de mest populære nettleserne. De blir publisert i aktuelle databaser med falske brukeranmeldelser og designerkvalifikasjoner. I mange tilfeller sammendragene kan bestå av skjermbilder, videoklipp og også utførlige sammendrag som tiltalende fantastiske attributtforbedringer og effektivitetsoptimaliseringer. Likevel vil oppførselen til de berørte nettleserne endres etter installasjonen- enkeltpersoner vil oppdage at de vil bli omdirigert til en hackerkontrollert touchdown-side, i tillegg til at innstillingene deres kan endres – standard startside, Internett-søkemotor, og også helt nye faner nettside.

Logs.exe: Analyse
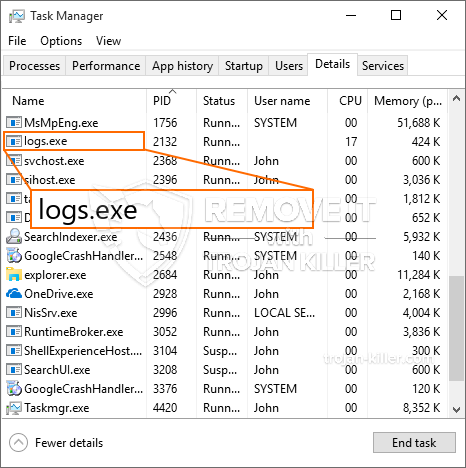
The Logs.exe malware is a classic situation of a cryptocurrency miner which depending on its arrangement can trigger a wide range of harmful actions. Its primary goal is to perform intricate mathematical tasks that will certainly benefit from the available system sources: prosessor, GPU, minne og harddisk område. The method they function is by attaching to an unique server called mining pool where the required code is downloaded and install. Så snart en av jobbene er lastet ned, vil den absolutt bli startet samtidig, multiple instances can be run at when. When an offered task is finished one more one will certainly be downloaded in its area and also the loophole will certainly continue up until the computer system is powered off, infeksjonen er fjernet, eller en mer lik hendelse finner sted. Kryptovaluta vil sikkert deles ut til de kriminelle kontrollerne (hacking team eller en enkelt hacker) rett til sine budsjetter.
A dangerous quality of this group of malware is that samples similar to this one can take all system resources and almost make the target computer system pointless until the risk has been entirely removed. The majority of them include a relentless installment that makes them actually difficult to get rid of. Disse kommandoene vil selvfølgelig gjøre endringer i oppstartsalternativer, setup files and also Windows Registry values that will certainly make the Logs.exe malware begin immediately as soon as the computer is powered on. Access to recovery menus and also choices might be obstructed which renders many hand-operated removal overviews virtually useless.
Denne spesifikke infeksjonen vil sette opp en Windows-tjeneste for seg selv, etter gjennomført beskyttelse analyse ther følgende handlinger har blitt observert:
. During the miner operations the associated malware can connect to already running Windows services and also third-party set up applications. Ved å gjøre det, vil systemadministratorene kanskje ikke oppdage at kildelottene kommer fra en egen prosess.
| Navn | Logs.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Logs.exe |

These type of malware infections are particularly reliable at carrying out sophisticated commands if configured so. De er basert på en modulær struktur som gjør det mulig for kriminelle kontrollere å håndtere alle slags farlige handlinger. Blant de foretrukne tilfellene er endringen av Windows-registeret – modifications strings related by the operating system can create severe efficiency disruptions and the failure to accessibility Windows solutions. Depending on the scope of changes it can additionally make the computer entirely pointless. On the various other hand control of Registry worths coming from any type of third-party installed applications can undermine them. Noen programmer kan unnlate å innføre helt mens andre kan plutselig slutte å fungere.
This particular miner in its existing variation is concentrated on extracting the Monero cryptocurrency containing a changed variation of XMRig CPU mining engine. If the projects confirm effective then future versions of the Logs.exe can be released in the future. Som malware gjør bruk av programvare applikasjons susceptabilities forurense målet verter, det kan være en del av en farlig samtidig infeksjon med ransomware samt trojanere.
Removal of Logs.exe is strongly suggested, considering that you run the risk of not just a big electrical energy bill if it is running on your COMPUTER, but the miner might likewise do other undesirable tasks on it and also even damage your COMPUTER completely.
Logs.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Logs.exe
SKRITT 5. Logs.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Logs.exe
Hvor å forhindre din PC blir infisert med “Logs.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Logs.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Logs.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Logs.exe”.







