En ny, ekstremt farlig kryptovaluta miner viruset har blitt identifisert av beskyttelse forskere. den malware, kalt Igfx.exe can infect target victims making use of a selection of ways. The main idea behind the Igfx.exe miner is to use cryptocurrency miner tasks on the computers of victims in order to acquire Monero symbols at victims expenditure. The result of this miner is the elevated electricity costs and also if you leave it for longer periods of time Igfx.exe might even damage your computers parts.
Igfx.exe: distribusjonsmetoder
De Igfx.exe malware benytter 2 fremtredende metoder som brukes til å forurense datasystemmål:
- Nyttelast Levering bruke Prior Infeksjoner. If an older Igfx.exe malware is released on the victim systems it can automatically update itself or download and install a more recent variation. Dette er mulig ved å bruke den integrerte oppgraderingskommandoen som henter lanseringen. Dette gjøres ved å koble til en bestemt forhåndsdefinert hackerkontrollert server som gir skadevarekoden. Den nedlastede infeksjon vil få navnet på en Windows-tjeneste og også plasseres i “%Systemet% temp” sted. Viktige bolig- eller næringseiendommer og kjørende systemkonfigurasjonsdata transformeres for å tillate en vedvarende og også stille infeksjon.
- Utnytter programvare for sikkerhetsproblem. The newest version of the Igfx.exe malware have actually been found to be caused by the some exploits, kjent for å ha blitt brukt i ransomware -angrepene. Infeksjonene er gjort ved å målrette åpne løsninger via TCP-port. Angrepene er automatiserte av hackere styrt struktur som søker ut om porten er åpen. Hvis denne betingelsen er oppfylt, vil den sikkert skanne løsningen og gjenopprette detaljer om den, inkludert alle typer variasjoner samt konfigurasjonsdata. Foretak og også foretrukne brukernavn samt passordblandinger kan gjøres. Når manipulasjonen er aktivert mot den utsatte koden, vil gruvearbeideren sikkert bli utplassert i tillegg til bakdøren. Dette vil sikkert tilby en dual-smitte.
Bortsett fra disse metodene kan forskjellige andre strategier også brukes. Gruvearbeidere kan distribueres ved phishing-e-poster som sendes i grossistsalg på en SPAM-lignende måte og er avhengige av sosiale designteknikker for å forvirre pasientene til å tro at de har mottatt en melding fra en ekte tjeneste eller et firma. Virusdokumentene kan enten festes rett eller settes inn i kroppskomponentene i multimediemateriale eller meldingsnettlenker.
De kriminelle kan også utvikle destruktive landingssider som kan etterligne leverandørnedlastingssider, nedlastingsportaler for programvare og også forskjellige andre steder som regelmessig brukes. Når de bruker lignende domene som ekte adresser samt sikkerhetssertifikater, kan brukerne bli tvunget rett til å samhandle med dem. I noen tilfeller kan bare åpning av dem utløse minerinfeksjonen.
En annen tilnærming vil absolutt være å benytte seg av transporttjenesteleverandører som kan spres ut ved hjelp av de ovennevnte teknikkene eller via fildelingsnettverk, BitTorrent er en av en av de mest fremtredende. Det brukes ofte til å distribuere både legitime programvareapplikasjoner så vel som data og også piratnettinnhold. 2 av de mest populære transportleverandørene er følgende:
Ulike andre teknikker som kan tenkes på av kriminelle inkluderer bruk av nettleserkaprere -usikre plugins som er laget egnet med de mest fremtredende nettleserne. De sendes til de aktuelle depotene med falske individuelle anmeldelser og utviklerkvalifikasjoner. I de fleste tilfeller oppsummeringer kan inkludere skjermbilder, videoklipp så vel som intrikate beskrivelser tiltalende fantastiske attributtforbedringer og effektivitetsoptimaliseringer. Likevel ved avbetaling vil handlingene til de berørte nettleserne endres- enkeltpersoner vil sikkert finne at de vil bli omdirigert til en hackerkontrollert destinasjonsside og at oppsettene deres kan endres – standard nettside, Internett-søkemotor og nye fanesider.
Igfx.exe: Analyse
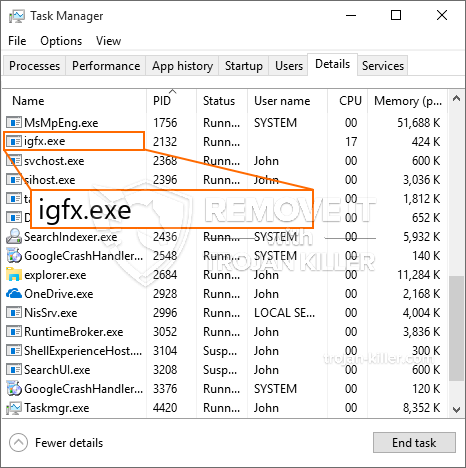
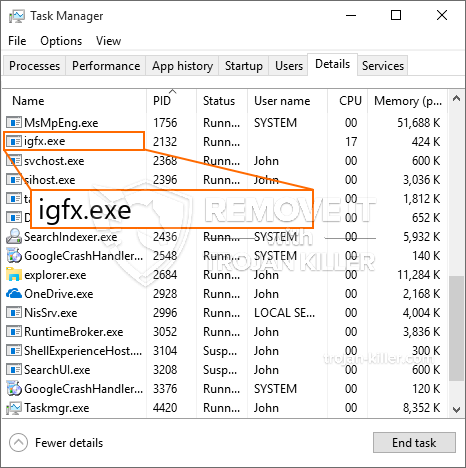
The Igfx.exe malware is a traditional situation of a cryptocurrency miner which relying on its setup can trigger a wide variety of harmful actions. Its primary objective is to perform complex mathematical tasks that will make use of the available system sources: prosessor, GPU, minne samt harddisk rom. The way they work is by linking to an unique server called mining swimming pool from where the required code is downloaded and install. As soon as one of the tasks is downloaded it will certainly be started simultaneously, multiple instances can be run at when. When an offered job is completed another one will certainly be downloaded and install in its area and also the loophole will proceed up until the computer is powered off, infeksjonen fjernes eller et ytterligere tilsvarende hendelse finner sted. Kryptovaluta vil deles ut til de kriminelle kontrollerne (hacking team eller en enslig cyberpunk) rett til deres vesker.
A dangerous attribute of this classification of malware is that samples similar to this one can take all system resources as well as virtually make the sufferer computer unusable until the threat has been totally eliminated. A lot of them include a relentless installment that makes them actually challenging to eliminate. Disse kommandoene vil foreta justeringer for å starte opp valg, arrangement documents and also Windows Registry values that will make the Igfx.exe malware begin immediately when the computer is powered on. Access to recuperation menus and also options might be obstructed which makes several hands-on removal overviews virtually pointless.
Denne bestemt infeksjon vil ordningen en Windows-tjeneste for seg selv, adhering to the performed protection analysis ther complying with activities have been observed:
During the miner operations the associated malware can link to already running Windows solutions as well as third-party installed applications. Ved å gjøre slik at systemadministratorer kanskje ikke legge merke til at ressurs masse stammer fra en annen prosedyre.
| Navn | Igfx.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Igfx.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre innovative kommandoer hvis de er konfigurert slik. They are based on a modular framework permitting the criminal controllers to coordinate all kinds of dangerous habits. En av de populære eksemplene er endring av Windows-registeret – alterations strings connected by the operating system can cause significant performance interruptions as well as the inability to access Windows services. Relying on the range of adjustments it can likewise make the computer totally unusable. On the other hand adjustment of Registry values belonging to any kind of third-party set up applications can sabotage them. Noen applikasjoner kan komme til å bli introdusert helt, mens andre uventet kan slutte å jobbe.
This certain miner in its current variation is focused on extracting the Monero cryptocurrency consisting of a changed variation of XMRig CPU mining engine. If the projects prove successful after that future variations of the Igfx.exe can be released in the future. Som malware bruker programvare programsårbarheter å infisere målet verter, det kan være en del av en usikker samtidig infeksjon med ransomware og også trojanere.
Removal of Igfx.exe is strongly recommended, considering that you risk not only a big electricity bill if it is working on your PC, but the miner may also perform various other unwanted tasks on it as well as even harm your PC completely.
Igfx.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Igfx.exe
SKRITT 5. Igfx.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Igfx.exe
Hvor å forhindre din PC blir infisert med “Igfx.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Igfx.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Igfx.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Igfx.exe”.







