En ny, veldig skadelig kryptovaluta-gruvevirus har faktisk blitt funnet av beskyttelsesforskere. den malware, kalt Cpuminer-uninst.exe kan forurense mållidende ved å bruke en rekke midler. Hovedpoenget bak Cpuminer-uninst.exe-gruvearbeideren er å bruke kryptovaluta-gruvearbeidere på datasystemene til pasienter for å få Monero-tokens til målkostnad. The outcome of this miner is the raised electricity expenses and also if you leave it for longer amount of times Cpuminer-uninst.exe may even harm your computer systems elements.
Cpuminer-uninst.exe: distribusjonsmetoder
De Cpuminer-uninst.exe skadelig benytter to foretrukne fremgangsmåter som er benyttet for å infisere data mål:
- Nyttelast Levering gjennom Tidligere infeksjoner. If an older Cpuminer-uninst.exe malware is released on the target systems it can instantly update itself or download and install a more recent version. Dette er mulig ved hjelp av den innebygde oppdateringskommandoen som får utgivelsen. This is done by linking to a certain predefined hacker-controlled web server which offers the malware code. The downloaded and install infection will certainly obtain the name of a Windows solution and be positioned in the “%Systemet% temp” plassering. Important homes and running system configuration documents are altered in order to allow a relentless and silent infection.
- Programvare Utnytter Søknad om sikkerhetsproblemene. The newest variation of the Cpuminer-uninst.exe malware have been located to be brought on by the some exploits, populært forstått for de ble anvendt i Ransomware streik. Infeksjonene er gjort ved å målrette åpne løsninger via TCP-port. Overfallene er automatiserte av hackere styrt struktur som søker etter om porten er åpen. If this condition is fulfilled it will scan the solution and retrieve information concerning it, including any kind of version and also arrangement data. Exploits as well as preferred username as well as password combinations might be done. When the make use of is set off against the at risk code the miner will be deployed in addition to the backdoor. Dette vil sikkert gi en dobbel infeksjon.
Apart from these techniques various other methods can be utilized too. Miners can be dispersed by phishing emails that are sent out wholesale in a SPAM-like manner and depend upon social engineering techniques in order to perplex the sufferers into believing that they have actually gotten a message from a legit service or firm. The infection files can be either straight connected or inserted in the body components in multimedia web content or text web links.
The crooks can also produce malicious touchdown web pages that can pose supplier download web pages, programvare nedlasting portaler, så vel som forskjellige andre områder som regelmessig er tilgjengelige. When they use comparable sounding domain to reputable addresses and safety and security certificates the customers might be coerced into engaging with them. Noen ganger bare åpne dem kan utløse miner infeksjon.
One more strategy would be to use haul carriers that can be spread out utilizing those approaches or using data sharing networks, BitTorrent er bare en av en av de mest populære. It is frequently made use of to disperse both reputable software application as well as files and also pirate material. To av en av de mest foretrukne hale leverandører er følgende:
Various other methods that can be taken into consideration by the criminals include making use of internet browser hijackers -harmful plugins which are made suitable with one of the most prominent internet browsers. They are posted to the relevant repositories with fake user evaluations and also developer credentials. Ofte sammendragene kan inkludere skjermbilder, video clips and fancy summaries promising wonderful function enhancements and also performance optimizations. Nonetheless upon installment the habits of the influenced web browsers will certainly alter- users will certainly locate that they will certainly be redirected to a hacker-controlled landing web page and their settings might be changed – standard startside, søkemotor og også splitter ny faneside.

Cpuminer-uninst.exe: Analyse
The Cpuminer-uninst.exe malware is a traditional case of a cryptocurrency miner which relying on its arrangement can create a wide array of harmful actions. Hovedmålet er å utføre komplekse matematiske oppgaver som vil få mest mulig ut av de tilbudte systemkildene: prosessor, GPU, minne og også plass på harddisken. Måten de jobber på er ved å koble til en unik server kalt mining pool hvor den nødvendige koden lastes ned. Så raskt som blant jobbene lastes ned vil den helt sikkert begynne samtidig, mange tilfeller kan være borte så snart. Når en gitt oppgave er fullført, vil en til bli lastet ned i området, og løkken vil sikkert fortsette frem til datasystemet slås av, infeksjonen elimineres eller en annen sammenlignbar anledning oppstår. Kryptovaluta vil sikkert bli kompensert for den kriminelle kontrollerne (hacking team eller en enslig cyberpunk) direkte til sine vesker.
Et skadelig trekk ved denne kategorien skadevare er at prøver som ligner på denne kan ta alle systemkilder samt praktisk talt gjøre måldatasystemet ubrukelig inntil faren faktisk er fullstendig eliminert. De fleste av dem inkluderer en vedvarende del som gjør dem faktisk vanskelig å bli kvitt. Disse kommandoene vil sikkert gjøre justeringer i oppstartsalternativer, setup documents and also Windows Registry values that will certainly make the Cpuminer-uninst.exe malware beginning instantly once the computer is powered on. Tilgjengelighet til valg av rekreasjonsmat så vel som valg kan bli hindret, noe som gjør mange manuelle fjerningsoversikter nesten verdiløse.
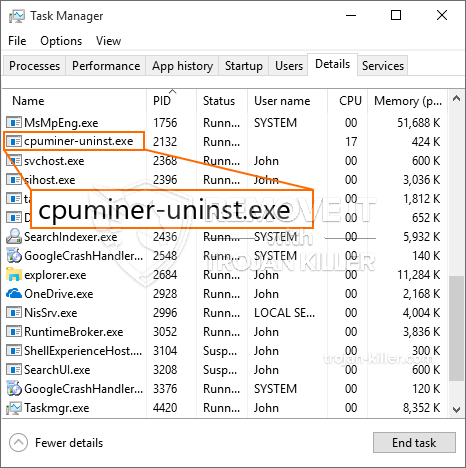
Denne spesifikke infeksjonen vil sette opp en Windows-tjeneste for seg selv, følge den utførte sikkerhetsanalysen og følgende aktiviteter er observert:
. Under gruvedriften kan den tilknyttede skadelige programvaren kobles til allerede kjørende Windows-tjenester og også tredjeparts oppsettprogrammer. Ved å gjøre det kan det hende at systemadministratorene ikke oppdager at kildepartiene stammer fra en annen prosess.
| Navn | Cpuminer-uninst.exe |
|---|---|
| Kategori | Trojan |
| Underkategori | kryptovaluta Miner |
| farer | Høy CPU-bruk, Internett hastighetsreduksjon, PC krasjer og fryser og etc. |
| Hovedhensikt | For å tjene penger for kriminelle |
| Fordeling | torrents, Gratis spill, Cracked Apps, e-post, tvilsomme nettsteder, Utnytter |
| fjerning | Installere GridinSoft Anti-Malware to detect and remove Cpuminer-uninst.exe |

Denne typen malware-infeksjoner er spesielt effektive til å utføre avanserte kommandoer hvis de er konfigurert slik. De er basert på en modulær struktur som gjør det mulig for de kriminelle kontrollørene å koordinere alle typer skadelig atferd. Blant de prominente tilfeller er endring av Windows-registeret – justeringsstrenger knyttet til operativsystemet kan forårsake betydelige effektivitetsforstyrrelser og manglende evne til å få tilgang til Windows-løsninger. Avhengig av omfanget av justeringer kan det også gjøre datamaskinen helt ubrukelig. På den annen side kan manipulering av registerverdier som tilhører alle slags tredjepartsmonterte applikasjoner sabotere dem. Noen applikasjoner kan ikke starte helt, mens andre plutselig kan slutte å jobbe.
Denne spesielle gruvearbeideren i sin eksisterende variant er fokusert på å trekke ut Monero-kryptovalutaen inkludert en modifisert variant av XMRig CPU-gruvemotoren. If the projects show successful after that future variations of the Cpuminer-uninst.exe can be launched in the future. Som malware bruker programvare programsårbarheter forurense målet verter, det kan være en del av en skadelig samtidig infeksjon med ransomware samt trojanere.
Removal of Cpuminer-uninst.exe is strongly recommended, med tanke på at du risikerer ikke bare store elektriske energikostnader hvis den kjører på DATAMASKINEN din, Men gruvearbeideren kan også utføre andre uønskede aktiviteter på den, samt skade PC-en din permanent.
Cpuminer-uninst.exe removal process
SKRITT 1. Først av alt, du må laste ned og installere GridinSoft Anti-Malware.
SKRITT 2. Da bør du velge “Rask skanning” eller “Full skanning”.
SKRITT 3. Kjør for å skanne datamaskinen
SKRITT 4. Etter at skanningen er fullført, du må klikke på “Søke om” button to remove Cpuminer-uninst.exe
SKRITT 5. Cpuminer-uninst.exe Removed!
video guide: How to use GridinSoft Anti-Malware for remove Cpuminer-uninst.exe
Hvor å forhindre din PC blir infisert med “Cpuminer-uninst.exe” i fremtiden.
En kraftig antivirus løsning som kan oppdage og blokkere fileless malware er hva du trenger! Tradisjonelle løsninger oppdager malware basert på virusdefinisjoner, og dermed er de ofte ikke kan oppdage “Cpuminer-uninst.exe”. GridinSoft Anti-Malware gir beskyttelse mot alle typer malware inkludert fileless malware som “Cpuminer-uninst.exe”. GridinSoft Anti-Malware gir cloud-baserte atferd analysator for å blokkere alle ukjente filer, inkludert zero-day malware. Slik teknologi kan oppdage og fjerne “Cpuminer-uninst.exe”.







