Een nieuw, het zeer gevaarlijke cryptocurrency-mijnervirus is eigenlijk gevonden door beveiligingswetenschappers. de malware, riep Miner.exe kan doelwit slachtoffers besmetten door gebruik te maken van een reeks methoden. De essentie achter de Miner.exe-mijnwerker is om cryptocurrency-mijnertaken te gebruiken op de computersystemen van doelen om Monero-symbolen te verwerven tegen de kosten van de slachtoffers. Het eindresultaat van deze mijnwerker zijn de verhoogde elektrische energiekosten en als u het voor langere tijd laat staan, kan Miner.exe zelfs uw computersysteemelementen beschadigen.
Miner.exe: distributiemethoden
De Miner.exe malware maakt gebruik van 2 voorkeurstechnieken die worden gebruikt voor het computersysteem doelen verontreinigen:
- Payload Levering door middel van Prior Infecties. Als een oudere Miner.exe-malware wordt vrijgegeven op de doelsystemen, kan deze zichzelf automatisch upgraden of een recentere versie downloaden. Dit is mogelijk door middel van het geïntegreerde upgradecommando dat de lancering verkrijgt. Dit gebeurt door verbinding met een bepaalde voorgedefinieerde-hacker gecontroleerde webserver die malware code voorziet. Het gedownloade virus krijgt zeker de naam van een Windows-service en wordt ook in het “%systeem% temp” plaats. Cruciale huizen en configuratiedocumenten van besturingssystemen worden gewijzigd om een consistente en ook stille infectie mogelijk te maken.
- Software Vulnerability Exploits. Er is ontdekt dat de meest recente versie van de Miner.exe-malware wordt veroorzaakt door enkele ondernemingen, algemeen begrepen als zijnde gebruikt bij de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen met behulp van de TCP-poort. De aanvallen zijn geautomatiseerd door een hacker gecontroleerd kader die opkijkt als de poort open. Als dit probleem is opgelost, wordt de oplossing gecontroleerd en worden er details over opgehaald, bestaande uit elk type variatie- en instellingsgegevens. Er kunnen zowel uitbuitingen als de voorkeur genietende combinatie van gebruikersnaam en wachtwoord worden gedaan. Wanneer de exploit wordt geactiveerd tegen de gevoelige code, wordt de mijnwerker samen met de achterdeur vrijgegeven. Dit zal zeker presenteren een dubbele infectie.
Afgezien van deze technieken kunnen er ook verschillende andere methoden worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die op een SPAM-achtige manier in het groot worden verzonden en vertrouwen op sociale ontwerptechnieken om de slachtoffers te laten geloven dat ze een bericht hebben ontvangen van een echte dienst of bedrijf. De infectiegegevens kunnen rechtstreeks worden toegevoegd of in de lichaamscomponenten worden ingevoegd in multimediamateriaal of tekstweblinks.
De boeven kunnen bovendien kwaadaardige bestemmingswebpagina's ontwikkelen die download- en installatiepagina's van leveranciers kunnen opleveren, downloadsites voor softwareprogramma's en ook andere vaak bezochte plaatsen. Wanneer ze een soortgelijk klinkend domein gebruiken als echte adressen, evenals beschermingscertificeringen, kunnen de klanten worden gedwongen om met hen in contact te komen. In sommige gevallen alleen het openen van hen kan de mijnwerker een infectie veroorzaken.
Een andere benadering zou zijn het gebruik van transporteurs die kunnen worden verspreid door gebruik te maken van de bovengenoemde methoden of via netwerken voor het delen van documenten, BitTorrent is een van de meest geprefereerde. Het wordt vaak gebruikt om zowel authentieke software als bestanden en illegaal materiaal te verspreiden. Twee van de meest populaire haul providers zijn de volgende:
Andere benaderingen die door de criminelen in overweging kunnen worden genomen, zijn onder meer het gebruik van internetbrowser-hijackers - gevaarlijke plug-ins die geschikt zijn gemaakt voor de meest geprefereerde internetbrowsers.. Ze worden met neprecensies van klanten en ook inloggegevens van de programmeur naar de juiste databases gestuurd. Vaak is het zo samenvattingen kunnen screenshots omvatten, videoclips en geavanceerde samenvattingen die grote functieverbeteringen en prestatie-optimalisaties aanmoedigen. Desalniettemin zullen de gewoonten van de getroffen browsers na installatie veranderen- gebruikers zullen merken dat ze zeker zullen worden omgeleid naar een hacker-gecontroleerde touchdown-pagina en dat hun instellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine en ook gloednieuwe tabs webpagina.

Miner.exe: Analyse
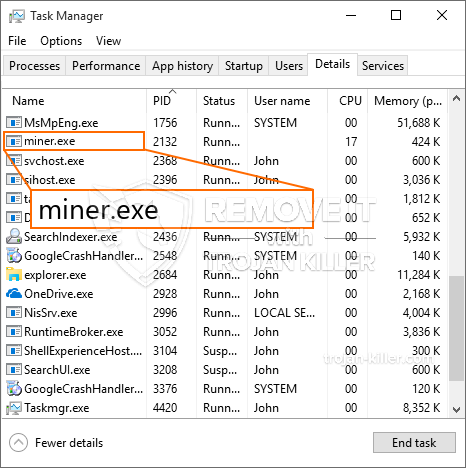
De Miner.exe-malware is een klassiek geval van een cryptocurrency-mijnwerker die, afhankelijk van de opstelling, een breed scala aan gevaarlijke activiteiten kan veroorzaken. Het belangrijkste doel is om ingewikkelde wiskundige taken uit te voeren die zeker zullen profiteren van de aangeboden systeembronnen: processor, GPU, geheugen alsmede ruimte op de harde schijf. De methode die ze gebruiken, is door verbinding te maken met een speciale server, mijnbouwzwembad genaamd, van waaruit de vereiste code wordt gedownload. Zodra een van de banen is gedownload, wordt tegelijkertijd gestart, meerdere exemplaren kan zo snel worden uitgevoerd bij. Wanneer een bepaalde taak is voltooid, zal er zeker een extra worden gedownload in zijn gebied en de lus zal doorgaan totdat de computer wordt uitgeschakeld, de infectie wordt verwijderd of er vindt een bijkomende soortgelijke gebeurtenis plaats. Cryptogeld zal worden toegekend aan de criminele controllers (hacken team of een enkele hacker) direct naar hun begrotingen.
Een gevaarlijk kenmerk van deze classificatie van malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en ook het doelcomputersysteem virtueel onbruikbaar kunnen maken totdat het gevaar daadwerkelijk volledig is verwijderd.. De meeste hebben een permanente installatie waardoor ze erg moeilijk te verwijderen zijn. Deze opdrachten zullen aanpassingen ook alternatieven, ordeningsdocumenten en Windows-registerwaarden die ervoor zorgen dat de Miner.exe-malware onmiddellijk begint wanneer de computer wordt ingeschakeld. De toegang tot selecties en opties voor genezend voedsel kan worden geblokkeerd, waardoor verschillende handmatige eliminatiegidsen praktisch nutteloos zijn.
Deze bijzondere infectie zal het opzetten van een Windows-oplossing voor zichzelf, naar aanleiding van de uitgevoerde veiligheidsevaluatie zijn de nakoming van activiteiten daadwerkelijk geobserveerd:
. Tijdens de mijnwerkerprocedures kan de aangesloten malware verbinding maken met reeds draaiende Windows-services en geïnstalleerde applicaties van derden. Hierdoor ontdekken de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een ander proces.
| Naam | Miner.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware om Miner.exe te detecteren en te verwijderen |

Dit soort malware-infecties zijn bijzonder betrouwbaar bij het uitvoeren van geavanceerde opdrachten als ze zo zijn ingesteld. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers alle soorten gevaarlijke gewoonten kunnen orkestreren. Onder de geprefereerde voorbeelden is de wijziging van het Windows-register – Wijzigingen die door het besturingssysteem zijn verbonden, kunnen leiden tot ernstige verstoringen van de efficiëntie en het onvermogen van toegankelijkheidsoplossingen voor Windows. Afhankelijk van de omvang van de aanpassingen kan het bovendien het computersysteem volledig onbruikbaar maken. Aan de andere kant kan manipulatie van registerwaarden die behoren tot elk type gekoppelde applicaties van derden deze ondermijnen. Sommige applicaties werken mogelijk niet meer en worden helemaal niet meer vrijgegeven, terwijl andere ineens kunnen stoppen met werken.
Deze specifieke mijnwerker in zijn bestaande variant is geconcentreerd op het extraheren van de Monero-cryptocurrency met een gewijzigde versie van de XMRig CPU-mijnengine. Als de campagnes succesvol blijken te zijn, kunnen toekomstige variaties van de Miner.exe in de toekomst worden vrijgegeven. Als de malware maakt gebruik van software applicatie kwetsbaarheden te misbruiken doelhosts infecteren, het kan zijn onderdeel van een gevaarlijke co-infectie met ransomware en ook Trojaanse paarden.
Het verwijderen van Miner.exe wordt sterk aangeraden, aangezien u de kans grijpt niet alleen enorme elektriciteitskosten te betalen als het op uw pc draait, De mijnwerker kan echter ook verschillende andere ongewenste taken uitvoeren en zelfs uw pc permanent beschadigen.
Miner.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Miner.exe te verwijderen
STAP 5. Miner.exe verwijderd!
video Guide: Hoe GridinSoft Anti-Malware te gebruiken voor het verwijderen van Miner.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Miner.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Miner.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Miner.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Miner.exe”.







