브랜드 새로운, 매우 유해한 암호 화폐 광부 바이러스는 안전과 보안 과학자들에 의해 발견되었다. 악성 코드, 라고 CoreSync.exe 방법의 범위를 활용하여 대상 환자를 감염시킬 수 있습니다. CoreSync.exe 광부 뒤에 주요 아이디어는 Monero을 얻기 위해 피해자의 컴퓨터 시스템에 채택 된 암호 화폐 광부 작업이다는 목표 비용으로 토큰. 이 광부의 결과는 전기 에너지 비용을 발생하고 시간의 긴 시간 동안 그것을두고 경우도 CoreSync.exe은 또한 당신의 컴퓨터 구성 요소에 손상을 줄 수.
CoreSync.exe: 배포 방법
그만큼 CoreSync.exe 악성 사용을 감염 컴퓨터 시스템을 대상으로 사용되는 두 가지 바람직한 방법은:
- 이전 감염을 사용하여 페이로드 배달. 이전 CoreSync.exe 악성 코드가 괴로워하는 시스템에 배포 된 경우 즉시 자체 또는 다운로드를 업그레이드하고 새로운 변화를 설치할 수 있습니다. 이 발사를 획득 내장 갱신 명령에 의해 가능하다. 이것은 악성 코드를 제공하는 미리 정의 된 특정 해커 제어 서버에 연결하면됩니다. 뿐만 아니라에 배치로 다운로드 된 감염은 확실히 Windows 서비스의 이름을 취득합니다 “%시스템 % 온도” 위치. 필수 건물 및 운영 체제 배치 데이터는 지속적이고 조용한 감염을 허용하기 위해 변환됩니다.
- 소프트웨어 응용 프로그램 취약점 악용. CoreSync.exe의 최신 버전은 일부 벤처 기업에 의해 트리거 될 발견 된 악성 코드, 널리 랜섬 공격을 살린 것에 대한 이해. 감염은 TCP 포트를 통해 개방형 솔루션을 대상으로 수행됩니다. 폭행은 포트가 열려있는 경우 조회 해커 제어 프레임 워크에 의해 자동화. 이 문제가 만족되면이 솔루션을 스캔하고 또한 관한 정보를 복구합니다, 변형 및 구성 데이터의 형식으로 이루어지는. 벤처뿐만 아니라 저명한 이름도 암호 믹스 할 수 있습니다. 가 위험 코드에 대한 해제 설정되어 악용하면 광부는 확실히 백도어에 추가로 발표 될 예정이다. 이것은 이중 감염을 제공 할 것입니다.
이러한 방법 외에도 다양한 방법이 물론 사용될 수있다. 광부들은 합법적 인 솔루션이나 회사에서 메시지를 받았는지 생각에 환자를 혼란스럽게하기 위해 사회 디자인 트릭에 스팸과 같은 방식으로 도매 보내도 의존하는 이메일 피싱에 의해 분산 될 수있다. 바이러스 파일은 직접 멀티미디어 컨텐츠 또는 텍스트 웹 링크의 본문 내용에 부착하거나 삽입 할 수 있습니다.
잘못을 저지른 마찬가지로 공급 업체 다운로드 웹 페이지를 가장 할 수 있습니다 악성 착륙 웹 페이지를 만들 수 있습니다, 소프트웨어 다운로드 포털 및 기타 자주 액세스 위치. 그들이 진짜 주소와도 안전 인증에 필적 보이는 도메인을 활용하면 고객은 바로 그들과 상호 작용에 설득 될 수있다. 어떤 경우에는 단순히 광부 감염을 일으킬 수를 여는.
또 하나 개의 기술은 확실히 확산 상기 기술을 활용 또는 파일 공유 네트워크를 통해 할 수있다 운반 캐리어의 사용을하는 것입니다, 비트 토런트는 가장 눈에 띄는 것 중 하나입니다. 종종 합법적 인 소프트웨어 응용 프로그램과 문서도 해적 웹 컨텐츠 모두를 배포하는 데 사용됩니다. 2 가장 선호하는 운반 서비스 제공 업체 중 하나의 다음과 같다:
범죄자에 의해 고려 될 수있는 다양한 다른 방법은 웹 브라우저를 사용하여 구성이 가장 인기있는 인터넷 브라우저와 호환 만들어 -hazardous 플러그인을 납치범. 그들은 가짜 사용자 평가뿐만 아니라 디자이너 자격과 관련 데이터베이스에 제출. 때때로 설명 스크린 샷을 포함 할 수있다, 환상적인 기능 개선 및 효율 최적화를 장려 비디오 클립과 공상 설명. 그러나 할부에 영향을받는 인터넷 브라우저의 습관은 확실히 변경됩니다- 개인은 그들이 해커 제어 방문 페이지로 리디렉션됩니다 또한 자신의 설정이 변경 될 수 있음을 발견 할 것이다 – 기본 웹 페이지, 검색 엔진 및 브랜드 새 탭 페이지.
CoreSync.exe: 분석
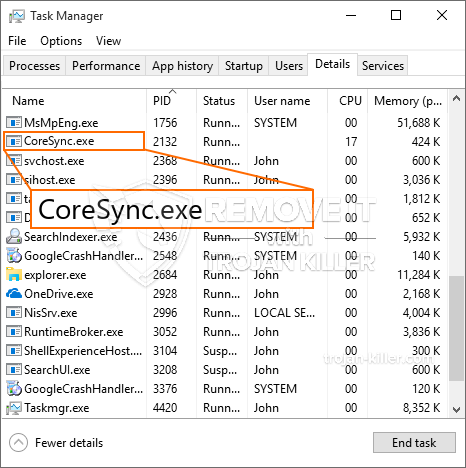
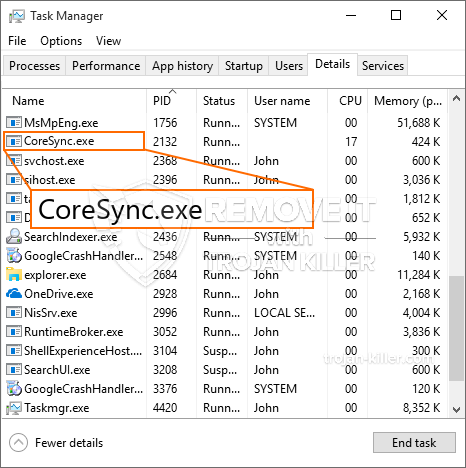
CoreSync.exe 악성 코드는 설정에 따라하는 유해 다양한 작업을 일으킬 수있는 암호 화폐 광부의 고전적인 상황. 그것의 주요 목표는 확실히 쉽게 사용 가능한 시스템 리소스를 활용합니다 복잡한 수학적 작업을 실행하는 것입니다: CPU, GPU, 메모리 및 하드 드라이브 공간. 그들이 작동 수단은 필요한 코드가 다운로드되는 고유 한 서버라는 광산 풀에 연결하는 것입니다. 으로 신속하게 작업 중 하나는 한 번에 시작됩니다 다운로드로, 다수의 인스턴스는 한 번에 수행 할 수 있습니다. 주어진 작업이 완료되면 다른 하나는 확실히 다운로드하고 그 자리에 설치하고 컴퓨터의 전원이 꺼져까지 또한 루프가 진행됩니다, 감염이 분리되었거나 또 하나 개의 유사한 이벤트가 발생. 암호 화폐는 범죄 컨트롤러에 수여됩니다 (해킹 그룹 또는 단독의 사이버 펑크) 바로 자신의 지갑에.
위험이 완전히 없애받은 때까지 악성 코드의이 범주의 안전하지 않은 기능은 물론 사실상 피해자의 컴퓨터 시스템 무의미을 모든 시스템 리소스를 취할 수있는이 같은 그 샘플입니다. 그들 대부분은 제거하기가 정말 힘든하게 영구적 인 설치 기능. 이 명령은 부팅 옵션을 변경합니다, 배치 문서뿐만 아니라 컴퓨터 시스템에 전원이 공급되면 확실히 CoreSync.exe를 만들 것입니다 Windows 레지스트리 값을 즉시 시작 악성 코드로. 또한 옵션을 식품 선택을 치유하고 접근성은 거의 효과가 다양한 수동 제거 개요를 제공하는 차단 될 수 있습니다.
이 특정 감염 자체에 대한 윈도우 솔루션을 구성한다, THER 다음과 같은 활동이 실제로 관찰 된 수행 보호 평가 준수:
광부 절차 중에 링크 된 악성 코드는 현재 Windows 서비스 및 타사 설치된 응용 프로그램을 실행에 연결할 수 있습니다. 시스템 관리자는이를 통해 알 수 없습니다 그 다른 프로세스에서 소스를 많이의 유래.
| 이름 | CoreSync.exe |
|---|---|
| 범주 | 트로이 사람 |
| 하위 카테고리 | 암호 화폐 광부 |
| 위험 | 높은 CPU 사용, 인터넷 속도 감소, PC 충돌 및 정지 등. |
| 주목적 | 사이버 범죄자 돈을 만들려면 |
| 분포 | 급류, 무료 게임, 금이 앱, 이메일, 의심스러운 웹 사이트, 악용 |
| 제거 | 설치 GridinSoft 안티 멀웨어 CoreSync.exe을 감지하고 제거합니다 |

악성 코드 감염의이 유형은 이렇게 설정 한 경우 복잡한 명령을 수행하기에 특히 효과적이다. 그들은 안전하지 않은 행동의 모든 종류를 관리 할 범죄 컨트롤러를 가능하게하는 모듈 형 구조를 기반으로. 선호하는 예 중 윈도우 레지스트리의 변경입니다 – OS에서 관련 조정 문자열은 상당한 성능 중단도 액세스 윈도우 솔루션 능력의 부족을 일으킬 수. 조정의 범위에 의존하는 것은 마찬가지로 컴퓨터 시스템을 완전히 사용할 수 없게 만들 수 있습니다. 타사에서 오는 레지스트리 worths의 반면 조정에 설치를 방해 할 수있는 응용 프로그램. 다른 사람이 갑자기 작업을 종료 할 수 있습니다 동안 일부 응용 프로그램은 아예 실행되지 않을 수 있습니다.
현재 버전에 이러한 특정 광부는 XMRig CPU 마이닝 엔진의 변화 변이 이루어진 Monero 암호 화폐의 광산에 집중. 캠페인은 CoreSync.exe의 효과적인 후 미래의 버전을 확인하면 미래에 도입 될 수. 악성 코드가 대상 호스트를 오염 소프트웨어 susceptabilities을 사용합니다으로, 이 트로이 목마뿐만 아니라 랜섬과 유해 공동 감염의 일부가 될 수 있습니다.
CoreSync.exe의 제거는 매우 좋습니다, 당신은 단지 거대한 전기 비용을 위험하기 때문에 그것은 당신의 컴퓨터에서 실행되는 경우, 그러나 광부는 추가로 그 위에 다른 바람직하지 않은 작업을 수행 할 수 있습니다뿐만 아니라 심지어 컴퓨터를 완전히 손상.
CoreSync.exe 제거 공정
단계 1. 가장 먼저, 당신은 GridinSoft 안티 악성 코드를 다운로드하고 설치해야.
단계 2. 그럼 당신은 선택해야 “빠른 검사” 또는 “전체 검사”.
단계 3. 컴퓨터를 스캔 실행
단계 4. 스캔이 완료되면, 당신은 클릭해야 “대다” CoreSync.exe을 제거하기 버튼
단계 5. CoreSync.exe 제거!
비디오 가이드: 제거 CoreSync.exe에 대한 GridinSoft 안티 악성 코드를 사용하는 방법
방법으로 재감염되는 PC를 방지하기 위해 “CoreSync.exe” 앞으로.
탐지하고 차단 fileless 악성 코드 수있는 강력한 안티 바이러스 솔루션은 당신이 필요하다! 기존의 솔루션은 바이러스 정의를 기반으로 악성 코드를 탐지, 따라서 그들은 종종 감지 할 수 없습니다 “CoreSync.exe”. GridinSoft 안티 - 악성 코드는 다음과 같은 fileless 악성 코드를 포함한 모든 유형의 맬웨어에 대한 보호를 제공 “CoreSync.exe”. GridinSoft 안티 - 악성 코드는 제로 데이 악성 코드를 포함한 모든 알 수없는 파일을 차단하는 클라우드 기반의 행동 분석을 제공합니다. 이러한 기술은 감지하고 완전히 제거 할 수 있습니다 “CoreSync.exe”.







