Een gloednieuw, extreem gevaarlijk cryptogeld mijnwerker infectie daadwerkelijk is gespot door veiligheid en beveiliging onderzoekers. de malware, riep Soundmodule.exe infecteren doel lijders maken van een selectie van middelen. Het belangrijkste idee achter de Soundmodule.exe mijnwerker is om cryptogeld mijnwerker activiteiten te gebruiken op de computersystemen van het slachtoffer in om Monero symbolen op doelen ten koste te verkrijgen. Het eindresultaat van deze mijnwerker wordt de verhoogde elektrische energie kosten alsmede indien je laat het voor langere perioden Soundmodule.exe kan zelfs uw computer systemen elementen schaden.
Soundmodule.exe: distributiemethoden
De Soundmodule.exe malware gebruik twee belangrijke benaderingen waarbij gebruik wordt gemaakt aan te infecteren computer doelen:
- Payload bezorging via Prior Infecties. Als een oudere Soundmodule.exe malware wordt ingezet op het doel systemen kunnen deze automatisch upgraden of download een nieuwere variant. Dit is mogelijk door middel van de geïntegreerde upgrade commando dat de release verkrijgt. Dit wordt gedaan door aansluiting op een speciaal vooraf bepaald hacker-gecontroleerde webserver die malware code voorziet. De gedownloade en installeer infectie zal zeker de naam van een Windows-oplossing te verkrijgen, alsmede in de worden geplaatst “%systeem% temp” Gebied. Cruciaal woningen en ook draaiend systeem configuratiebestanden worden gewijzigd met het oog op een consistente en ook stil infectie toestaan.
- Software Application Vulnerability Exploits. De meest recente variant van de Soundmodule.exe malware zijn ontdekt te worden veroorzaakt door het aantal exploits, algemeen bekend voor toepassing in de ransomware aanvallen. De infecties worden gedaan door zich te richten geopend diensten via de TCP-poort. De aanvallen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. Als dit probleem wordt voldaan zal het zeker controleert de oplossing en het verkrijgen van informatie over, bestaande uit elke vorm van variatie en ook installatie-informatie. Ventures en prominente gebruikersnaam en wachtwoord mixen zou kunnen worden gedaan. Wanneer het manipuleren is uitgeschakeld versus de kwetsbare code mijnwerkers zeker ingezet met de achterdeur. Dit zal zeker over een duale infectie.
Naast deze werkwijzen kunnen andere werkwijzen gebruik worden gemaakt. Mijnwerkers kunnen worden gedistribueerd door phishing e-mails die uit de groothandel in een worden verzonden SPAM-achtige manier evenals afhangen van social design trucs om de slachtoffers te verwarren recht te denken dat ze daadwerkelijk hebben gekregen een bericht van een legitieme dienst of bedrijf. De infectie documenten kunnen ofwel direct worden bevestigd of in het lichaam inhoud van multimedia web content of boodschap koppelingen.
De criminelen kunt ook destructieve landing webpagina's die leverancier download kan imiteren en installeren van webpagina's, softwaretoepassing download websites en diverse andere regelmatig benaderd gebieden. Wanneer zij gebruik maken van vergelijkbare schijnbare domein legitieme adressen en ook veiligheidscertificaten de individuen kunnen worden overgehaald recht in met hen te communiceren. Soms alleen het openen van hen kan de mijnwerker infectie activeren.
Een extra benadering zou zijn om haul providers gebruiken die spread met behulp van de hierboven genoemde technieken of via het delen van gegevens netwerken kunnen worden, BitTorrent is een van de meest prominente. Het wordt vaak gebruik gemaakt van zowel legitieme software en ook documenten en piraten inhoud verspreiden. 2 één van de meest geprefereerde lading providers zijn de volgende:
Andere methoden die over gedacht kan worden door de daders bestaan uit het gebruik browser hijackers -gevaarlijke plugins die verenigbaar zijn met de meest geprefereerde internet browsers worden gemaakt. Ze zijn gepubliceerd om de relevante repositories met nep individuele getuigenissen en programmeur kwalificaties. Vaak de beschrijvingen kunnen screenshots omvatten, video's en fancy samenvattingen stimuleren van uitstekende attribuut verbeteringen evenals efficiency optimalisaties. Maar bij de tranche van het gedrag van de betrokken browsers zal transformeren- individuen zal zeker vinden dat ze zeker zullen worden doorgestuurd naar een-hacker gecontroleerde touchdown webpagina en hun instellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine en gloednieuwe tabs webpagina.

Soundmodule.exe: Analyse
De Soundmodule.exe malware is een traditionele situatie van een cryptogeld mijnwerker die, afhankelijk van de opstelling van een breed scala van onveilige handelingen kunnen creëren. Zijn primaire doel is om complexe wiskundige banen die zullen profiteren van de beschikbare systeembronnen te voeren: processor, GPU, geheugen en ook de harde schijf ruimte. De methode die ze werken is door te linken naar een speciale server genaamd mijnbouw zwembad waar de opgeroepen voor code wordt gedownload. Zo snel als een van de taken is gedownload zal worden gelijktijdig gestart, meerdere omstandigheden kunnen worden uitgevoerd op wanneer. Wanneer een aangeboden taak is voltooid zal een ander worden gedownload in de locatie, evenals de lus zal doorgaan tot het computersysteem is uitgeschakeld, de infectie wordt weggedaan of een andere vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken groep of een enkele cyberpunk) direct naar hun begrotingen.
Een schadelijke kenmerk van deze groep van malware is dat de voorbeelden die op deze lijkt een overzicht van alle systeembronnen te nemen en ook praktisch de doelcomputer onbruikbaar maken totdat het risico daadwerkelijk volledig is geëlimineerd. De meesten van hen zijn onder andere een hardnekkige installatie die maakt ze echt een uitdaging om zich te ontdoen van. Deze commando's zullen zeker aanpassingen aan laars alternatieven, setup data evenals Windows-register waarden die zeker zal maken van de Soundmodule.exe malware begint automatisch zodra de computer wordt ingeschakeld. De toegankelijkheid van het helen van de menu's, evenals alternatieven zou kunnen worden belemmerd die veel hands-on eliminatie overzichten vrijwel zinloos maakt.
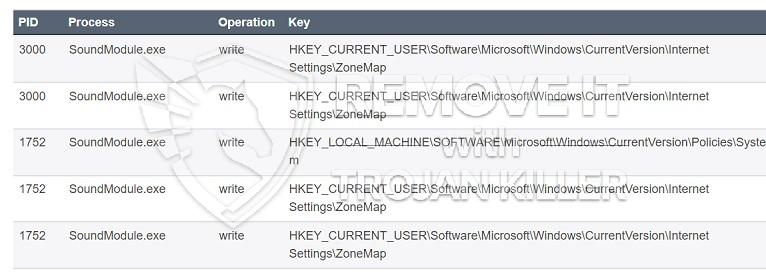
Dit bepaalde infectie zal het inrichten van een Windows-service voor zichzelf, vast te houden aan de uitgevoerde evaluatie bescherming ther voldoen aan acties zijn waargenomen:
. Tijdens de mijnwerker procedures kunnen de aangesloten malware hechten aan al met Windows services en third-party geïnstalleerde toepassingen. Door dit te doen de systeembeheerders niet zou kunnen opmerken dat de bron veel afkomstig is van een andere procedure.
| Naam | Soundmodule.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware op te sporen en te verwijderen Soundmodule.exe |

Dit soort malware-infecties zijn specifiek betrouwbaar bij het vervullen van geavanceerde commando's als zo opgezet. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers om alle soorten van schadelijke gedrag te beheren. Een van de geprefereerde voorbeelden is de wijziging van het Windows-register – aanpassingen strings gerelateerde door het besturingssysteem kan leiden tot grote prestaties verstoringen alsmede het gebrek aan toegang tot Windows-services. Afhankelijk van het bereik van de aanpassingen kan het ook de computer compleet zinloos maken. Anderzijds controle registerwaarden uit derden gemonteerde toepassingen te saboteren. Sommige toepassingen te kort zou schieten om volledig vrij te geven, terwijl anderen onverwacht werken kan stoppen.
Dit bepaalde mijnwerker in zijn huidige versie is gericht op de mijnbouw de Monero cryptogeld bestaande uit een gemodificeerde variant van XMRig CPU mijnbouw motor. Als de campagnes tonen succesvolle vervolgens toekomstige varianten van het Soundmodule.exe kan worden gelanceerd in de toekomst. Als de malware maakt gebruik van software susceptabilities te infecteren doelhosts, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en Trojaanse paarden.
Eliminatie van Soundmodule.exe wordt sterk aanbevolen, omdat je de kans niet alleen een groot elektriciteitsrekening nemen als het werkt op uw computer, maar de mijnwerker kan bovendien het verrichten van andere ongewenste activiteiten op het zo goed als zelfs schade toebrengen aan uw computer permanent.
Soundmodule.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Soundmodule.exe verwijderen
STAP 5. Soundmodule.exe verwijderd!
video Guide: Hoe wordt GridinSoft Anti-Malware gebruiken voor het verwijderen Soundmodule.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Soundmodule.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Soundmodule.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Soundmodule.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Soundmodule.exe”.







