브랜드 새로운, 매우 위험한 암호 화폐 채굴 기 감염이 실제로 안전 과학자들에 의해 감지되었습니다.. 악성 코드, 라고 ZM.exe 다양한 방법을 이용하여 대상 환자를 오염시킬. ZM.exe 광부의 기본 아이디어는 피해자의 비용으로 Monero 기호를 획득하기 위해 피해자의 컴퓨터에서 암호 화폐 광부 작업을 활용하는 것입니다.. The end result of this miner is the elevated electrical energy expenses and also if you leave it for longer time periods ZM.exe might also harm your computers components.
ZM.exe: 배포 방법
그만큼 ZM.exe 악성 코드가 이용하는 2 컴퓨터 목표를 감염하는 데 사용되는 인기있는 방법:
- 이전 감염을 통해 페이로드 배달. If an older ZM.exe malware is deployed on the target systems it can automatically update itself or download a more recent variation. 이것은 릴리스를 얻는 통합 업그레이드 명령을 통해 가능합니다. 이것은 악성 코드를 공급하는 미리 정의 된 특정 해커 제어 서버에 연결하면됩니다. 다운로드 한 바이러스는 Windows 솔루션의 이름을 획득하고 “%시스템 % 온도” 위치. 끊임없는 자동 감염을 허용하기 위해 시스템 속성 설정 및 실행 중 필수 속성이 변환됩니다..
- 소프트웨어 응용 프로그램 취약점 악용. The most current variation of the ZM.exe malware have been discovered to be triggered by the some exploits, 랜섬웨어 공격에 사용되는 것으로 유명. 감염은 TCP 포트를 통해 공개 서비스를 대상으로 수행됩니다. 공격은 포트가 열려있는 경우 조회 해커 제어 프레임 워크에 의해 자동화. 이 조건이 충족되면 확실히 서비스를 스캔하고 관련 세부 정보를 검색합니다., 배치 정보뿐만 아니라 변형의 임의의 유형으로 구성된. 공격뿐만 아니라 선호하는 이름뿐만 아니라 암호 믹스 수행 할 수 있습니다. 사용하기 쉬운 코드와 비교할 때 백도어 외에도 광부가 확실히 배포됩니다.. 이것은 이중 감염을 선물 할 것이다.
이러한 기술 이외에도 다양한 다른 기술을 사용할 수 있습니다. SPAM과 같은 방식으로 대량으로 발송되는 피싱 전자 메일을 통해 광부를 배포 할 수있을뿐만 아니라 사회 설계 기술을 통해 피해자가 합법적 인 서비스 또는 회사로부터 메시지를 받았다고 믿도록 당황하게합니다.. 바이러스 파일은 멀티미디어 컨텐츠 또는 메시지 웹 링크의 본문 컨텐츠에 직접 첨부하거나 삽입 할 수 있습니다..
불법 행위자는 공급 업체 다운로드 및 설치 웹 페이지를 가장 할 수있는 유해한 방문 페이지를 추가로 생성 할 수 있습니다., 소프트웨어 응용 프로그램 다운로드 웹 사이트 및 기타 정기적으로 액세스하는 장소. 고객이 유사한 도메인 이름을 합법적 인 주소 및 안전 및 보안 인증에 활용하면 고객과 통신하도록 설득 될 수 있습니다. 때로는 광부 감염을 유발할 수를 여는.
하나 이상의 기술은 분명히 위에서 언급 한 방법을 사용하거나 데이터 공유 네트워크를 사용하여 확산 될 수있는 운반 캐리어를 사용하는 것입니다., 비트 토런트는 가장 선호하는 것들 중 하나 중 하나입니다. 평판이 좋은 소프트웨어 응용 프로그램과 파일 및 해적 자료를 모두 분산시키는 데 정기적으로 사용됩니다.. 2 가장 유명한 페이로드 서비스 제공 업체는 다음과 같습니다.:
법률 위반자가 고려할 수있는 다양한 기술은 인터넷 브라우저 하이재커를 사용하는 것입니다. 가장 유명한 웹 브라우저에 적합한 유해한 플러그인. 그들은 프로그래머 자격뿐만 아니라 가짜 고객 평가와 함께 적절한 리포지토리에 제출됩니다. 많은 경우에 대한 설명은 스크린 샷을 포함 할 수있다, 비디오 및 고급 요약은 효율성 최적화뿐만 아니라 뛰어난 기능 개선을 장려합니다. 그러나 설치시 영향을받는 웹 브라우저의 습관은 확실히 바뀔 것입니다- 고객은 해커가 제어하는 터치 다운 페이지로 다시 라우팅되고 설정이 변경 될 수 있음을 알게됩니다 – 기본 웹 페이지, 인터넷 검색 엔진과 새로운 탭 웹 페이지.
ZM.exe: 분석
The ZM.exe malware is a timeless situation of a cryptocurrency miner which depending on its configuration can create a wide variety of unsafe actions. Its major objective is to carry out intricate mathematical tasks that will capitalize on the available system sources: CPU, GPU, 메모리뿐만 아니라 하드 드라이브 공간. The method they work is by linking to a special web server called mining pool from where the required code is downloaded and install. 즉시 작업의 하나로서 확실히 한 번에 시작됩니다 다운로드, 여러 상황이 언제 실행될 수 있습니다.. When a provided job is finished one more one will be downloaded in its place as well as the loop will certainly continue until the computer is powered off, 감염이 제거 쪘거나 한 번 더 비슷한 행사가 이루어진다. 암호 화폐 확실히 범죄 컨트롤러에 보상한다 (해킹 팀 또는 고독한 해커) 바로 자신의 지갑에.
An unsafe feature of this group of malware is that examples similar to this one can take all system resources as well as virtually make the victim computer system pointless up until the threat has been totally gotten rid of. The majority of them include a relentless setup which makes them truly difficult to remove. 이 명령은 선택도 변화를 만들 것입니다, setup data and also Windows Registry values that will make the ZM.exe malware start instantly once the computer is powered on. Access to healing food selections as well as choices might be obstructed which makes several hands-on removal overviews practically useless.
이 특정 감염 자체에 대한 Windows 서비스를 구성합니다, complying with the conducted safety and security analysis ther complying with activities have actually been observed:
. During the miner operations the linked malware can attach to already running Windows services and third-party mounted applications. 그렇게함으로써 시스템 관리자는 자원 로트가 다른 프로세스에서 비롯된 것을 관찰하지 못할 수 있습니다..
| 이름 | ZM.exe |
|---|---|
| 범주 | 트로이 사람 |
| 하위 카테고리 | 암호 화폐 광부 |
| 위험 | 높은 CPU 사용, 인터넷 속도 감소, PC 충돌 및 정지 등. |
| 주목적 | 사이버 범죄자 돈을 만들려면 |
| 분포 | 급류, 무료 게임, 금이 앱, 이메일, 의심스러운 웹 사이트, 악용 |
| 제거 | 설치 GridinSoft 안티 멀웨어 to detect and remove ZM.exe |
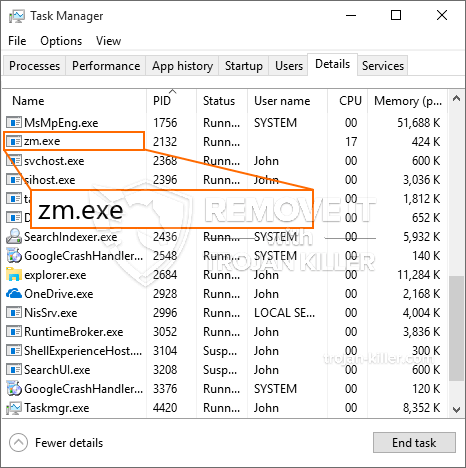
ID =”82228″ 정렬 =”aligncenter” 폭 =”600″]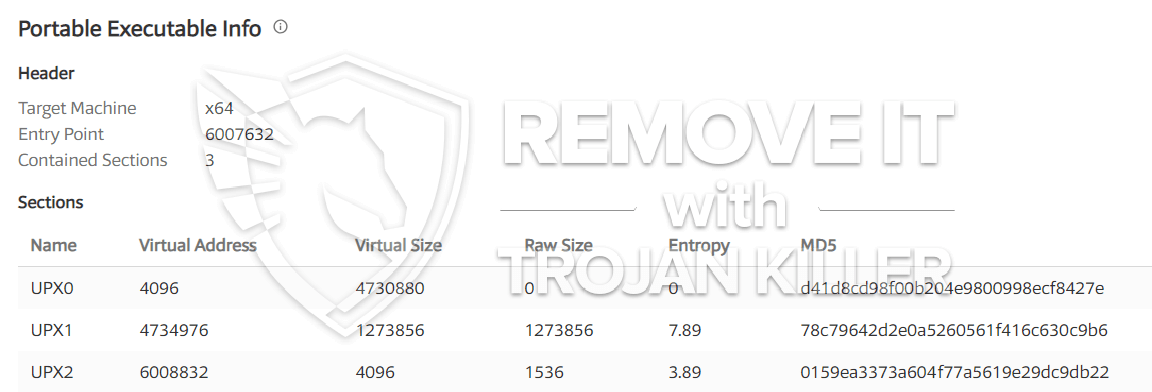 ZM.exe
ZM.exe
These type of malware infections are specifically effective at accomplishing sophisticated commands if set up so. They are based upon a modular framework enabling the criminal controllers to orchestrate all type of hazardous behavior. 인기있는 인스턴스 중 하나는 윈도우 레지스트리의 변경입니다 – modifications strings associated by the operating system can create serious efficiency interruptions and the failure to accessibility Windows solutions. Depending upon the scope of adjustments it can additionally make the computer completely unusable. 반면에 타사 설정 응용 프로그램에서 오는 레지스트리 값 조정은 이를 방해할 수 있습니다.. Some applications might stop working to release completely while others can unexpectedly quit working.
This certain miner in its existing variation is concentrated on extracting the Monero cryptocurrency including a changed version of XMRig CPU mining engine. If the projects confirm effective then future versions of the ZM.exe can be released in the future. 악성 코드는 오염물 대상 호스트에 소프트웨어 susceptabilities를 사용하기 때문에, 또한 랜섬웨어 및 트로이 목마와 유해 공동 감염의 구성 요소가 될 수 있습니다.
Elimination of ZM.exe is highly suggested, given that you risk not just a huge electricity bill if it is running on your COMPUTER, yet the miner may likewise execute other undesirable tasks on it as well as even harm your COMPUTER permanently.
ZM.exe removal process
단계 1. 가장 먼저, 당신은 GridinSoft 안티 악성 코드를 다운로드하고 설치해야.
단계 2. 그럼 당신은 선택해야 “빠른 검사” 또는 “전체 검사”.
단계 3. 컴퓨터를 스캔 실행
단계 4. 스캔이 완료되면, 당신은 클릭해야 “대다” button to remove ZM.exe
단계 5. ZM.exe Removed!
비디오 가이드: How to use GridinSoft Anti-Malware for remove ZM.exe
방법으로 재감염되는 PC를 방지하기 위해 “ZM.exe” 앞으로.
탐지하고 차단 fileless 악성 코드 수있는 강력한 안티 바이러스 솔루션은 당신이 필요하다! 기존의 솔루션은 바이러스 정의를 기반으로 악성 코드를 탐지, 따라서 그들은 종종 감지 할 수 없습니다 “ZM.exe”. GridinSoft 안티 - 악성 코드는 다음과 같은 fileless 악성 코드를 포함한 모든 유형의 맬웨어에 대한 보호를 제공 “ZM.exe”. GridinSoft 안티 - 악성 코드는 제로 데이 악성 코드를 포함한 모든 알 수없는 파일을 차단하는 클라우드 기반의 행동 분석을 제공합니다. 이러한 기술은 감지하고 완전히 제거 할 수 있습니다 “ZM.exe”.