En ny, virkelig usikre kryptovaluta miner virus har faktisk blitt oppdaget av sikkerhetsforskere. den malware, kalt Jvc.exe kan forurense mål lider hjelp av en rekke måter. Hovedideen bak Jvc.exe miner er å bruke kryptovaluta miner aktiviteter på datasystemene til sufferers for å skaffe Monero symboler på ofrene kostnads. Resultatet av denne gruvearbeideren er de økte strømkostnadene, og hvis du lar det stå i lengre perioder, kan Jvc.exe også skade datamaskinsystemets deler.
Jvc.exe: distribusjonsmetoder
De Jvc.exe malware gjør bruk av 2 foretrukne fremgangsmåter som benyttes for å forurense datasystem mål:
- Nyttelast Levering bruke Prior Infeksjoner. Hvis en eldre Jvc.exe malware blir distribuert på målsystemene, kan den øyeblikkelig oppdatere seg selv eller laste ned og installere en nyere variant. Dette er mulig via den innebygde oppdatert kommando som får frigjørings. Dette gjøres ved å koble til en viss forhåndsdefinert hacker styrt web-server som leverer den skadelige koden. Den lastet ned og installere infeksjon vil sikkert få navnet på en Windows-tjeneste samt plasseres i “%Systemet% temp” plassering. Viktige egenskaper og kjører systemkonfigurasjonsfiler er forvandlet for å tillate en nådeløs samt stille infeksjon.
- Programvare Utnytter Program for sikkerhetsproblem. Den siste versjonen av Jvc.exe malware har blitt oppdaget å være utløst av noen utnyttelser, kjent anerkjent for å bli anvendt i Ransomware angrep. Infeksjonene er gjort ved å målrette åpne løsninger via TCP-port. Angrepene er automatiserte av hackere styrt ramme som søker ut om porten er åpen. Hvis dette problemet er oppfylt vil det sikkert skanne løsningen og også få informasjon om det, bestående av alle slags versjon samt konfigurasjonsinformasjon. Ventures samt foretrukne brukernavn samt passord mikser kan gjøres. Når manipulere aktiveres mot den utsatte koden miner vil bli utplassert sammen med bakdør. Dette vil sikkert gi en dobbel infeksjon.
Bortsett fra disse metodene forskjellige andre metoder kan bli gjort bruk av også. Gruvearbeidere kan bli distribuert av phishing e-poster som sendes engros i en spam-aktig måte, så vel som avhenger sosiale design triks for å forvirre ofrene akkurat til å tro at de faktisk har mottatt en melding fra en ekte løsning eller virksomhet. Virus dokumenter kan være enten rett eller tilkoblet plassert i kroppen innholdet i multimedia materiale eller meldingsforbindelser.
Skurkene kan også lage ondsinnede landing websider som kan etterligne leverandør laste ned nettsider, program nedlasting nettsteder, samt diverse andre regelmessig tilgang til steder. Når de bruker sammenlign vises domenenavn til legit adresser samt beskyttelsessertifikater brukerne kan bli overtalt til å kommunisere med dem. Noen ganger bare åpne dem kan sette av miner infeksjon.
En annen metode ville være å bruke nyttelast leverandører som kan spres ut å utnytte de ovennevnte metoder eller gjennom dokumenter som deler nettverkene, BitTorrent er bare ett av de mest fremtredende. Det er ofte brukt til å distribuere både ekte program og også filer og pirat webinnhold. 2 av en av de mest populære hale leverandører er følgende:
Forskjellige andre metoder som kan vurderes av lovbrytere består av å gjøre bruk av nettleserkaprere -hazardous plugins som er laget passer med de mest populære nettlesere. De er publisert i relevante databaser med falske kunde attester samt designer kvalifikasjoner. I de fleste tilfeller oppsummeringer kan bestå av skjermbilder, videoer og forseggjorte sammendrag oppmuntrende gode funksjonsforbedringer samt effektivitet optimaliseringer. Men ved oppsett vaner av de berørte nettlesere vil sikkert forandre- brukere vil oppdage at de vil sikkert bli omdirigert til en hacker-kontrollert landing nettside samt deres oppsett kan endres – standard nettside, søkemotor og nye faner siden.

Jvc.exe: Analyse
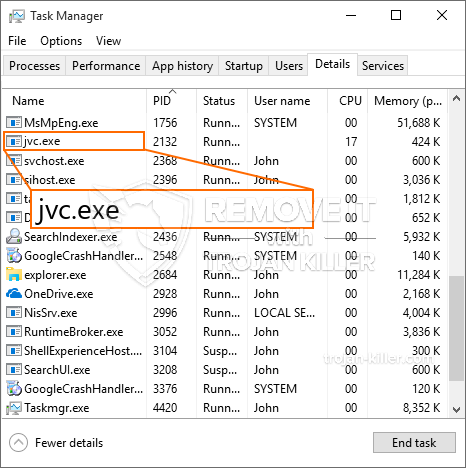
Jvc.exe-skadelig programvare er et tradisjonelt tilfelle av en gruvearbeider som avhengig av oppsett kan utløse et bredt spekter av skadelige handlinger. Hovedmålet er å utføre kompliserte matematiske jobber som vil bruke de lett tilgjengelige systemressursene: prosessor, GPU, minne og også plass på harddisken. Midlene de jobber er ved å koble til en spesiell server kalt mining swimming pool hvorfra den nødvendige koden lastes ned. Så snart en av jobbene er lastet ned, vil den bli startet på samme tid, flere omstendigheter kan være borte for når. Når en gitt oppgave er ferdig, vil en annen sikkert lastes ned og installeres i området, og smutthullet vil helt sikkert fortsette til datamaskinen er slått av., infeksjonen er fjernet eller en annen lignende hendelse skjer. Kryptovaluta vil sikkert bli belønnet til de kriminelle kontrollerne (hacking gruppe eller en enslig cyberpunk) direkte til sine vesker.
En farlig egenskap ved denne klassifiseringen av skadelig programvare er at eksempler som denne kan ta alle systemkilder, så vel som nesten gjøre den lidende datamaskinen meningsløs til risikoen faktisk er fullstendig fjernet. De fleste av dem har en jevn installasjon som gjør dem veldig utfordrende å bli kvitt. Disse kommandoene vil sikkert gjøre justeringer av oppstartsalternativer, konfigurasjonsfiler og Windows-registerverdier som vil gjøre at Jvc.exe-skadeprogrammet begynner umiddelbart når datamaskinen slås på. Tilgjengelighet til valg av mat og alternativer for rekreasjon kan bli blokkert, noe som gjør mange praktiske eliminasjonsguider nesten verdiløse.
Denne spesifikke infeksjonen vil sikkert sette opp en Windows-tjeneste for seg selv, å overholde den utførte beskyttelsesevalueringen der det følges handlinger er faktisk blitt observert:
. Under gruveprosedyrene kan den tilknyttede malware knytte seg til Windows-løsninger som kjører og også tredjepartsmonterte applikasjoner. Ved å gjøre det kan systemadministratorene kanskje ikke se at kildelottene kommer fra en annen prosedyre.
| Navn | Jvc.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Jvc.exe |

Disse type skadelige infeksjoner er særlig effektiv til å utføre kommandoer innovative hvis konfigurert så. De er basert på en modulær struktur som gjør det mulig for kriminelle kontrollører å orkestrere all slags farlig oppførsel. Blant de populære eksemplene er endring av Windows-registeret – modifikasjonsstrenger assosiert med operativsystemet kan forårsake alvorlige ytelsesforstyrrelser, samt manglende tilgang til Windows-løsninger. Avhengig av justeringsomfanget kan det også gjøre datamaskinen helt ubrukelig. På den annen side kan kontroll av registerverdier som kommer fra alle slags tredjepartsapplikasjoner, undergrave dem. Noen applikasjoner kan komme til å bli introdusert helt, mens andre uventet kan slutte å fungere.
Denne bestemte gruvearbeideren i sin nåværende variant er fokusert på gruvedrift av Monero-kryptokurrency med en modifisert variant av XMRig CPU-gruvedriftmotor. Hvis kampanjene verifiserer effektive, kan fremtidige variasjoner av Jvc.exe introduseres i fremtiden. Som malware bruker programvare sårbarheter å infisere målet verter, det kan være en del av en usikker saminfeksjon med ransomware og trojanere.
Fjerning av Jvc.exe anbefales på det sterkeste, gitt at du risikerer ikke bare en enorm strømregning hvis den fungerer på din PC, likevel kan gruvearbeideren også utføre andre uønskede oppgaver på den, og til og med skade DATAMASKINEN din permanent.
Jvc.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” knappen for å fjerne Jvc.exe
SKRITT 5. Jvc.exe fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Jvc.exe
Hvor å forhindre din PC blir infisert med “Jvc.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Jvc.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Jvc.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Jvc.exe”.







