Een gloednieuw, echt schadelijke cryptocurrency-mijnwerkersinfectie is opgemerkt door veiligheidswetenschappers. de malware, riep Oledlg.exe kan doelwitslachtoffers besmetten met behulp van een selectie van methoden. Het belangrijkste punt achter de Oledlg.exe-mijnwerker is het gebruik van cryptocurrency-mijnwerker-taken op de computersystemen van slachtoffers om Monero-symbolen te verkrijgen tegen de kosten van de patiënt. The result of this miner is the raised power costs as well as if you leave it for longer periods of time Oledlg.exe may also harm your computers elements.
Oledlg.exe: distributiemethoden
De Oledlg.exe malware maakt gebruik van twee prominente technieken die worden gebruikt om computersysteemdoelen te besmetten:
- Payload Levering door middel van Prior Infecties. If an older Oledlg.exe malware is deployed on the target systems it can instantly update itself or download and install a more recent version. Dit is mogelijk via de geïntegreerde-update commando dat de lancering verkrijgt. Dit wordt gedaan door verbinding te maken met een bepaalde vooraf gedefinieerde, door hackers gecontroleerde server die de malwarecode levert. Het gedownloade virus krijgt zeker de naam van een Windows-oplossing en wordt in het “%systeem% temp” Gebied. Belangrijke huizen en ook configuratiedocumenten voor besturingssystemen worden gewijzigd om een meedogenloze en stille infectie mogelijk te maken.
- Software Application Vulnerability Exploits. The most current version of the Oledlg.exe malware have actually been found to be triggered by the some ventures, beroemd omdat het werd gebruikt bij de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die zoekt naar als de poort open. Als aan dit probleem wordt voldaan, zal het de oplossing controleren en er informatie over verkrijgen, bestaande uit elk type versie en instellingsgegevens. Exploits en prominente gebruikersnaam en ook met een wachtwoord combinaties kan worden gedaan. Wanneer de manipulatie wordt geactiveerd ten opzichte van de at risk-code, zal de miner zeker samen met de achterdeur worden vrijgegeven. Dit zal zeker presenteren een duale infectie.
Naast deze methodes kunnen er ook verschillende andere methodes worden gebruikt. Mijnwerkers kunnen worden verspreid via phishing-e-mails die op een SPAM-achtige manier in het groot worden verzonden en zijn ook afhankelijk van sociale ontwerpmethoden om de doelwitten te verwarren door te geloven dat ze een bericht hebben ontvangen van een gerenommeerde service of firma.. De infectiebestanden kunnen rechtstreeks worden aangebracht of ingevoegd in de inhoud van het lichaam in multimediamateriaal of berichtlinks.
De criminelen kunnen ook kwaadaardige touchdown-webpagina's maken die zich kunnen voordoen als download- en installatiepagina's van een leverancier, portals voor het downloaden van software en andere veelgebruikte locaties. Wanneer ze vergelijkbare domeinnamen gebruiken voor legitieme adressen en beveiligingscertificaten gebruiken, kunnen de individuen worden gedwongen om met hen te communiceren. In sommige gevallen alleen het openen van hen kan verrekenen de mijnwerker infectie.
Een andere methode zou zeker zijn om ladingsdragers te gebruiken die kunnen worden verspreid met behulp van de bovengenoemde benaderingen of via netwerken voor het delen van documenten, BitTorrent is een van de meest populaire. Het wordt regelmatig gebruikt om zowel legitieme softwaretoepassingen als bestanden en illegale webinhoud te verspreiden. 2 van de meest geprefereerde payload providers zijn de volgende:
Andere technieken waar de slechteriken aan kunnen denken, zijn het gebruik van browserkapers - onveilige plug-ins die compatibel zijn gemaakt met een van de meest prominente webbrowsers. Ze worden ingediend bij de relevante databases met valse gebruikersevaluaties en ook met ontwerpkwalificaties. In de meeste gevallen zijn de samenvattingen kunnen zijn screenshots, videoclips en uitgebreide samenvattingen die geweldige attribuutverbeteringen en ook efficiëntie-optimalisaties aanmoedigen. Niettemin zullen de gewoonten van de beïnvloede browsers op termijn veranderen- klanten zullen ontdekken dat ze zeker zullen worden omgeleid naar een hacker-gecontroleerde touchdown-pagina en dat hun instellingen kunnen worden gewijzigd – de standaard webpagina, online zoekmachine en ook gloednieuwe tabs pagina.

Oledlg.exe: Analyse
The Oledlg.exe malware is a timeless situation of a cryptocurrency miner which depending on its setup can trigger a wide array of dangerous activities. Het primaire doel is om ingewikkelde wiskundige taken uit te voeren die zullen profiteren van de beschikbare systeembronnen: processor, GPU, geheugen en schijfruimte. De manier waarop ze werken is door te linken naar een speciale server genaamd mining pool van waaruit de vereiste code wordt gedownload en geïnstalleerd. Zodra één van de banen wordt gedownload zal het zeker worden gestart in een keer, meerdere instanties kunnen worden uitgevoerd zodra:. Wanneer een aangeboden taak is voltooid, wordt er nog een gedownload en in zijn gebied geïnstalleerd, evenals de maas in de wet totdat het computersysteem wordt uitgeschakeld, de infectie wordt verwijderd of er vindt nog een soortgelijke gebeurtenis plaats. Cryptogeld zal beloond worden naar de correctionele controllers (hacken groep of een enkele cyberpunk) rechtstreeks naar hun portemonnee.
Een gevaarlijk kenmerk van deze categorie malware is dat voorbeelden zoals deze alle systeembronnen kunnen nemen en het computersysteem van de patiënt vrijwel zinloos maken totdat het risico daadwerkelijk volledig is geëlimineerd. De meeste hebben een consistente opstelling waardoor ze echt moeilijk te verwijderen zijn. Deze commando's zullen zeker aanpassingen aan laarsopties maken, setup files and also Windows Registry values that will certainly make the Oledlg.exe malware begin automatically as soon as the computer system is powered on. Toegankelijkheid tot herstelmenu's en alternatieven kan worden belemmerd, waardoor veel praktische eliminatiehandleidingen bijna nutteloos worden.
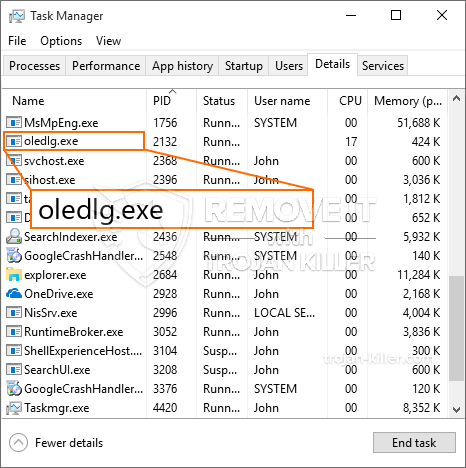
Deze specifieke infectie zal een Windows-oplossing voor zichzelf de configuratie, voldoen aan de uitgevoerde veiligheidsevaluatie zijn de volgende acties in acht genomen:
. Tijdens de miner-procedures kan de bijbehorende malware linken naar momenteel draaiende Windows-services en geïnstalleerde applicaties van derden. Door dit te doen, zien de systeembeheerders mogelijk niet dat de resourcepartijen uit een afzonderlijk proces komen.
| Naam | Oledlg.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Oledlg.exe |

Dit soort malware-infecties zijn in het bijzonder effectief bij het uitvoeren van geavanceerde commando's als zo opgezet. They are based on a modular structure permitting the criminal controllers to coordinate all sort of harmful actions. Een van de belangrijkste voorbeelden is de wijziging van het Windows-register – alterations strings related by the os can cause significant performance disturbances and also the inability to gain access to Windows solutions. Depending on the scope of modifications it can also make the computer system entirely unusable. On the other hand control of Registry worths coming from any type of third-party set up applications can undermine them. Sommige applicaties werken mogelijk niet meer en worden helemaal niet meer vrijgegeven, terwijl andere ineens kunnen stoppen met werken.
This particular miner in its current variation is focused on mining the Monero cryptocurrency containing a modified variation of XMRig CPU mining engine. If the campaigns verify effective after that future variations of the Oledlg.exe can be launched in the future. Als de malware maakt gebruik van softwareprogramma susceptabilities tot doel gastheren besmetten, het kan een deel van een gevaarlijke co-infectie met ransomware zijn evenals Trojans.
Removal of Oledlg.exe is strongly recommended, given that you take the chance of not just a large power expense if it is working on your PC, however the miner might likewise do various other unwanted activities on it and even damage your COMPUTER completely.
Oledlg.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Oledlg.exe
STAP 5. Oledlg.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Oledlg.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Oledlg.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Oledlg.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Oledlg.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Oledlg.exe”.







