Een gloednieuw, echt gevaarlijke cryptocurrency-mijnwerkersinfectie is daadwerkelijk opgemerkt door beveiligingswetenschappers. de malware, riep Time.exe kan doelwitpatiënten infecteren met behulp van verschillende middelen. Het belangrijkste idee achter de Time.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten te gebruiken op de computersystemen van patiënten om Monero-symbolen te krijgen op kosten van de slachtoffers. The outcome of this miner is the elevated power bills and if you leave it for longer time periods Time.exe may even damage your computers components.
Time.exe: distributiemethoden
De Time.exe malware maakt gebruik van twee populaire methoden die worden gebruikt om het computersysteem targets besmetten:
- Payload bezorging via Prior Infecties. If an older Time.exe malware is released on the target systems it can instantly update itself or download a newer variation. Dit is mogelijk via het geïntegreerde update-commando dat de release verwerft. Dit wordt gedaan door verbinding te maken met een specifieke, vooraf gedefinieerde, door een hacker bestuurde webserver die de malwarecode aanbiedt. De gedownloade en installeer infectie zal zeker de naam van een Windows-service te verwerven en ook in de worden gezet “%systeem% temp” plaats. Essentiële woningen en ook actieve systeemconfiguratiegegevens worden getransformeerd om een aanhoudende en ook stille infectie mogelijk te maken.
- Software Application Vulnerability Exploits. The most current version of the Time.exe malware have actually been discovered to be brought on by the some exploits, in de volksmond bekend als gebruikt bij ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De aanvallen worden geautomatiseerd door een hacker bestuurde structuur die zoekt uit of de poort open. Als aan dit probleem is voldaan, wordt de oplossing gescand en wordt er informatie over opgehaald, inclusief alle soorten versies en instellingsgegevens. Exploits en prominente gebruikersnaam en ook wachtwoordmixen kunnen worden gedaan. Wanneer de manipulatie wordt geactiveerd tegen de gevoelige code, wordt de mijnwerker naast de achterdeur ingezet. Dit zal zeker bieden een dubbele infectie.
Naast deze technieken kunnen ook verschillende andere methoden worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die op een SPAM-achtige manier in bulk worden verzonden en die afhankelijk zijn van social design-trucs om de slachtoffers te doen geloven dat ze een bericht hebben ontvangen van een legitieme dienst of bedrijf. De infectiebestanden kunnen rechtstreeks worden aangesloten of in de lichaamscomponenten worden geplaatst in multimedia-inhoud of tekstweblinks.
De overtreders kunnen bovendien kwaadaardige bestemmingswebpagina's maken die download- en installatiepagina's van leveranciers kunnen opleveren, softwaredownloadsites en diverse andere veel gebruikte gebieden. Wanneer ze vergelijkbare schijnbare domeinnamen gebruiken voor echte adressen, evenals beveiligingscertificeringen, kunnen de gebruikers ertoe worden gedwongen contact met hen op te nemen. Soms kan alleen het openen ervan de mijnwerkersinfectie veroorzaken.
Een andere methode zou zeker zijn om gebruik te maken van haul service providers die verspreid kunnen worden door gebruik te maken van de bovengenoemde technieken of door middel van file sharing netwerken, BitTorrent behoort tot een van de meest populaire. Het wordt vaak gebruikt om zowel gerenommeerde software en documenten als pirateninhoud te verspreiden. Twee van de meest prominente payload providers zijn de volgende:
Andere technieken die door de kwaaddoeners kunnen worden overwogen, zijn het gebruik van browserkapers - gevaarlijke plug-ins die compatibel zijn gemaakt met de meest populaire webbrowsers. Ze worden geplaatst op de relevante repositories met nep recensies van klanten evenals designer geloofsbrieven. In veel gevallen is de samenvattingen zou kunnen bestaan uit screenshots, video's en mooie samenvattingen die geweldige functieverbeteringen en prestatie-optimalisaties aanmoedigen. Maar na installatie zullen de gewoonten van de getroffen webbrowsers zeker veranderen- klanten zullen zeker merken dat ze zeker zullen worden omgeleid naar een door een hacker bestuurde bestemmingspagina en ook hun instellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine evenals gloednieuwe tabs pagina.

Time.exe: Analyse
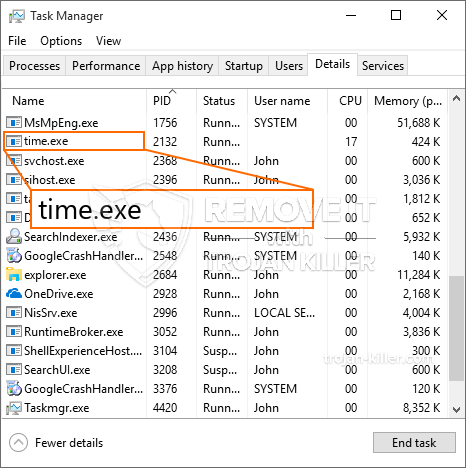
The Time.exe malware is a traditional situation of a cryptocurrency miner which depending on its configuration can trigger a variety of harmful actions. Its major objective is to perform complex mathematical jobs that will take advantage of the available system resources: processor, GPU, geheugen en harde schijf ruimte. The means they function is by attaching to a special server called mining swimming pool where the called for code is downloaded. Zodra een van de taken is gedownload, wordt deze tegelijkertijd gestart, verschillende gevallen kunnen worden uitgevoerd tegelijkertijd. When a given job is completed another one will certainly be downloaded and install in its place and also the loophole will continue up until the computer is powered off, de infectie wordt weggedaan of één meer vergelijkbare gelegenheid gebeurt. Cryptogeld zal zeker worden toegekend aan de criminele controllers (hacken groep of een eenzame hacker) direct naar hun portemonnee.
A hazardous feature of this classification of malware is that examples like this one can take all system sources and also almost make the target computer system pointless up until the threat has actually been completely eliminated. Most of them include a consistent installment which makes them truly tough to eliminate. Deze commando's zal zeker veranderingen ook keuzes, configuration documents as well as Windows Registry values that will certainly make the Time.exe malware beginning instantly as soon as the computer system is powered on. Accessibility to healing food selections as well as choices may be blocked which provides many manual removal guides practically ineffective.
Deze bijzondere infectie zal het opzetten van een Windows-oplossing voor zichzelf, adhering to the performed security evaluation ther following actions have been observed:
. During the miner procedures the connected malware can connect to currently running Windows services and third-party set up applications. By doing so the system administrators might not see that the resource load originates from a different procedure.
| Naam | Time.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Time.exe |

Dit soort malware-infecties zijn bijzonder effectief bij het uitvoeren van geavanceerde opdrachten als ze zo zijn geconfigureerd. Ze zijn gebaseerd op een modulaire structuur die de criminele controleurs in staat stelt om allerlei gevaarlijke acties te orkestreren. Onder de geprefereerde voorbeelden is de wijziging van het Windows-register – wijzigingsreeksen die verband houden met het besturingssysteem kunnen aanzienlijke efficiëntieonderbrekingen veroorzaken en het onvermogen om toegang te krijgen tot Windows-oplossingen. Afhankelijk van de omvang van de wijzigingen kan het de computer ook volledig onbruikbaar maken. Aan de andere kant kan manipulatie van registerwaarden die behoren tot elke vorm van geïnstalleerde applicaties van derden, deze saboteren. Sommige toepassingen worden mogelijk helemaal niet vrijgegeven, terwijl andere onverwacht kunnen stoppen met werken.
Deze specifieke mijnwerker in zijn huidige versie is gericht op het minen van de Monero-cryptocurrency met een aangepaste versie van de XMRig CPU-mijnengine. If the campaigns verify effective then future variations of the Time.exe can be launched in the future. Als de malware maakt gebruik van software kwetsbaarheden te misbruiken doelhosts besmetten, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en Trojaanse paarden.
Elimination of Time.exe is strongly recommended, aangezien u niet alleen het risico loopt van hoge stroomkosten als deze aan uw COMPUTER werkt, maar de mijnwerker kan er ook verschillende andere ongewenste taken op uitvoeren en ook uw pc permanent beschadigen.
Time.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Time.exe
STAP 5. Time.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Time.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Time.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Time.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Time.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Time.exe”.







