Een nieuw, extreem gevaarlijke cryptocurrency-mijnwerkerinfectie is daadwerkelijk opgemerkt door beveiligingsonderzoekers. de malware, riep Cpuminer-amd.exe kan doelwitpatiënten infecteren door gebruik te maken van een aantal manieren. De essentie achter de Cpuminer-amd.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten op de computers van patiënten te gebruiken om Monero-symbolen te verkrijgen tegen kosten van slachtoffers. Het resultaat van deze mijnwerker is de verhoogde elektriciteitsrekening en als u het voor langere tijd verlaat, kan Cpuminer-amd.exe ook uw computersysteemelementen beschadigen.
Cpuminer-amd.exe: distributiemethoden
De Cpuminer-amd.exe malware maakt gebruik van 2 prominente benaderingen die worden gebruikt om computerdoelen te besmetten:
- Payload Levering via Prior Infecties. Als een oudere Cpuminer-amd.exe-malware op de doelsystemen wordt ingezet, kan deze zichzelf onmiddellijk bijwerken of een nieuwere versie downloaden. Dit is mogelijk via de ingebouwde update-opdracht die de release verkrijgt. Dit wordt gedaan door aansluiting op een speciaal vooraf bepaald hacker-gecontroleerde server die de malware code geeft. Het gedownloade virus krijgt de naam van een Windows-service en wordt in de “%systeem% temp” plaats. Essentiële woningen en configuratiebestanden van het besturingssysteem worden gewijzigd om een consistente en stille infectie mogelijk te maken.
- Software programma Kwetsbaarheid Exploits. Er is ontdekt dat de nieuwste variant van de Cpuminer-amd.exe-malware wordt veroorzaakt door enkele ondernemingen, in de volksmond bekend om te worden gebruikt in de ransomware-aanvallen. De infecties worden gedaan door zich te richten geopend diensten met behulp van de TCP-poort. De aanvallen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. Als aan dit probleem is voldaan, wordt de oplossing gescand en worden er details over opgehaald, inclusief elke soort versie en ook configuratie-informatie. Ventures evenals populaire gebruikersnaam en wachtwoord combinaties kunnen worden gedaan. Wanneer de manipulatie wordt geactiveerd tegen de gevoelige code, wordt de mijnwerker samen met de achterdeur ingezet. Dit zal zeker bieden een dubbele infectie.
Naast deze methoden kunnen ook andere benaderingen worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die in bulk op een SPAM-achtige manier worden verzonden, en ze kunnen ook vertrouwen op trucs voor sociaal ontwerp om de slachtoffers te laten denken dat ze een bericht hebben ontvangen van een legitieme dienst of bedrijf. De infectiedocumenten kunnen direct worden bijgevoegd of in de hoofdtekst worden geplaatst in multimedia-inhoud of berichtlinks.
De criminelen kunnen bovendien schadelijke landingspagina's maken die zich kunnen voordoen als download- en installatiepagina's van leveranciers, downloadsites voor softwareprogramma's en ook andere vaak bezochte plaatsen. Wanneer ze een vergelijkbaar ogend domein gebruiken voor gerenommeerde adressen en veiligheidscertificeringen, kunnen de individuen gedwongen worden om contact met hen op te nemen. In sommige gevallen alleen het openen van hen kan de mijnwerker een infectie veroorzaken.
Een aanvullende benadering zou zeker zijn om payload-serviceproviders te gebruiken die kunnen worden verspreid met behulp van de bovengenoemde methoden of met behulp van netwerken voor het delen van bestanden., BitTorrent is een van de meest prominente. Het wordt regelmatig gebruikt om zowel legitieme softwareapplicaties als bestanden en illegale webinhoud te verspreiden. 2 van de meest vooraanstaande vervoerders zijn de volgende:
Verschillende andere methoden die door de wetsovertreders kunnen worden overwogen, zijn het gebruik van internetbrowserkapers - gevaarlijke plug-ins die compatibel zijn gemaakt met een van de meest prominente internetbrowsers. Ze worden gepubliceerd in de juiste repositories met valse individuele evaluaties en ontwikkelaarskwalificaties. In de meeste gevallen kunnen de beschrijvingen screenshots bevatten, video's en uitgebreide samenvattingen met uitstekende functieverbeteringen en efficiëntie-optimalisaties. Desalniettemin zal na installatie het gedrag van de getroffen webbrowsers zeker veranderen- klanten zullen merken dat ze zeker zullen worden omgeleid naar een door een hacker gecontroleerde landingspagina en dat hun instellingen kunnen worden gewijzigd – de standaard webpagina, internet zoekmachine en gloednieuwe tabs pagina.

Cpuminer-amd.exe: Analyse
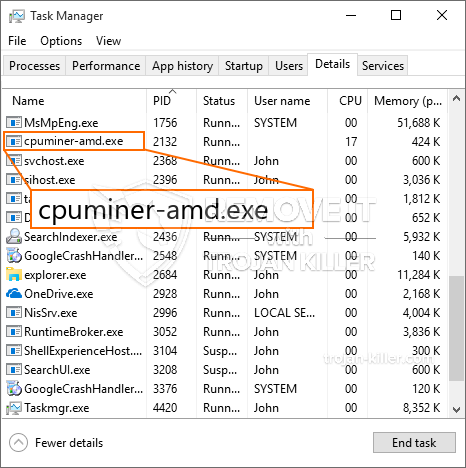
De Cpuminer-amd.exe-malware is een klassieke instantie van een cryptocurrency-mijnwerker die, afhankelijk van de configuratie, een breed scala aan gevaarlijke activiteiten kan activeren. Het primaire doel is om ingewikkelde wiskundige taken uit te voeren die zeker zullen profiteren van de aangeboden systeembronnen: processor, GPU, geheugen en harde schijf ruimte. De methode die ze gebruiken is door verbinding te maken met een unieke webserver genaamd mining pool waar de benodigde code wordt gedownload. Zodra een van de taken is gedownload, zal deze zeker gelijktijdig worden gestart, tal van omstandigheden kan worden gegaan voor zodra. Wanneer een aangeboden taak is voltooid, wordt er nog een gedownload en op zijn locatie geïnstalleerd, en de lus zal zeker doorgaan totdat de computer wordt uitgeschakeld, de infectie is geëlimineerd of nog een vergelijkbare gebeurtenis plaatsvindt. Cryptogeld zal zeker worden gecompenseerd naar de correctionele controllers (hacken groep of een enkele cyberpunk) direct naar hun begrotingen.
Een schadelijk kenmerk van deze groep malware is dat vergelijkbare voorbeelden alle systeembronnen kunnen gebruiken en de computer van het slachtoffer praktisch onbruikbaar kunnen maken totdat het gevaar daadwerkelijk volledig is verwijderd. De meeste bevatten een hardnekkige aflevering waardoor ze erg moeilijk te verwijderen zijn. Deze opdrachten zullen zeker wijzigingen aanbrengen in opstartalternatieven, rangschikkingsgegevens en Windows-registerwaarden die ervoor zorgen dat de Cpuminer-amd.exe-malware automatisch start zodra de computer wordt ingeschakeld. De toegang tot recuperatiemenu's en ook opties kan worden belemmerd, waardoor talloze handmatige verwijderingsoverzichten bijna waardeloos zijn.
Deze specifieke infectie zal zeker de configuratie van een Windows-service voor zichzelf, het naleven van de uitgevoerde veiligheidsanalyse en het daadwerkelijk naleven van activiteiten is waargenomen:
. Tijdens de miner-procedures kan de aangesloten malware een koppeling maken met de momenteel actieve Windows-services en ook met geïnstalleerde applicaties van derden. Hierdoor zien de systeembeheerders mogelijk niet dat de bronpartijen uit een andere procedure komen.
| Naam | Cpuminer-amd.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware om Cpuminer-amd.exe te detecteren en te verwijderen |

Dit soort malware-infecties zijn bijzonder efficiënt in het uitvoeren van innovatieve opdrachten als ze zo zijn ingesteld. Ze zijn gebaseerd op een modulaire structuur die de criminele controleurs in staat stelt om allerlei soorten onveilige gewoonten te orkestreren. Een van de favoriete gevallen is de wijziging van het Windows-register – aanpassingsstrings die door het besturingssysteem zijn verbonden, kunnen grote prestatieonderbrekingen veroorzaken en ook het onvermogen om toegang te krijgen tot Windows-services. Vertrouwend op het scala aan aanpassingen kan het het computersysteem ook volkomen zinloos maken. Aan de andere kant kan aanpassing van registerwaarden afkomstig van door derden geïnstalleerde applicaties deze saboteren. Sommige applicaties kunnen te kort schieten om volledig te starten, terwijl andere plotseling kunnen stoppen met werken.
Deze bepaalde mijnwerker in zijn huidige variant is geconcentreerd op het delven van de Monero-cryptocurrency met een gewijzigde versie van de XMRig CPU-mijnengine. Als de campagnes effectief blijken, kunnen toekomstige versies van Cpuminer-amd.exe in de toekomst worden gelanceerd. Als de malware maakt gebruik van software applicatie kwetsbaarheden te misbruiken doelhosts besmetten, Het kan deel uitmaken van een gevaarlijke co-infectie met ransomware en ook Trojaanse paarden.
Verwijdering van Cpuminer-amd.exe wordt sterk aangeraden, aangezien u de kans loopt niet alleen hoge elektriciteitskosten te betalen als het op uw pc werkt, maar de mijnwerker kan er ook andere ongewenste taken op uitvoeren en uw pc permanent beschadigen.
Cpuminer-amd.exe verwijderingsproces
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” knop om Cpuminer-amd.exe te verwijderen
STAP 5. Cpuminer-amd.exe verwijderd!
video Guide: Hoe GridinSoft Anti-Malware te gebruiken voor het verwijderen van Cpuminer-amd.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Cpuminer-amd.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Cpuminer-amd.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Cpuminer-amd.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Cpuminer-amd.exe”.







