Een gloednieuw, echt gevaarlijk cryptocurrency mijnwerkervirus is geïdentificeerd door beveiligingsonderzoekers. de malware, riep Zoek.exe kunnen besmetten doel patiënten met behulp van een selectie van methoden. Het belangrijkste idee achter de Find.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computers van doelen om Monero-tokens bij patiënten te krijgen’ kosten. Het resultaat van deze mijnwerker zijn de verhoogde elektriciteitskosten en ook als u het voor langere tijd verlaat, kan Find.exe zelfs de componenten van uw computersysteem beschadigen.
Zoek.exe: distributiemethoden
De Zoek.exe malware toepassingen 2 voorkeursmethoden die worden gebruikt om besmetten computer doelen:
- Payload Levering door middel van Prior Infecties. Als een oudere Find.exe-malware wordt ingezet op de getroffen systemen, kan deze zichzelf onmiddellijk upgraden of een nieuwere variant downloaden en installeren. Dit is mogelijk via de ingebouwde upgrade-opdracht die de release verkrijgt. Dit wordt gedaan door te linken naar een bepaalde vooraf gedefinieerde hacker-gecontroleerde server die de malwarecode geeft. De gedownloade infectie krijgt zeker de naam van een Windows-service en wordt in het “%systeem% temp” plaats. Vitale residentiële of commerciële eigendommen en ook lopende systeemarrangementen worden gewijzigd om een meedogenloze en ook stille infectie mogelijk te maken.
- Software programma Kwetsbaarheid Exploits. De meest recente variant van de Find.exe-malware is gevonden om door sommige ondernemingen te worden veroorzaakt, bekend om het feit dat het wordt gebruikt bij de aanvallen met ransomware. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De aanslagen worden geautomatiseerd door een hacker bestuurde structuur die zoekt naar als de poort open. Als dit probleem is opgelost, zal het de oplossing controleren en ook de details ervan ophalen, inclusief elk type versie en ook configuratie-informatie. Ventures en populaire mixen van gebruikersnaam en wachtwoord kunnen worden gedaan. Wanneer de manipulatie wordt veroorzaakt tegen de kwetsbare code, wordt de mijnwerker samen met de achterdeur ingezet. Dit zal het een dubbele infectie.
Naast deze technieken kunnen ook andere benaderingen worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die op een SPAM-achtige manier in het groot worden verzonden en vertrouwen op sociale ontwerpmethoden om de doelwitten perplex te laten geloven dat ze daadwerkelijk een bericht hebben ontvangen van een legitieme oplossing of bedrijf. De virusdocumenten kunnen rechtstreeks worden verbonden of in het lichaamsmateriaal in multimediamateriaal of tekstlinks worden ingevoegd.
De boosdoeners kunnen ook destructieve bestemmingspagina's produceren die kunnen leiden tot het downloaden en installeren van webpagina's door leveranciers, software download websites, alsmede diverse andere veelgebruikte locaties. Wanneer ze domeinnamen gebruiken die lijken op legitieme adressen en ook beveiligingscertificaten gebruiken, kunnen de klanten ertoe worden aangezet om met hen in contact te komen. In veel gevallen kan alleen het openen ervan de mijnwerker-infectie veroorzaken.
Een aanvullende benadering zou zeker zijn om transportaanbieders te gebruiken die kunnen worden verspreid met behulp van die methoden of met behulp van netwerken voor het delen van bestanden, BitTorrent is slechts een van de meest geprefereerde. Het wordt regelmatig gebruikt om zowel gerenommeerde softwareprogramma's als bestanden en illegale webinhoud te verspreiden. 2 van één van de meest prominente haul providers zijn de volgende::
Verschillende andere benaderingen die door de slechteriken in overweging kunnen worden genomen, zijn onder meer het gebruik van browserkapers - onveilige plug-ins die geschikt zijn gemaakt met een van de meest geprefereerde internetbrowsers. Ze worden geüpload naar de relevante databases met neppe individuele beoordelingen en ook inloggegevens van ontwerpers. In de meeste gevallen kunnen de beschrijvingen bestaan uit screenshots, videoclips en ook geavanceerde beschrijvingen die uitstekende attribuutverbeteringen en prestatie-optimalisaties beloven. Desalniettemin zal het gedrag van de getroffen webbrowsers na installatie zeker veranderen- individuen zullen zeker merken dat ze worden omgeleid naar een hacker-gecontroleerde touchdown-pagina en dat hun instellingen kunnen worden gewijzigd – de standaard webpagina, zoekmachine evenals gloednieuwe tabs pagina.
Zoek.exe: Analyse
De Find.exe-malware is een tijdloze situatie van een cryptocurrency-mijnwerker die, afhankelijk van de opstelling, een breed scala aan gevaarlijke acties kan activeren. Het belangrijkste doel is om gecompliceerde wiskundige taken uit te voeren die zullen profiteren van de aangeboden systeembronnen: processor, GPU, geheugen evenals harde schijf ruimte. De manier waarop ze werken, is door verbinding te maken met een speciale server genaamd mijnbouwzwembad van waaruit de opgeroepen code wordt gedownload en geïnstalleerd. Zo snel als een van de taken is gedownload zal worden begonnen in een keer, talrijke gevallen kan worden uitgevoerd in een keer. Wanneer een aangeboden taak is voltooid, wordt er nog een gedownload en op zijn plaats geïnstalleerd en de lus zal zeker doorgaan totdat de computer wordt uitgeschakeld, de infectie wordt verwijderd of er vindt een soortgelijke gebeurtenis plaats. Cryptogeld zal beloond worden naar de correctionele controllers (hacken team of een eenzame cyberpunk) rechtstreeks naar hun portemonnee.
Een onveilige eigenschap van deze categorie malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en ook de doelcomputer virtueel zinloos kunnen maken totdat het gevaar daadwerkelijk volledig is geëlimineerd. De meesten van hen hebben een consistente installatie die ze echt uitdagend te elimineren maakt. Deze commando's zullen zeker aanpassingen aan laars alternatieven, configuratiebestanden en Windows-registerwaarden die ervoor zorgen dat de Find.exe-malware automatisch start zodra het computersysteem wordt ingeschakeld. De toegankelijkheid van voedselkeuzes en keuzes voor recuperatie kan worden geblokkeerd, wat veel handmatige verwijderingsoverzichten biedt die praktisch zinloos zijn.
Deze specifieke infectie zal zeker een Windows-oplossing voor zichzelf configureren, naar aanleiding van de uitgevoerde analyse Bescherming ther volgende acties zijn waargenomen:
. Tijdens de mijnwerkzaamheden kan de bijbehorende malware zich hechten aan Windows-services die momenteel worden uitgevoerd en aan applicaties van derden. Hierdoor zien de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een andere procedure.
| Naam | Zoek.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware om Find.exe te detecteren en te verwijderen |
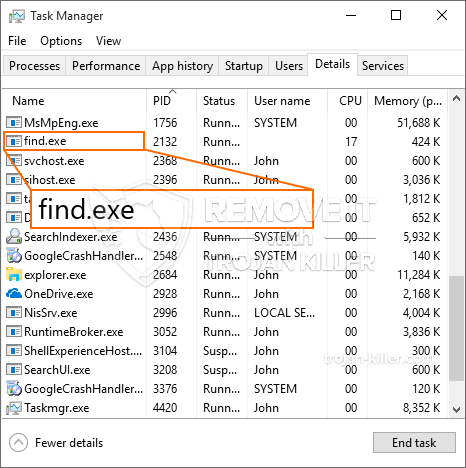
id =”82513″ align =”aligncenter” width =”600″] Zoek.exe
Zoek.exe
Dit soort malware-infecties zijn specifiek betrouwbaar bij het uitvoeren van geavanceerde commando's als zo geconfigureerd. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers alle soorten schadelijke acties kunnen beheren. Onder de prominente voorbeelden is de wijziging van het Windows-register – Wijzigingsreeksen gerelateerd aan het besturingssysteem kunnen leiden tot grote efficiëntieverstoringen en het niet kunnen gebruiken van Windows-services. Afhankelijk van de omvang van de wijzigingen kan het het computersysteem bovendien volledig zinloos maken. Aan de andere kant kan manipulatie van registerwaarden die behoren tot geïnstalleerde applicaties van derden deze ondermijnen. Sommige applicaties kunnen te kort schieten om helemaal te introduceren, terwijl andere onverwachts kunnen stoppen met werken.
Deze specifieke mijnwerker in zijn huidige versie is geconcentreerd op het extraheren van de Monero-cryptocurrency met een gewijzigde versie van de XMRig CPU-mijnengine. Als de campagnes daarna succesvol blijken te zijn, kunnen toekomstige varianten van Find.exe in de toekomst worden geïntroduceerd. Omdat de malware gebruik maakt van gevoeligheid van softwareprogramma's om doelhosts te infecteren, Het kan deel uitmaken van een onveilige co-infectie met ransomware en ook Trojaanse paarden.
Verwijdering van Find.exe wordt sterk aangeraden, aangezien u het risico loopt niet alleen een enorme elektriciteitsrekening te krijgen als deze werkt op uw COMPUTER, de mijnwerker kan er echter ook andere ongewenste activiteiten op uitvoeren en zelfs uw pc permanent beschadigen.
Find.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Find.exe te verwijderen
STAP 5. Find.exe verwijderd!
video Guide: Hoe GridinSoft Anti-Malware te gebruiken voor het verwijderen van Find.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Zoek.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Zoek.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Zoek.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Zoek.exe”.