En ny, veldig farlig kryptovaluta miner infeksjonen har faktisk blitt funnet av sikkerhetsforskere. den malware, kalt Disk_defragm.exe kan infisere mål ofrene benytte et utvalg av midler. Essensen bak Disk_defragm.exe gruvearbeideren er å ansette cryptocurrency gruvearbeider aktiviteter på datasystemene til mål for å skaffe Monero symboler på måls bekostning. Resultatet av denne gruvearbeideren er de økte strømregningene, så vel som om du lar det ligge i lengre tid Disk_defragm.exe kan også skade datamaskinens deler.
Disk_defragm.exe: distribusjonsmetoder
De Disk_defragm.exe malware bruker to fremtredende metoder som brukes for å forurense datamaskinsystemmål:
- Nyttelast Levering gjennom Tidligere infeksjoner. Hvis en eldre Disk_defragm.exe malware er distribuert på målsystemene, kan den umiddelbart oppdatere seg selv eller laste ned og installere en nyere variant. Dette er mulig å bruke den integrerte oppdateringskommandoen som får utgivelsen. Dette gjøres ved å knytte til en bestemt forhåndsdefinert hacker-kontrollert server som gir malware-koden. Den nedlastede og installere infeksjonen vil få navnet på en Windows-løsning, samt bli plassert i “%Systemet% temp” plassering. Viktige hjem og også kjørende systemordningsfiler blir transformert for å tillate en jevn og rolig infeksjon.
- Utnytter programvare for sikkerhetsproblem. Den nyeste versjonen av Disk_defragm.exe malware har blitt oppdaget å bli brakt videre av noen ventures, mye forstått for å ha blitt benyttet i ransomware-streikene. Infeksjoner er gjort ved å målrette åpne tjenester ved hjelp av TCP-port. Angrepene er automatiserte av hackere styrt struktur som vender opp om porten er åpen. Hvis denne betingelsen er oppfylt, vil den skanne tjenesten samt hente informasjon angående den, som består av hvilken som helst versjon og også konfigurasjonsinformasjon. Utnytter og populær brukernavn samt passord mikser kan gjøres. Når bruken er satt av mot den sårbare koden, blir gruvearbeideren frigjort i tillegg til bakdøren. Dette vil sikkert presentere en dobbelinfeksjon.
Bortsett fra disse teknikkene kan det også benyttes forskjellige andre tilnærminger. Gruvearbeidere kan spres ved hjelp av phishing-e-post som blir sendt ut i bulk på en SPAM-lignende måte og er også avhengige av sosialtekniske triks for å pusle ofrene til å tro at de faktisk har mottatt en melding fra en ekte tjeneste eller selskap. Infeksjonsdataene kan enten kobles rett inn eller settes inn i kroppens innhold i multimediainnhold eller nettleser for meldinger.
Kriminelle kan på samme måte lage skadelige destinasjonssider som kan utgjøre seg for leverandørens nedlasting og installering av websider, programvare last ned portaler og andre ofte tilgjengelige steder. Når de bruker lignende tilsynelatende domenenavn som legit adresser og også sikkerhetssertifiseringer, kan kundene bli tvunget til å samarbeide med dem. I mange tilfeller rett og slett å åpne dem kan aktivere miner infeksjon.
En annen strategi vil absolutt være å bruke transportører som kan spres ut ved å bruke disse metodene eller via nettverk for deling av dokumenter, BitTorrent er en av de mest populære. Det blir ofte brukt til å spre både legit programvare så vel som dokumenter og piratinnhold. To av de mest populære transportørene er følgende:
Ulike andre metoder som skurkene kan tenke på inkluderer bruk av nettleserkaprere - skrekkelige plugins som er gjort egnet med de mest foretrukne nettlesere.. De blir publisert til de aktuelle depotene med falske kundeavtaler og programmeringskvalifikasjoner. I mange tilfeller beskrivelsene kan bestå av skjermbilder, videoer samt sofistikerte sammendrag som lover utmerkede attribusforbedringer og ytelsesoptimaliseringer. Ikke desto mindre vil vanene til de påvirkede nettleserne ved innstilling endre seg- enkeltpersoner vil oppdage at de vil bli omdirigert til en hacker-kontrollert destinasjonsside og innstillingene deres kan bli endret – standard startside, internett søkemotor og også nye faner side.

Disk_defragm.exe: Analyse
Disk_defragm.exe-malware er et klassisk tilfelle av en cryptocurrency-gruvearbeider, som avhengig av konfigurasjonen kan forårsake en rekke farlige handlinger. Dets viktigste mål er å utføre kompliserte matematiske oppgaver som vil få mest mulig ut av de tilgjengelige systemkildene: prosessor, GPU, minne og harddiskplass. Midlene de opererer er ved å koble til en unik server som heter mining swimming pool hvor den nødvendige koden lastes ned. Så snart en av jobbene er lastet ned, vil den absolutt bli startet samtidig, mange tilfeller kan utføres så snart som. Når en gitt oppgave er ferdig, vil en ekstra en sikkert laste ned den på sin plass, og også løkken vil fortsette helt til datamaskinen er slått av, infeksjonen er blitt kvitt eller en mer lik anledning oppstår. Kryptovaluta vil sikkert bli belønnet til de kriminelle kontrollerne (hacking team eller en enkelt cyberpunk) rett til sine lommebøker.
En skadelig kvalitet på denne gruppen malware er at eksempler som ligner på denne kan ta alle systemkilder og praktisk talt gjøre datamaskinsystemet meningsløst til faren faktisk er blitt eliminert.. Mange av dem inkluderer et nådeløst oppsett som gjør dem faktisk utfordrende å bli kvitt. Disse kommandoene vil sikkert gjøre endringer for alternativer, installasjonsfiler så vel som Windows-registerverdier som sikkert vil føre til at Disk_defragm.exe malware starter automatisk så snart datasystemet er slått på. Tilgang til valg av mat og valg av rekreasjon kan bli blokkert, noe som gjør mange praktiske eliminasjonsoversikter tilnærmet meningsløse.
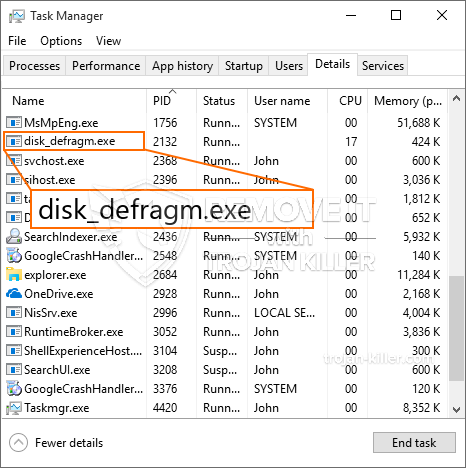
Denne spesifikke infeksjonen vil sikkert arrangere en Windows-løsning for seg selv, i samsvar med den utførte sikkerhets- og sikkerhetsanalysen er følgende aktiviteter blitt observert:
. Under gruvedriftens operasjoner kan den tilknyttede skadelige programvaren koble seg til allerede kjørte Windows-tjenester så vel som tredjepartsinstallasjoner. Ved å gjøre det kan det hende at systemansvarlige ikke observerer at kildebelastningen stammer fra en annen prosess.
| Navn | Disk_defragm.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware for å oppdage og fjerne Disk_defragm.exe |

Denne typen malware-infeksjoner er spesielt pålitelige når de utfører sofistikerte kommandoer hvis de er konfigurert slik. De er basert på et modulært rammeverk som gjør det mulig for kriminelle kontrollører å håndtere alle slags farlige vaner. Blant de prominente eksemplene er justering av Windows-registeret – modifikasjonsstrenger tilknyttet os kan utløse store effektivitetsforstyrrelser og mangelen på evne til å få tilgang til Windows-tjenester. Avhengig av omfanget av endringer kan det også gjøre datamaskinen helt ubrukelig. På den annen side kan justering av registerverdier som kommer fra alle typer tredjepartsmonterte applikasjoner undergrave dem. Noen applikasjoner kan ikke starte helt, mens andre plutselig kan slutte å fungere.
Denne spesifikke gruvearbeideren i sin eksisterende versjon er fokusert på gruvedrift av Monero cryptocurrency som inneholder en endret versjon av XMRig CPU gruvemotor. Hvis prosjektene viser seg effektive, kan fremtidige variasjoner av Disk_defragm.exe frigis i fremtiden. Som malware bruker programvare programsårbarheter forurense målet verter, det kan være bestanddel av en farlig samtidig infeksjon med ransomware og også trojanere.
Fjerning av Disk_defragm.exe anbefales sterkt, gitt at du risikerer ikke bare en stor elektrisk energikostnad hvis den fungerer på din PC, men gruvearbeideren kan også gjøre forskjellige andre uønskede oppgaver på den og også til og med skade PCen din fullstendig.
Disk_defragm.exe fjerningsprosess
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” -knappen for å fjerne Disk_defragm.exe
SKRITT 5. Disk_defragm.exe fjernet!
video guide: Hvordan bruke GridinSoft Anti-Malware for å fjerne Disk_defragm.exe
Hvor å forhindre din PC blir infisert med “Disk_defragm.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Disk_defragm.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Disk_defragm.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Disk_defragm.exe”.







