
Een team van onderzoekers uit de Verenigde Staten, Australië en Oostenrijk ontwikkelde een nieuwe versie van Rowhammer aanval.
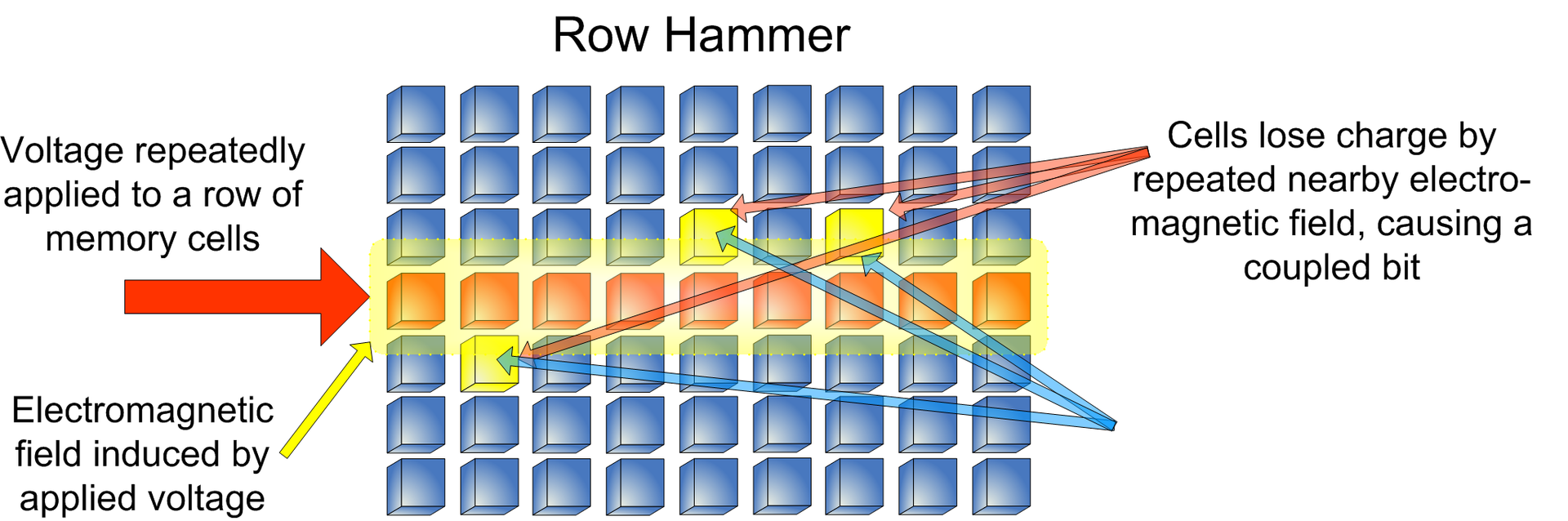
denlike previous versions, a new attack called RAMBleed allows not only modifing data and increase privileges, maar ook stelen van gegevens die zijn opgeslagen op het apparaat.Rowhammer is een exploit klasse voor hardware kwetsbaarheid (CVE-2019-0174) in de moderne geheugenkaarten. Standaard, data in memory cards is stored in cells located on a silicon chip in rows forming a grid.
In 2014, scientists found that multiple readings of data stored in the same row result in an electrical charge that can affect data in adjacent rows. The attack was called Rowhammer, and with its help, scientists could either damage data or use it for malicious purposes.
Sinds 2014, researchers significantly expanded capabilities of the original attack, Echter, it was only now possible to remove data from the memory and steal it.
“It is widely assumed however, that bit flips within the adversary’s own private memory have no security implications, as the attacker can already modify its private memory via regular write operations. We demonstrate that this assumption is incorrect by employing Rowhammer as areadside channel. More specifically, we show how an unprivileged attacker can exploit the data dependence between Rowhammer induced bit flips and the bitsin nearby rows to deduce these bits, including values belonging to other processes and the kernel”, - verslag van de onderzoekers.
In order to make RAMBleed attack possible, scientists managed to force Linux memory allocator (buddy allocator) to enable a large block of consecutive physical addresses that allowed them to orchestrate the attack.
Researchers created a new mechanism, “Frame Feng Shui“, to place victim’s program pages in the right place in physical memory. In aanvulling op, they developed a new method of managing data in memory and repeating their reading (so-called row hammering) to determine which data is in neighboring memory cells.
“Thus, primary contribution of this work is to show that Rowhammer is a threat to not only integrity, but also to confidentiality”, — say scientists.
