Een nieuw, zeer onveilig cryptogeld mijnwerker infectie daadwerkelijk is gespot door de veiligheid van wetenschappers. de malware, riep Wincache.exe kan doelwitpatiënten infecteren met behulp van een selectie van methoden. De essentie achter de Wincache.exe-mijnwerker is om cryptocurrency-mijnwerker-taken op de computers van patiënten te gebruiken om Monero-symbolen te verwerven tegen kostprijs van de slachtoffers. Het resultaat van deze miner is de hoge elektriciteitsrekening en als u deze langere tijd achterlaat, kan Wincache.exe zelfs de componenten van uw computersysteem beschadigen.
Wincache.exe: distributiemethoden
De Wincache.exe malware maakt gebruik van 2 prominente technieken die worden gebruikt om computersysteemdoelen te besmetten:
- Payload Delivery gebruik Prior Infecties. Als een oudere Wincache.exe-malware wordt vrijgegeven op de systemen van de gebruiker, kan deze zichzelf onmiddellijk upgraden of een recentere versie downloaden en installeren. Dit is mogelijk door middel van de ingebouwde upgrade commando dat de lancering krijgt. Dit wordt gedaan door aansluiting op een speciaal vooraf bepaald hacker-gecontroleerde server die de malware code voorziet. Het gedownloade virus krijgt de naam van een Windows-oplossing en wordt in de “%systeem% temp” Gebied. Belangrijke gebouwen en actieve systeemindelingsbestanden worden gewijzigd om een consistente en stille infectie mogelijk te maken.
- Software Vulnerability Exploits. Er is ontdekt dat de nieuwste variant van de Wincache.exe-malware is geactiveerd door een aantal ondernemingen, algemeen duidelijk is voor toepassing in de ransomware strikes. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. Als aan dit probleem wordt voldaan, zal het zeker de oplossing controleren en ook informatie hierover krijgen, bestaande uit elk type variatie en ook arrangementgegevens. Ventures en ook prominente gebruikersnaam en wachtwoordmixen kunnen worden gedaan. Wanneer de exploit wordt veroorzaakt tegen de gevoelige code, zal de miner zeker worden vrijgegeven naast de achterdeur. Dit zal zeker bieden een dubbele infectie.
Naast deze methoden kunnen ook andere strategieën worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die in bulk worden verzonden op een SPAM-achtige manier en ook afhankelijk zijn van trucs voor sociale ontwerpen om de patiënten te verwarren met de overtuiging dat ze een bericht hebben ontvangen van een legitieme oplossing of bedrijf. De infectiegegevens kunnen rechtstreeks worden aangesloten of in de lichaamsonderdelen worden geplaatst in multimediamateriaal of tekstweblinks.
De daders kunnen ook kwaadaardige bestemmingswebpagina's produceren die de download van de leverancier kunnen imiteren en webpagina's kunnen installeren, portals voor het downloaden van softwaretoepassingen en andere regelmatig bezochte gebieden. Wanneer ze vergelijkbare verschijnende domeinnamen gebruiken voor legitieme adressen, evenals veiligheids- en beveiligingscertificaten, kunnen de gebruikers worden gedwongen rechtstreeks met hen te communiceren. Soms zijn ze alleen maar te openen kan verrekenen de mijnwerker infectie.
Een aanvullende techniek zou zeker zijn om gebruik te maken van aanbieders van payload-diensten die via die technieken of via netwerken voor het delen van bestanden kunnen worden verspreid, BitTorrent is slechts een van de meest geprefereerde. Er wordt regelmatig gebruik van gemaakt om zowel legitieme softwaretoepassingen als gegevens en piratenmateriaal te verspreiden. Twee van één van de meest populaire haul service providers zijn de volgende:
Andere benaderingen waarmee de overtreders rekening kunnen houden, zijn onder meer het gebruik van browserkapers - gevaarlijke plug-ins die compatibel zijn gemaakt met de meest populaire internetbrowsers. Ze worden in de juiste databases geplaatst met nepgetuigenissen van klanten en ook kwalificaties voor ontwerpers. Vaak is het zo samenvattingen kunnen screenshots omvatten, videoclips en geavanceerde beschrijvingen die uitstekende functieverbeteringen en prestatie-optimalisaties beloven. Desalniettemin zullen de gewoonten van de getroffen browsers tijdens de installatie zeker veranderen- individuen zullen zeker ontdekken dat ze worden omgeleid naar een door een hacker bestuurde bestemmingspagina en dat ook hun instellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine en ook nieuwe tabbladen webpagina.

Wincache.exe: Analyse
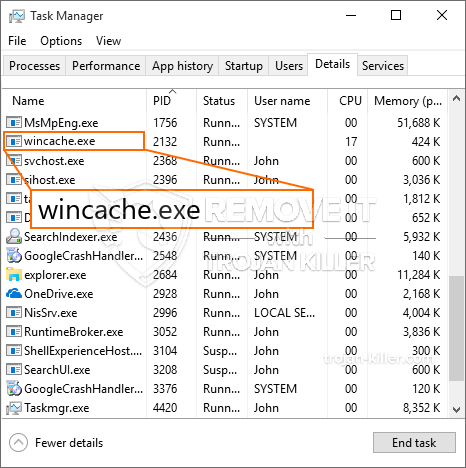
De Wincache.exe-malware is een traditioneel geval van een cryptocurrency-mijnwerker die, afhankelijk van de opstelling, een verscheidenheid aan gevaarlijke acties kan veroorzaken. Het primaire doel is om complexe wiskundige taken uit te voeren die zeker zullen profiteren van de beschikbare systeembronnen: processor, GPU, geheugen en harde schijf ruimte. De methode die ze gebruiken, is door verbinding te maken met een speciale webserver genaamd mijnbouwzwembad van waaruit de vereiste code wordt gedownload en geïnstalleerd. Zodra een van de taken is gedownload, wordt deze meteen gestart, meerdere omstandigheden kan worden uitgevoerd in een keer. Wanneer een opgegeven taak is voltooid, zal er zeker nog een worden gedownload en op zijn locatie worden geïnstalleerd en de lus zal zeker doorgaan totdat het computersysteem wordt uitgeschakeld, de infectie wordt geëlimineerd of er doet zich een andere soortgelijke gebeurtenis voor. Cryptogeld zal beloond worden naar de correctionele controllers (hacken groep of een enkele cyberpunk) direct naar hun begrotingen.
Een onveilige kwaliteit van deze classificatie van malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en het computersysteem van het slachtoffer bijna zinloos kunnen maken totdat het gevaar daadwerkelijk volledig is geëlimineerd. De meeste hebben een consistente opzet waardoor ze echt moeilijk te elimineren zijn. Deze commando's zullen zeker aanpassingen ook opties maken, rangschikkingsbestanden en ook Windows-registerwaarden die ervoor zorgen dat de Wincache.exe-malware automatisch automatisch start zodra de computer wordt ingeschakeld. Toegang tot selecties en alternatieven voor herstelvoedsel kan worden geblokkeerd, waardoor veel praktische verwijderingsgidsen vrijwel niet effectief zijn.
Deze bijzondere infectie zal het opzetten van een Windows-oplossing voor zichzelf, vast te houden aan het gevoerde veiligheid en beveiliging evaluatie ther volgende acties daadwerkelijk waargenomen:
. Tijdens de miner-procedures kan de gekoppelde malware verbinding maken met reeds actieve Windows-services en geïnstalleerde applicaties van derden. Hierdoor ontdekken de systeembeheerders mogelijk niet dat de resourcetonnen afkomstig zijn van een afzonderlijk proces.
| Naam | Wincache.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware om Wincache.exe te detecteren en te verwijderen |

Dit soort malware-infecties zijn bijzonder effectief bij het uitvoeren van geavanceerde opdrachten als ze zo zijn ingesteld. Ze zijn gebaseerd op een modulair kader waardoor de criminele controleurs allerlei soorten schadelijk gedrag kunnen orkestreren. Een van de geprefereerde voorbeelden is de wijziging van het Windows-register – Aanpassingsstrings die verband houden met het besturingssysteem kunnen grote verstoringen in de efficiëntie veroorzaken en ook het gebrek aan toegang tot Windows-services. Afhankelijk van de omvang van de aanpassingen kan het de computer eveneens volledig onbruikbaar maken. Aan de andere kant kan aanpassing van registerwaarden die afkomstig zijn van door derden gemonteerde applicaties deze ondermijnen. Sommige toepassingen kan mislukken volledig vrij te geven, terwijl anderen onverwacht kan stoppen met werken.
Deze bepaalde mijnwerker in zijn huidige versie is gericht op het extraheren van de Monero-cryptocurrency die een gewijzigde variant van de XMRig CPU-mijnengine bevat. Als de projecten daarna succesvol blijken te zijn, kunnen toekomstige versies van Wincache.exe in de toekomst worden gelanceerd. Als de malware gebruik maakt van de zwakke plekken in software om de beoogde gastheer te infecteren, kan onderdeel van een onveilige co-infectie met ransomware en als Trojaanse paarden.
Het elimineren van Wincache.exe wordt sterk aanbevolen, aangezien u niet alleen het risico loopt van grote stroomkosten als deze op uw COMPUTER werkt, maar de mijnwerker kan er ook verschillende andere ongewenste activiteiten op uitvoeren en zelfs uw pc permanent beschadigen.
Wincache.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Wincache.exe te verwijderen
STAP 5. Wincache.exe verwijderd!
video Guide: Hoe GridinSoft Anti-Malware te gebruiken voor het verwijderen van Wincache.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Wincache.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Wincache.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Wincache.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Wincache.exe”.







